Implement Nist Csf Processunity
Implement Nist Csf Processunity Processunity helps organizations of all sizes implement nist csf more efficiently with out of the box control mappings, automated evidence collection, third party risk management workflows and real time reporting. This guide provides a clear and practical understanding of nist csf 2.0, helping organizations navigate its core concepts, functions, and integration steps to build a resilient and business aligned cybersecurity program.
Implement Nist Csf Processunity Open for public comment until may 6, 2026: csf 2.0 informative references quick‑start guide. this draft explains how to find, filter, and apply informative references using nist tools. Nist cybersecurity framework (csf 2.0) the nist cybersecurity framework is a voluntary, risk based framework for managing cybersecurity risk. originally developed for us critical infrastructure, csf 2.0 broadens the scope to all organisations — and is increasingly adopted by australian businesses with us supply chain relationships. Discover the value of nist csf 2.0 assessments, designed to enhance your cybersecurity posture and meet regulatory expectations effectively. This nist consultant complete training offers an end to end exploration of the nist risk management framework (rmf) and the cybersecurity framework (csf) 2.0 — preparing professionals to implement, assess, and align organizational security programs with u.s. and global standards.
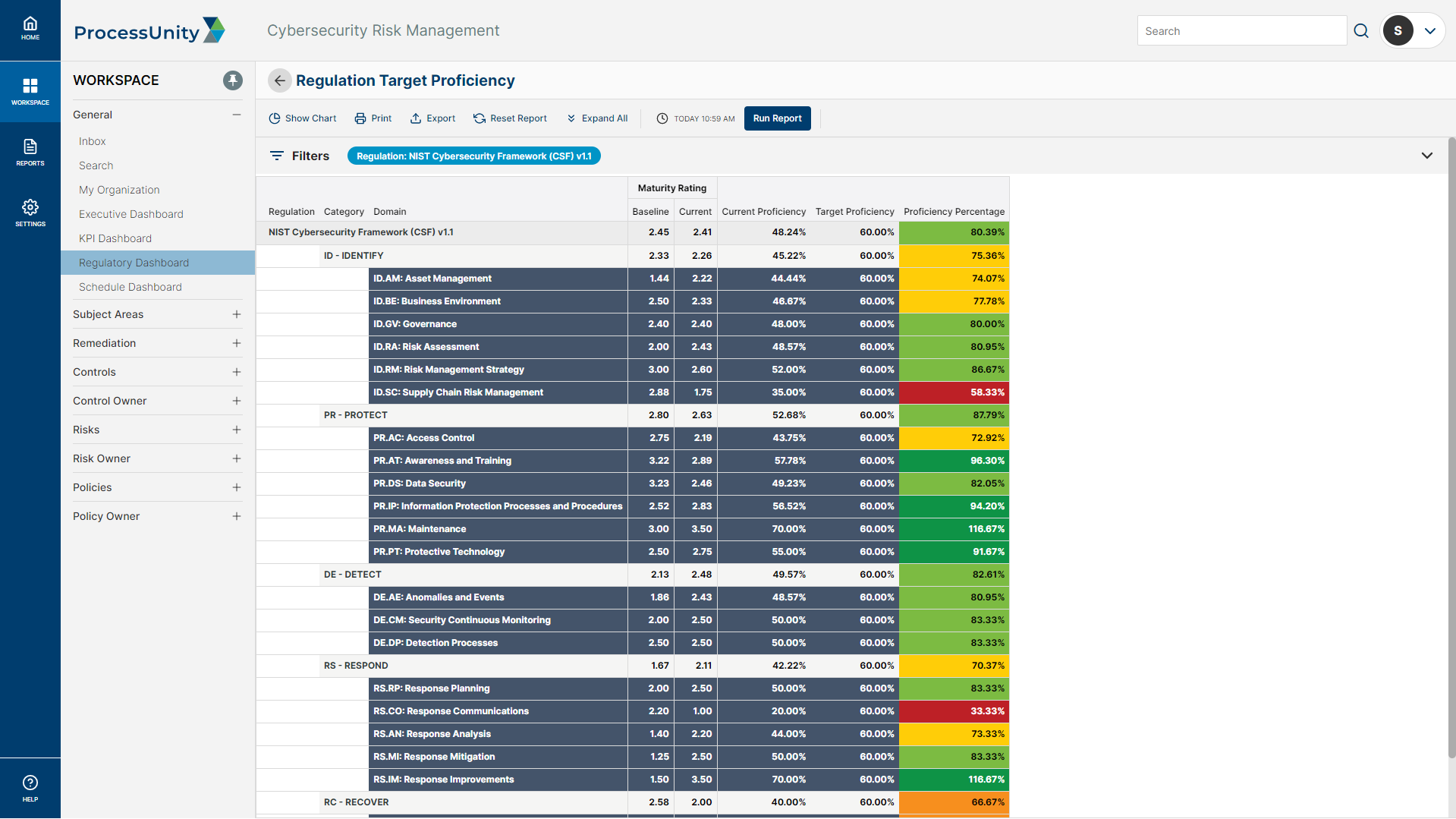
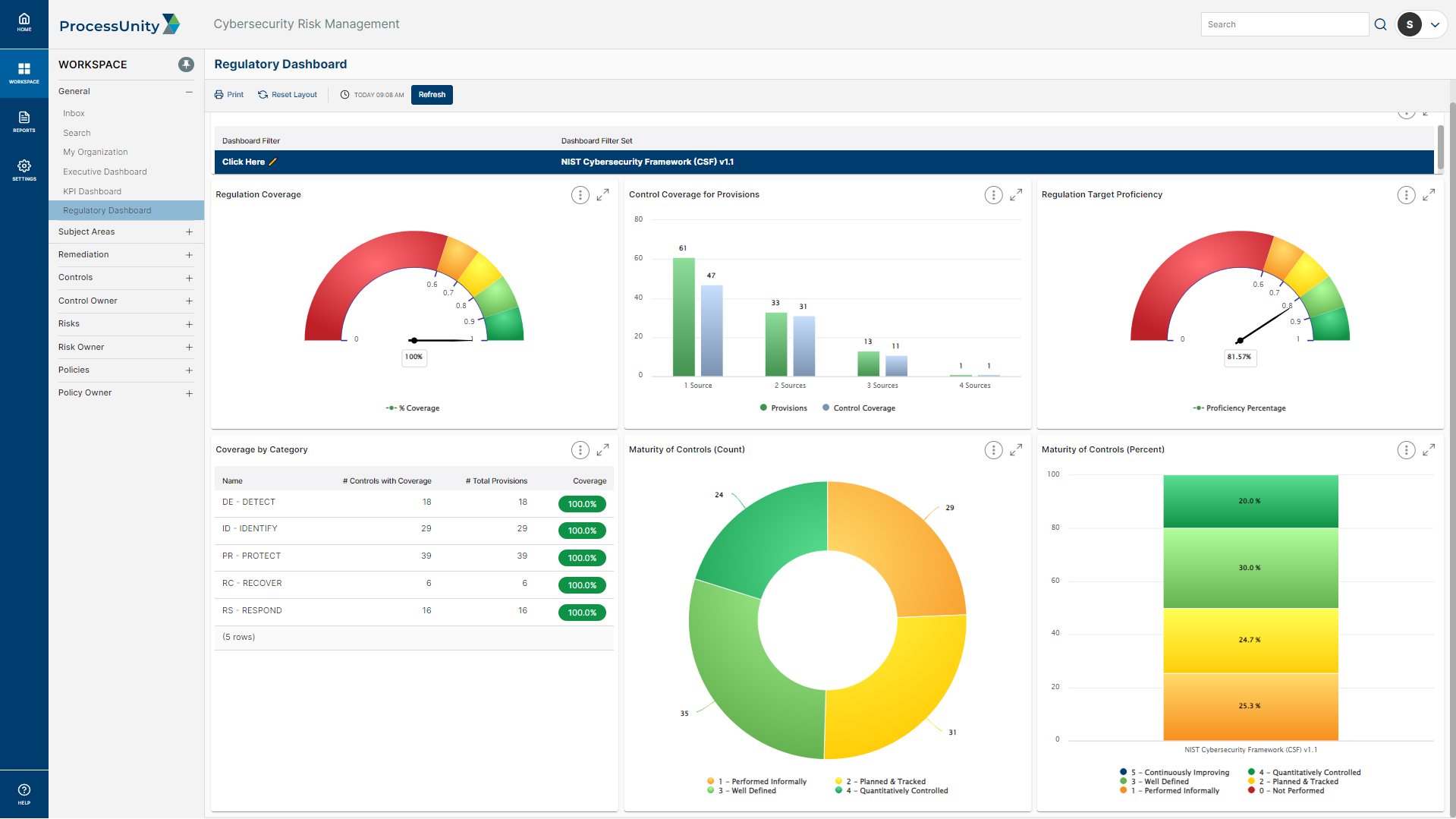
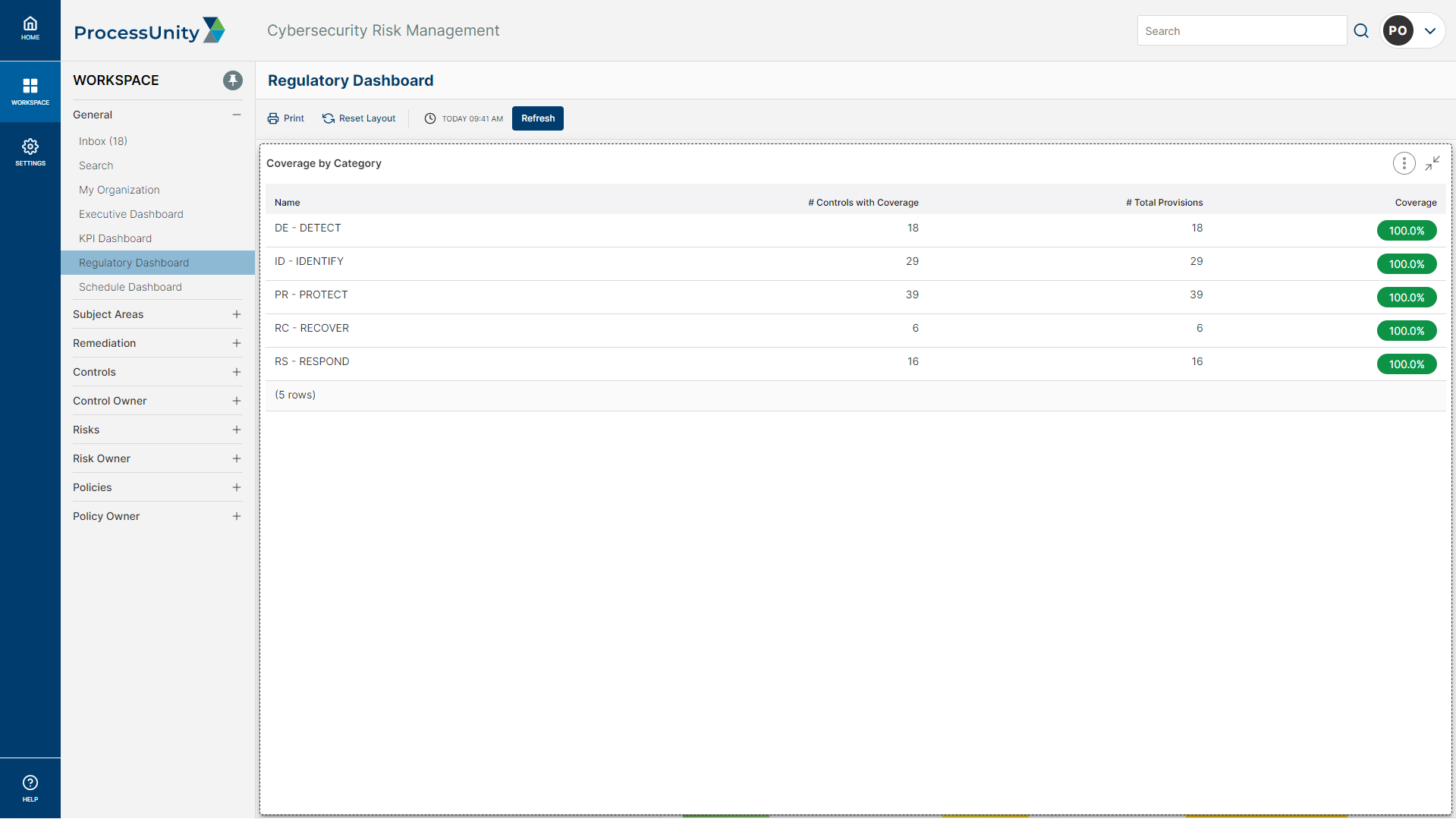
