Implement Zero Trust Security The Internet Of Things On Aws
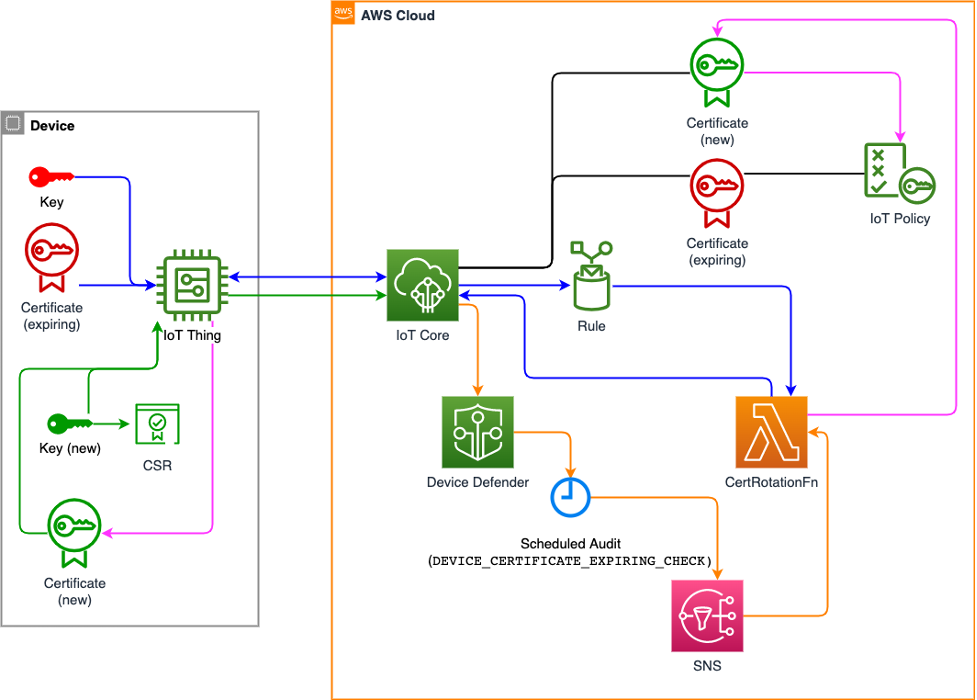
Implement Zero Trust Security The Internet Of Things On Aws One of the main challenges customers face is determining how zero trust principles can be applied to iot and how to get started with incorporating zero trust principles using aws iot. By following this guide, you can plan and deploy a zero trust architecture that not only strengthens security posture but also aligns with compliance mandates and optimizes cost management.
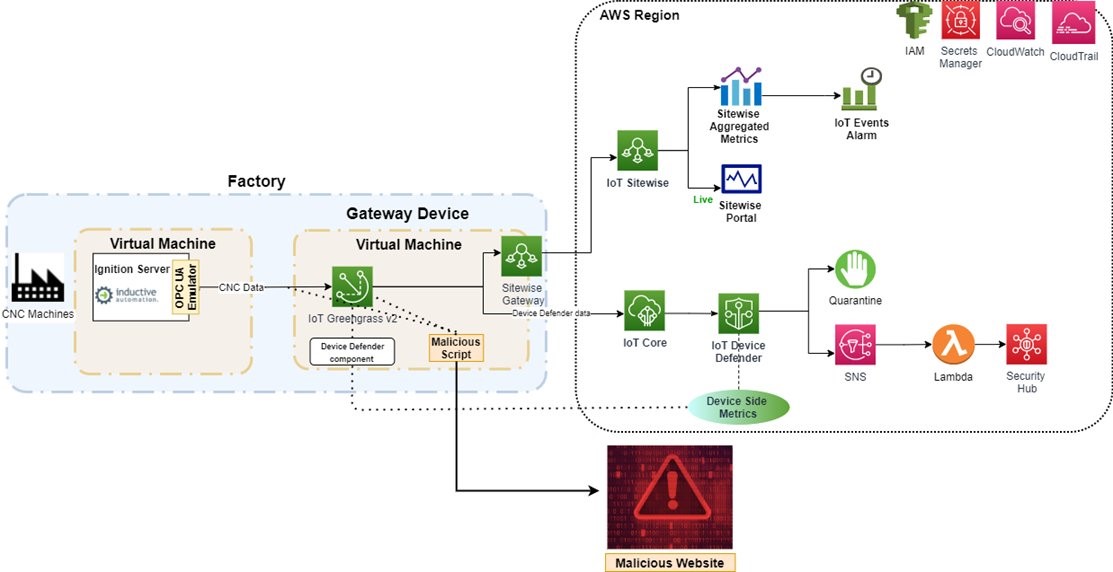
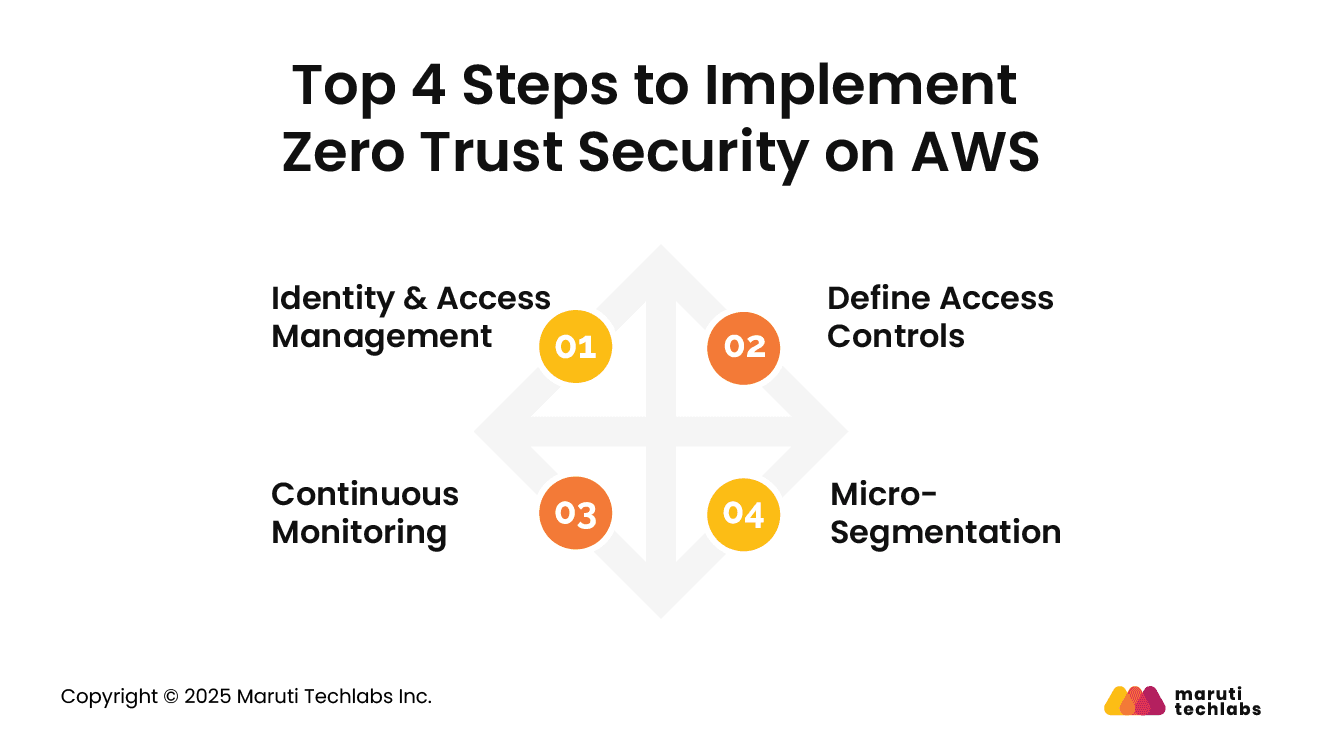
Implement Zero Trust Security The Internet Of Things On Aws Zero trust aws implementations can reduce security incidents by up to 68% according to recent industry studies. this deep dive explores how to architect and implement zero trust principles on aws, leveraging native services for identity management, network segmentation, and continuous monitoring. The zero trust model is essential for aws users, focusing on strict identity verification and continuous monitoring. by adopting this approach, organizations can enhance their security and protect sensitive data in an evolving threat landscape. Let's walk through the process of implementing zero trust architecture in aws, providing you with practical steps and best practices to enhance your cloud security posture. Learn how to implement aws zero trust security with iam, network segmentation, monitoring, and automation for maximum protection.

5 Ways Orca Security And Aws Establish Zero Trust In The Cloud Let's walk through the process of implementing zero trust architecture in aws, providing you with practical steps and best practices to enhance your cloud security posture. Learn how to implement aws zero trust security with iam, network segmentation, monitoring, and automation for maximum protection. In this blog post, we'll delve into zero trust security and its application within aws, guiding you on how to build secure architectures that are resilient to modern threats. A blog entry that addresses zero trust concepts, provider tools and implementing a zero trust architecture in aws. This guide explains how to design a strong aws security architecture using zero trust principles. the content is written in a simple, interview friendly way so you can both understand the concepts and confidently explain them in discussions. Detect and protect sensitive data, such as pii, in s3 buckets. automatically identifies vulnerabilities, unpatched software, and cves on ec2 instances.

