Identity Management In Database Administration Baremon
Identity Management In Database Administration Baremon Discover baremon's approach to identity management in database administration, focusing on data security, compliance, and operational efficiency. The database model for identity management systems revolves around efficiently managing users, roles, permissions, authentication providers, audit logs, and their relationships to facilitate secure and compliant identity management operations.
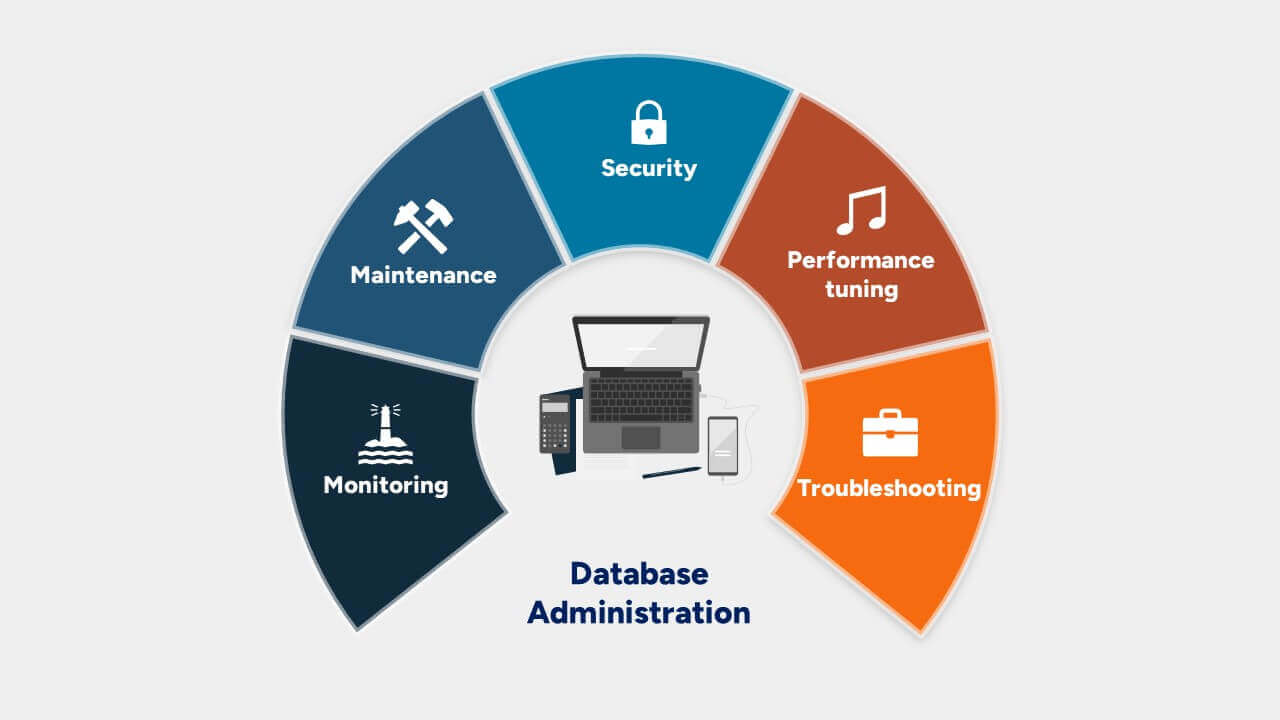
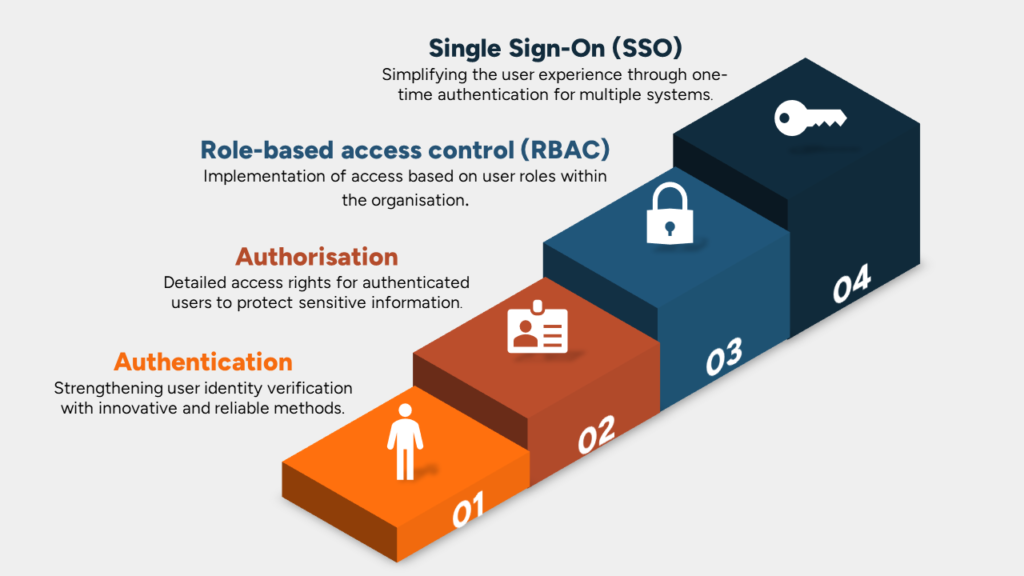
Database Administration Baremon Learn the core concepts of identity and access management (iam), including authentication, authorization, and identity providers, to secure resources effectively. What is identity management? identity management is the process of managing user identities and access privileges in a centralized way. it involves recording and controlling identities within an organization and enforcing identity governance policies. This research seeks to explore optimal governance and administrative practices to enhance identity management systems, with a particular emphasis on security, privacy, and usability. Identity management, otherwise known as identity and access management (iam) is an identity security framework that works to authenticate and authorize user access to resources such as applications, data, systems, and cloud platforms.
