Identity Orchestration For Customer Identity Management Secureauth

Identity Orchestration Techniques Identity Management Institute From registration to authentication, risk monitoring, and fraud detection, identity orchestration allows you to create flows from your existing security stack. Secureauth corp. today announced a major upgrade to its identity management software arculix, with new features that include improvements to its authentication orchestration and.
Identity Orchestration For Customer Identity Management Secureauth Identity orchestration software helps streamline identity and access management by organizing distinct identity and authentication services into cohesive, automated workflows. Our ai driven risk engine helps deliver dynamic – and often invisible – authentication and authorization for users, combined with a data privacy framework that protects their information and. Secureauth workforce is designed to manage and secure access for employees within an organization, while secureauth ciam focuses on managing and securing customer identities and access. it is tailored for organizations that need to interact with external users, such as customers or partners. Identity orchestration acts as the control layer that unifies identity tools, clouds, and applications. it separates identity logic from applications, with no need for custom code or brittle integrations. enables real time policy enforcement, centralized governance, and secure access flows.

Identity Orchestration For Customer Identity Management Secureauth Secureauth workforce is designed to manage and secure access for employees within an organization, while secureauth ciam focuses on managing and securing customer identities and access. it is tailored for organizations that need to interact with external users, such as customers or partners. Identity orchestration acts as the control layer that unifies identity tools, clouds, and applications. it separates identity logic from applications, with no need for custom code or brittle integrations. enables real time policy enforcement, centralized governance, and secure access flows. From registration to authentication, risk monitoring, and fraud detection, identity orchestration allows you to create flows from your existing security stack that guide users through defined tasks. Secureauth delivers continuous identity security for enterprises. protect workforce, customers & ai agents with real time verification. request a demo. Secureauth connect is a modern, cloud native identity and access management (iam) platform that provides secure, easy access for customer iam (ciam), workforce iam, and partner iam use cases. Use existing enterprise or consumer identities to authenticate users in secureauth. you can connect oidc or saml providers, use secureauth identity pools, or add a custom identity source when you have legacy or non standard systems.
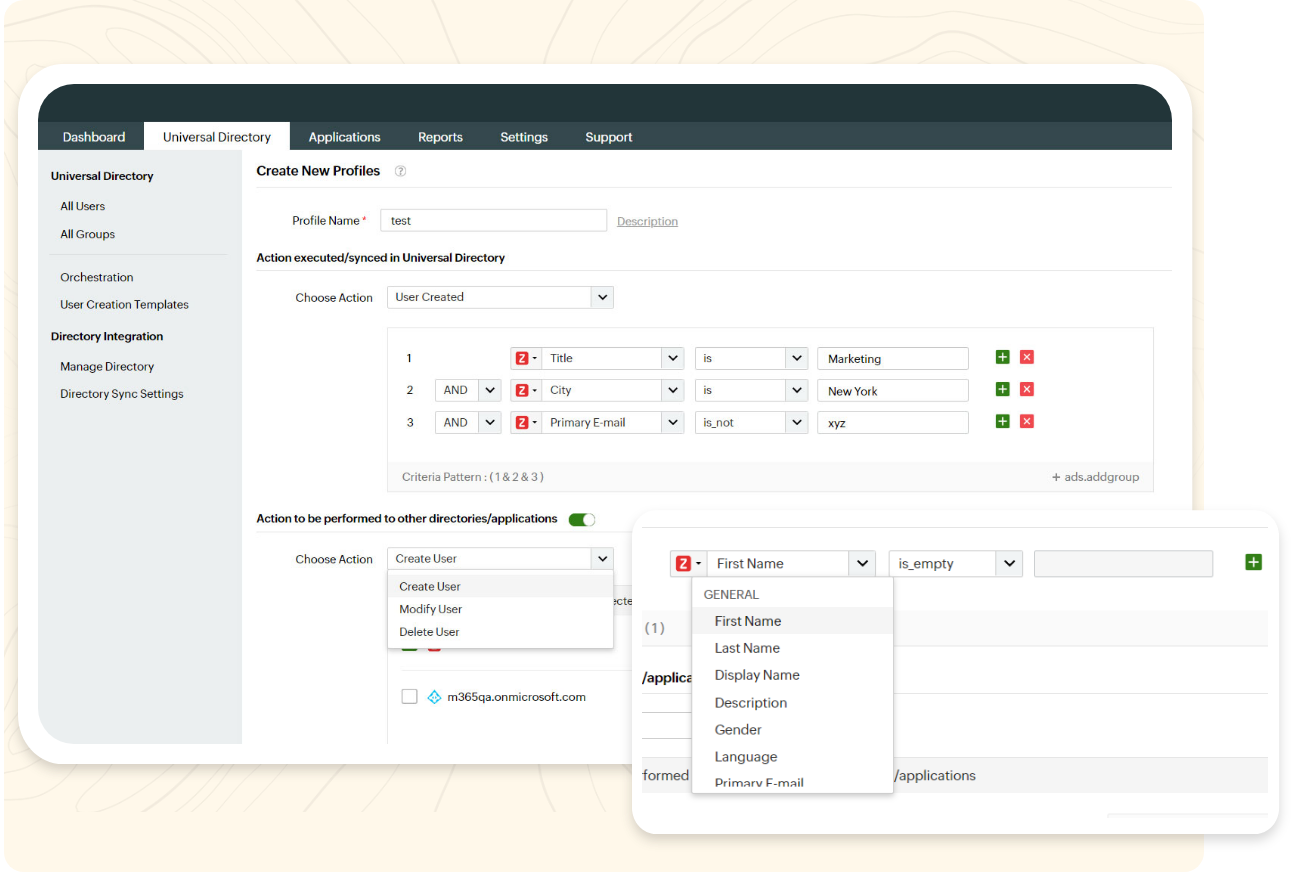
Orchestration Manageengine Identity360 From registration to authentication, risk monitoring, and fraud detection, identity orchestration allows you to create flows from your existing security stack that guide users through defined tasks. Secureauth delivers continuous identity security for enterprises. protect workforce, customers & ai agents with real time verification. request a demo. Secureauth connect is a modern, cloud native identity and access management (iam) platform that provides secure, easy access for customer iam (ciam), workforce iam, and partner iam use cases. Use existing enterprise or consumer identities to authenticate users in secureauth. you can connect oidc or saml providers, use secureauth identity pools, or add a custom identity source when you have legacy or non standard systems.

Identity Orchestration For Workforce Identity Management Secureauth Secureauth connect is a modern, cloud native identity and access management (iam) platform that provides secure, easy access for customer iam (ciam), workforce iam, and partner iam use cases. Use existing enterprise or consumer identities to authenticate users in secureauth. you can connect oidc or saml providers, use secureauth identity pools, or add a custom identity source when you have legacy or non standard systems.
Comments are closed.