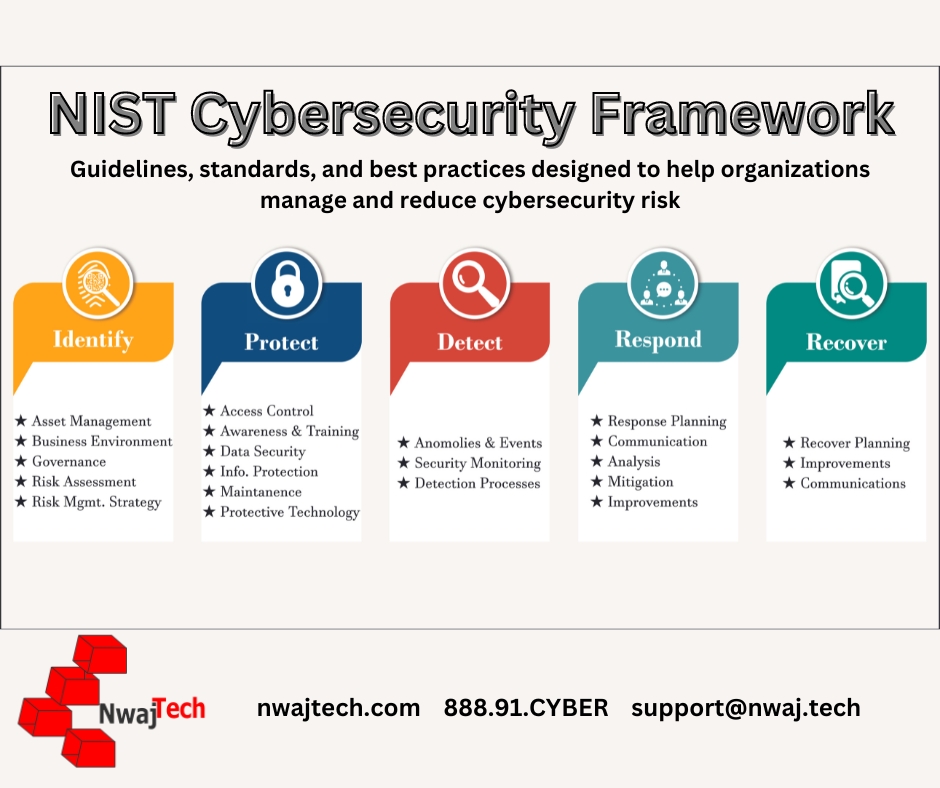
Implement Nist Csf Processunity Discover the value of nist csf 2.0 assessments, designed to enhance your cybersecurity posture and meet regulatory expectations effectively. This nist consultant complete training offers an end to end exploration of the nist risk management framework (rmf) and the cybersecurity framework (csf) 2.0 — preparing professionals to implement, assess, and align organizational security programs with u.s. and global standards. Download the guide to discover how to implement nist csf 2.0 with expert insights, ai powered tools, and step by step guidance to boost cybersecurity and compliance in 2026. Nist csf basically is on govern, identify, protect, detect, respond and recover. at its core is responding and recoer. zero trust foundations: identity & access security (iam): identification domain ransomware readiness for distributed endpoints (including byod): protection on end point secure collaboration: data protection, sharing and access control: protection on third party software suplly. With processunity for cybersecurity risk management, you can map your controls to the nist csf and track your cybersecurity governance policies. while nist csf 2.0 is still in development, processunity will work to keep its control mappings up to date as soon as the new guidance is codified. Implement a control library using a framework mapped to 1,000 control standards, including nist cyber framework (csf), nist 800 53, and iso 27001. automate control assessments and evidentiary requests to keep control reviews on schedule.