Introducing The Aws Zero Trust Accelerator For Government Aws In this blog post, we'll delve into zero trust security and its application within aws, guiding you on how to build secure architectures that are resilient to modern threats. A blog entry that addresses zero trust concepts, provider tools and implementing a zero trust architecture in aws. This guide explains how to design a strong aws security architecture using zero trust principles. the content is written in a simple, interview friendly way so you can both understand the concepts and confidently explain them in discussions. Detect and protect sensitive data, such as pii, in s3 buckets. automatically identifies vulnerabilities, unpatched software, and cves on ec2 instances.
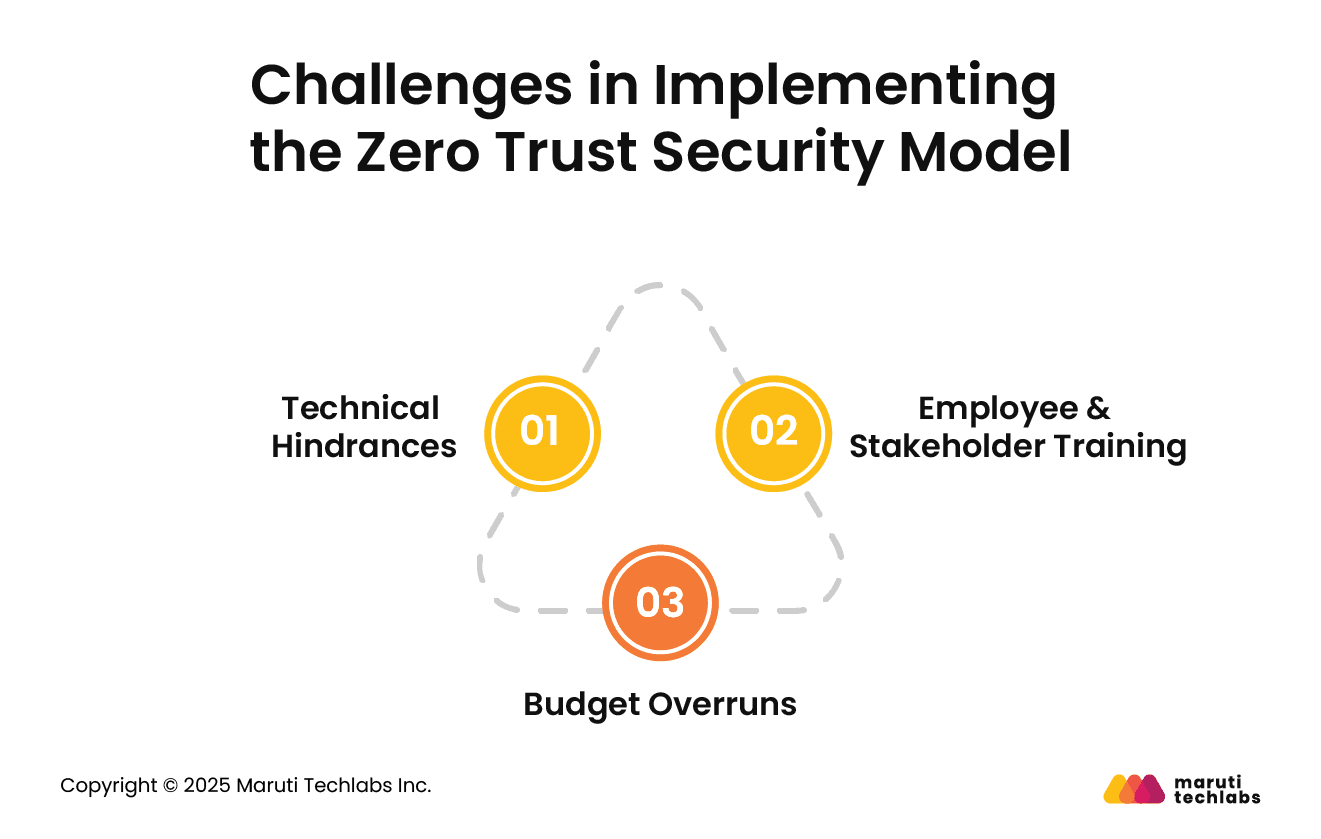
Implementing Zero Trust Security On Aws What Ctos Must Know This guide explains how to design a strong aws security architecture using zero trust principles. the content is written in a simple, interview friendly way so you can both understand the concepts and confidently explain them in discussions. Detect and protect sensitive data, such as pii, in s3 buckets. automatically identifies vulnerabilities, unpatched software, and cves on ec2 instances.
Implementing Zero Trust Security On Aws What Ctos Must Know
Comments are closed.