Identity Lifecycle Management Identity Access Provisioning

Identity Provisioning And Access Management Pdf Active Directory The iam lifecycle manages a user’s digital identity from enrollment through maintenance to de provisioning. it ensures users get the right access at the right time, and that they lose it when they no longer need it. While identity and access management (iam) and identity lifecycle management (ilm) are related, they focus on different aspects of identity security. the lifecycle begins with creating and provisioning identities—both human and non human.
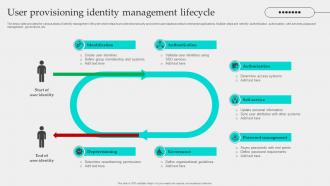
User Provisioning Identity Management Lifecycle Ppt Slide Automation is central: ilm automates provisioning and deprovisioning to eliminate manual errors and security gaps. four critical stages: the identity journey consists of provisioning, access management, monitoring, and deprovisioning. Identity lifecycle management governs digital identities across their full lifecycle, automating provisioning, access changes, and deprovisioning. it enforces least privilege, synchronizes identity data, and integrates with hr, iam, and siem systems. Provisioning: once access is approved, provisioning involves the automated or manual process of granting the requested access to the user. this can include creating user accounts, assigning roles, and configuring permissions. Identity security relies on an effective access provisioning lifecycle, ensuring identities are created, managed, and removed accurately and on time to reduce risk, close access gaps, and maintain continuous compliance.

Identity And Access Management Lifecycle Identity Management Institute Provisioning: once access is approved, provisioning involves the automated or manual process of granting the requested access to the user. this can include creating user accounts, assigning roles, and configuring permissions. Identity security relies on an effective access provisioning lifecycle, ensuring identities are created, managed, and removed accurately and on time to reduce risk, close access gaps, and maintain continuous compliance. Ilm connects identity data, access policies, and automation to ensure every identity — human or non human — has the right access at every point in time. ilm provides the foundation for secure, compliant, and efficient workforce identity management — from onboarding to offboarding. The access provisioning lifecycle is a crucial part of identity and access management (iam). it's the process of managing user access to an organization's resources, like applications, systems, and data, throughout their entire "lifecycle" within the organization. This article describes the deployment process of integrating cloud hr systems, such as workday and successfactors, with microsoft entra id. integrating microsoft entra id with your cloud hr system results in a complete identity lifecycle management system. Learn what identity lifecycle management (ilm) is, how it works, and why it's critical for secure user access. explore stages, benefits, and best practices.

The Identity And Access Provisioning Lifecycle Explained Conductorone Ilm connects identity data, access policies, and automation to ensure every identity — human or non human — has the right access at every point in time. ilm provides the foundation for secure, compliant, and efficient workforce identity management — from onboarding to offboarding. The access provisioning lifecycle is a crucial part of identity and access management (iam). it's the process of managing user access to an organization's resources, like applications, systems, and data, throughout their entire "lifecycle" within the organization. This article describes the deployment process of integrating cloud hr systems, such as workday and successfactors, with microsoft entra id. integrating microsoft entra id with your cloud hr system results in a complete identity lifecycle management system. Learn what identity lifecycle management (ilm) is, how it works, and why it's critical for secure user access. explore stages, benefits, and best practices.

Identity And Access Provisioning Lifecycle Irmt This article describes the deployment process of integrating cloud hr systems, such as workday and successfactors, with microsoft entra id. integrating microsoft entra id with your cloud hr system results in a complete identity lifecycle management system. Learn what identity lifecycle management (ilm) is, how it works, and why it's critical for secure user access. explore stages, benefits, and best practices.

The Identity And Access Provisioning Lifecycle Explained Conductorone
Comments are closed.