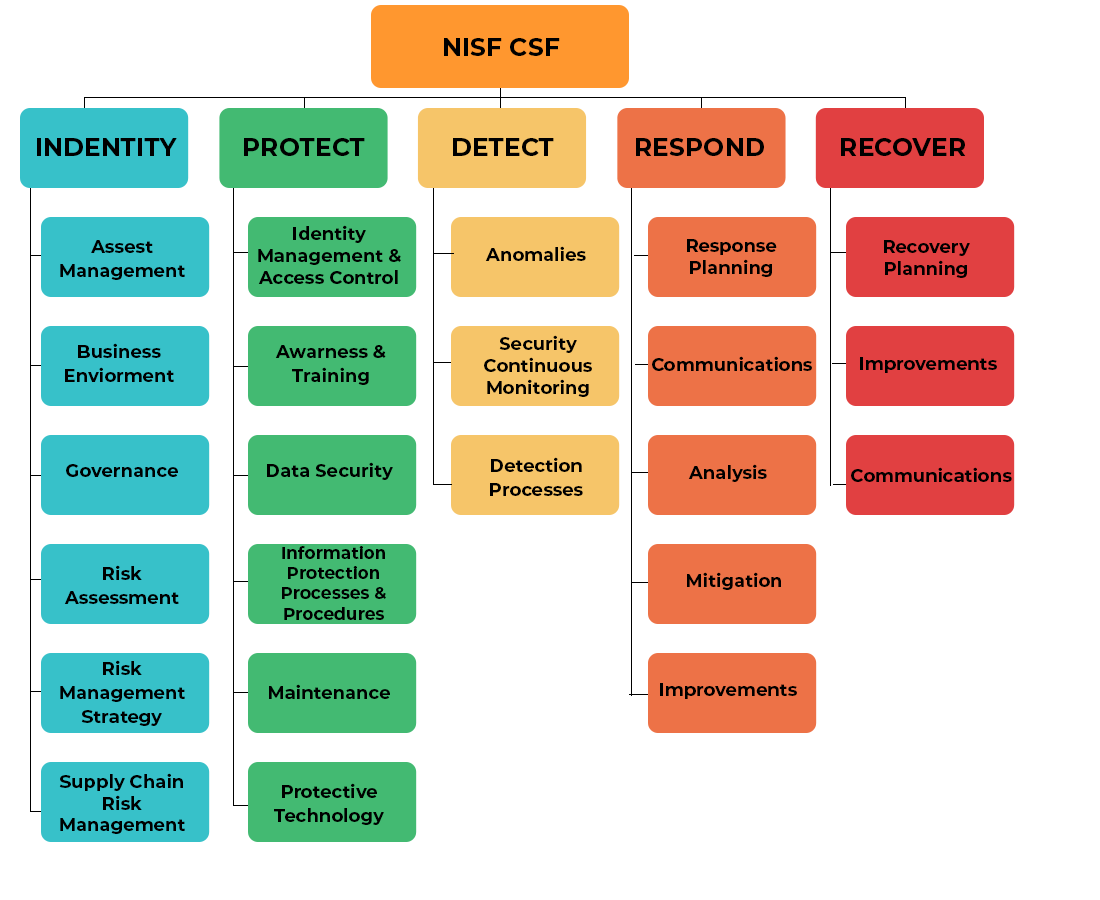
Nist Csf Gai Cyber Solutions Download the guide to discover how to implement nist csf 2.0 with expert insights, ai powered tools, and step by step guidance to boost cybersecurity and compliance in 2026. Nist csf basically is on govern, identify, protect, detect, respond and recover. at its core is responding and recoer. zero trust foundations: identity & access security (iam): identification domain ransomware readiness for distributed endpoints (including byod): protection on end point secure collaboration: data protection, sharing and access control: protection on third party software suplly. With processunity for cybersecurity risk management, you can map your controls to the nist csf and track your cybersecurity governance policies. while nist csf 2.0 is still in development, processunity will work to keep its control mappings up to date as soon as the new guidance is codified. Implement a control library using a framework mapped to 1,000 control standards, including nist cyber framework (csf), nist 800 53, and iso 27001. automate control assessments and evidentiary requests to keep control reviews on schedule.
Securing Your Business An Overview Of The Nist Csf Cybersecurity With processunity for cybersecurity risk management, you can map your controls to the nist csf and track your cybersecurity governance policies. while nist csf 2.0 is still in development, processunity will work to keep its control mappings up to date as soon as the new guidance is codified. Implement a control library using a framework mapped to 1,000 control standards, including nist cyber framework (csf), nist 800 53, and iso 27001. automate control assessments and evidentiary requests to keep control reviews on schedule.
Nist Csf Cybersecurity Frameworks Implementation In Nz Au
Comments are closed.