Iam Policies Sysdig Docs
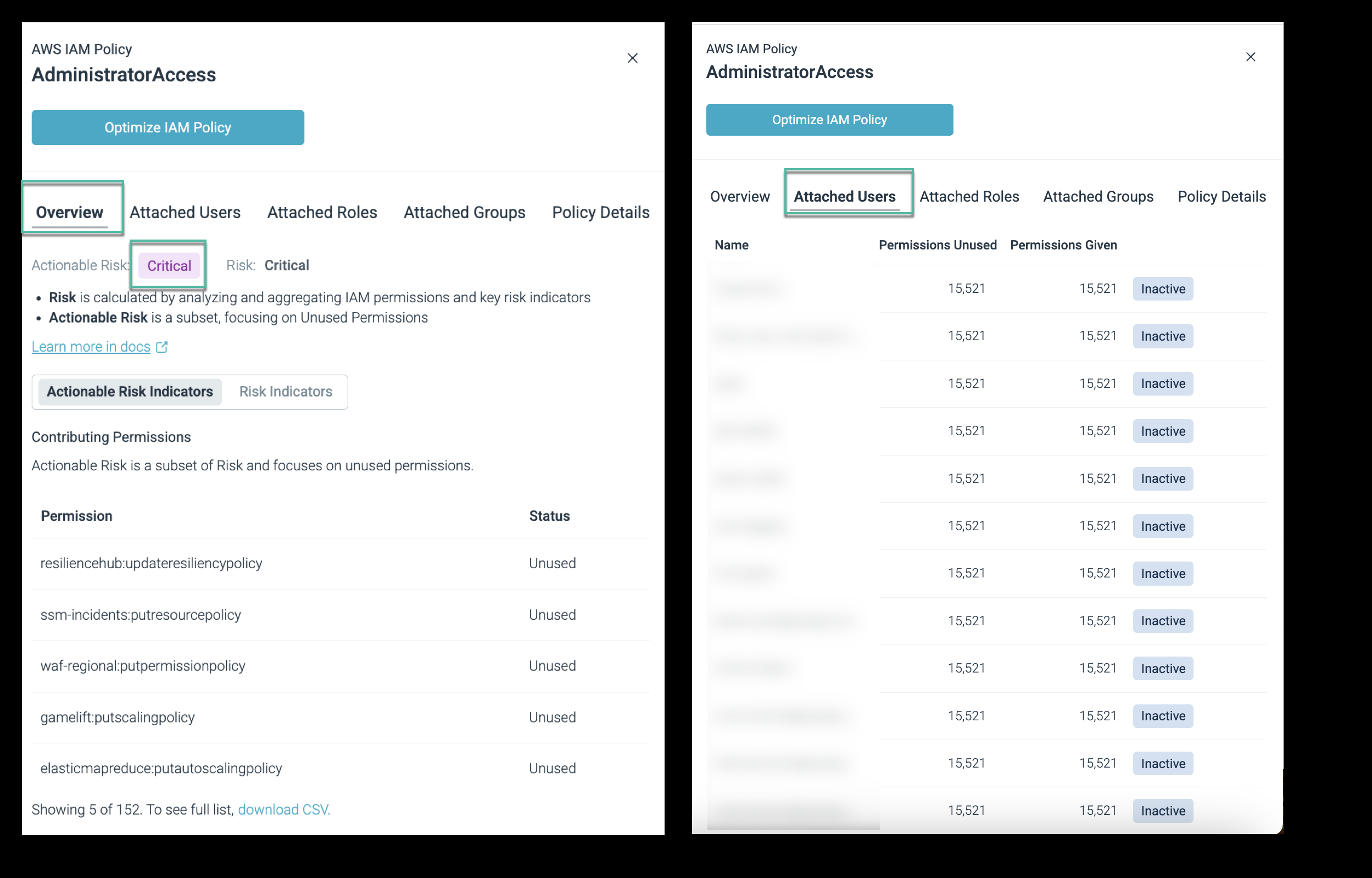
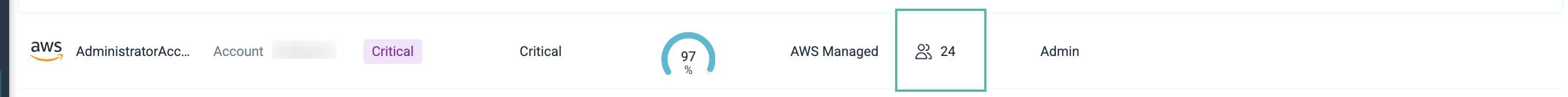
Iam Policies Sysdig Docs Summary: displays the critical permissions issues detected on the iam policy, sorted by permission criticality and unused permission criticality. remediation strategies: displays suggested remediations, with instructions. Sysdig also provides an overview of existing custom policies and permissions attached to them. explore some of the remediation workflows for the roles in your account.