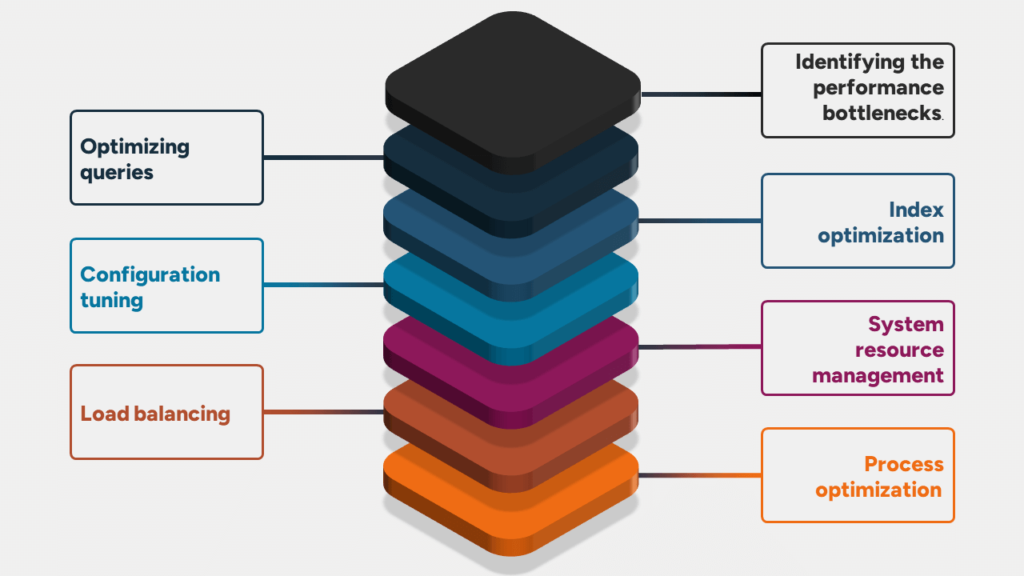
Database Performance Tuning Baremon This research seeks to explore optimal governance and administrative practices to enhance identity management systems, with a particular emphasis on security, privacy, and usability. Identity management, otherwise known as identity and access management (iam) is an identity security framework that works to authenticate and authorize user access to resources such as applications, data, systems, and cloud platforms. The four core pillars of iam are iga, am, pam and ad management. in this article, we explore these pillars and explain why you need all four. The identity management database is used to hold all information about managed users and corresponding account information and is deployed on one of the supported database management systems. Identity and access management standards are critical for ensuring system security, data confidentiality and integrity in many organizations. To reap the most security benefits, it is imperative that companies ensure that their iam tools and processes are set up correctly. in this article, we will share 11 identity and access management best practices your company should adopt to establish a strong security posture.
Comments are closed.