Identity And Access Management For Cloud Security Identity Management

Identity And Access Management Cloud Security Solution With ibm consulting’s identity and access management (iam) services, streamline this undertaking with identity and security expertise that will help you define and manage solutions across hybrid cloud environments, transform governance workflows, and demonstrate compliance. This article will analyze why the identity and access management domain is the most significant control for data security in cloud environments. the operational areas of identity and access management include authentication, authorization, federated identity management, and compliance management.

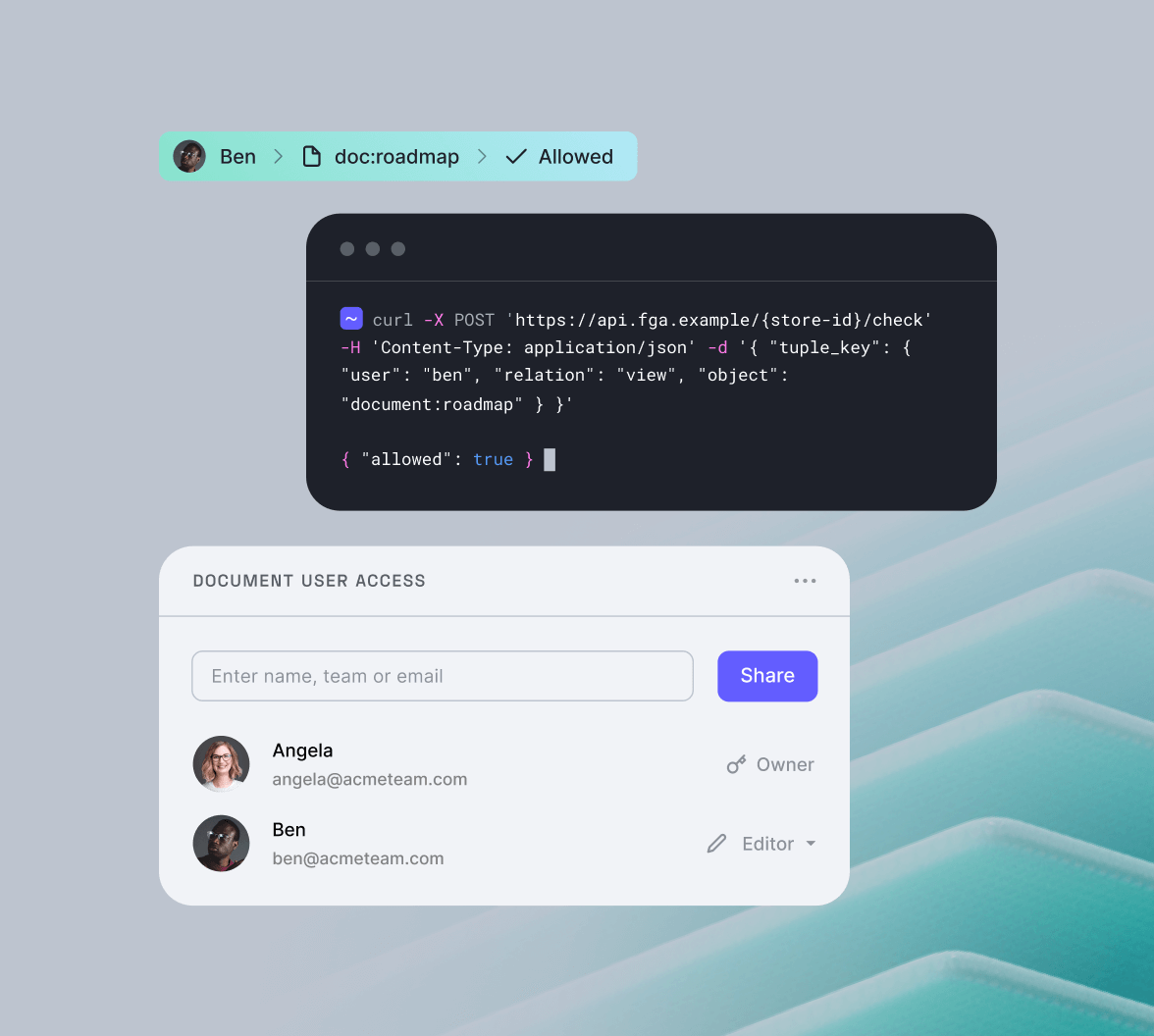
Identity And Access Management For Cloud Security Identity Management In cloud computing, multiple organizations are now managing the identity and access management to resources. find best practices and resources for managing identity securely in the cloud. Learn the fundamentals of identity and access management (iam) in cloud computing, its importance, challenges, and best practices for securing access. Summary: this article looks at identity and access management (iam) in cloud computing. you’ll learn how cloud iam differs from traditional on premises iam, explore the benefits and challenges of cloud iam, and discover how to choose the best cloud iam system for your organization. Cloud identity and access management (iam) enables organizations to securely control user access to resources through a comprehensive framework of policies, processes, and tools that manage digital identities and enforce access rights across on premises, hybrid, and cloud environments.

Rh Isac Manage Your Cloud Vulnerabilities With An Identity And Access Summary: this article looks at identity and access management (iam) in cloud computing. you’ll learn how cloud iam differs from traditional on premises iam, explore the benefits and challenges of cloud iam, and discover how to choose the best cloud iam system for your organization. Cloud identity and access management (iam) enables organizations to securely control user access to resources through a comprehensive framework of policies, processes, and tools that manage digital identities and enforce access rights across on premises, hybrid, and cloud environments. Identity and access management (iam) is the practice of making sure that people and entities with digital identities have the right level of access to enterprise resources like networks and databases. Learn what identity and access management (iam) is, how it works, and why it’s critical for modern cybersecurity. explore benefits, challenges & best practices. Iam (identity and access management) verifies users and manages their access privileges, becoming the critical security control point in the cloud computing era. In this guide, we will cover everything you need to know about cloud identity and access management (iam), including key considerations and more.

Identity Access Management Authentication With Cloud Identity Identity and access management (iam) is the practice of making sure that people and entities with digital identities have the right level of access to enterprise resources like networks and databases. Learn what identity and access management (iam) is, how it works, and why it’s critical for modern cybersecurity. explore benefits, challenges & best practices. Iam (identity and access management) verifies users and manages their access privileges, becoming the critical security control point in the cloud computing era. In this guide, we will cover everything you need to know about cloud identity and access management (iam), including key considerations and more.
Identity And Access Management For Cloud Security Free Essay Example Iam (identity and access management) verifies users and manages their access privileges, becoming the critical security control point in the cloud computing era. In this guide, we will cover everything you need to know about cloud identity and access management (iam), including key considerations and more.
Cloud Identity And Access Management Iam
Comments are closed.