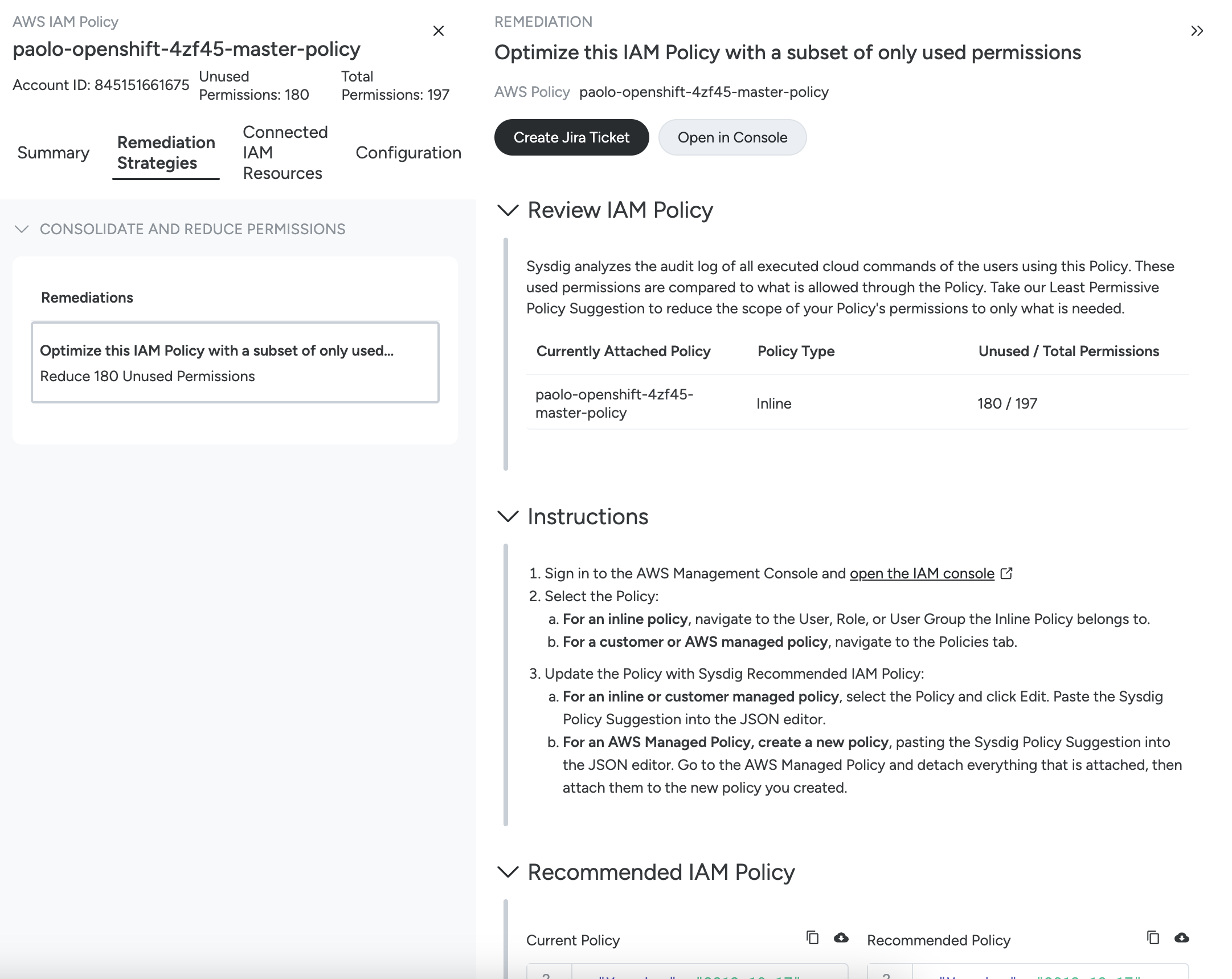
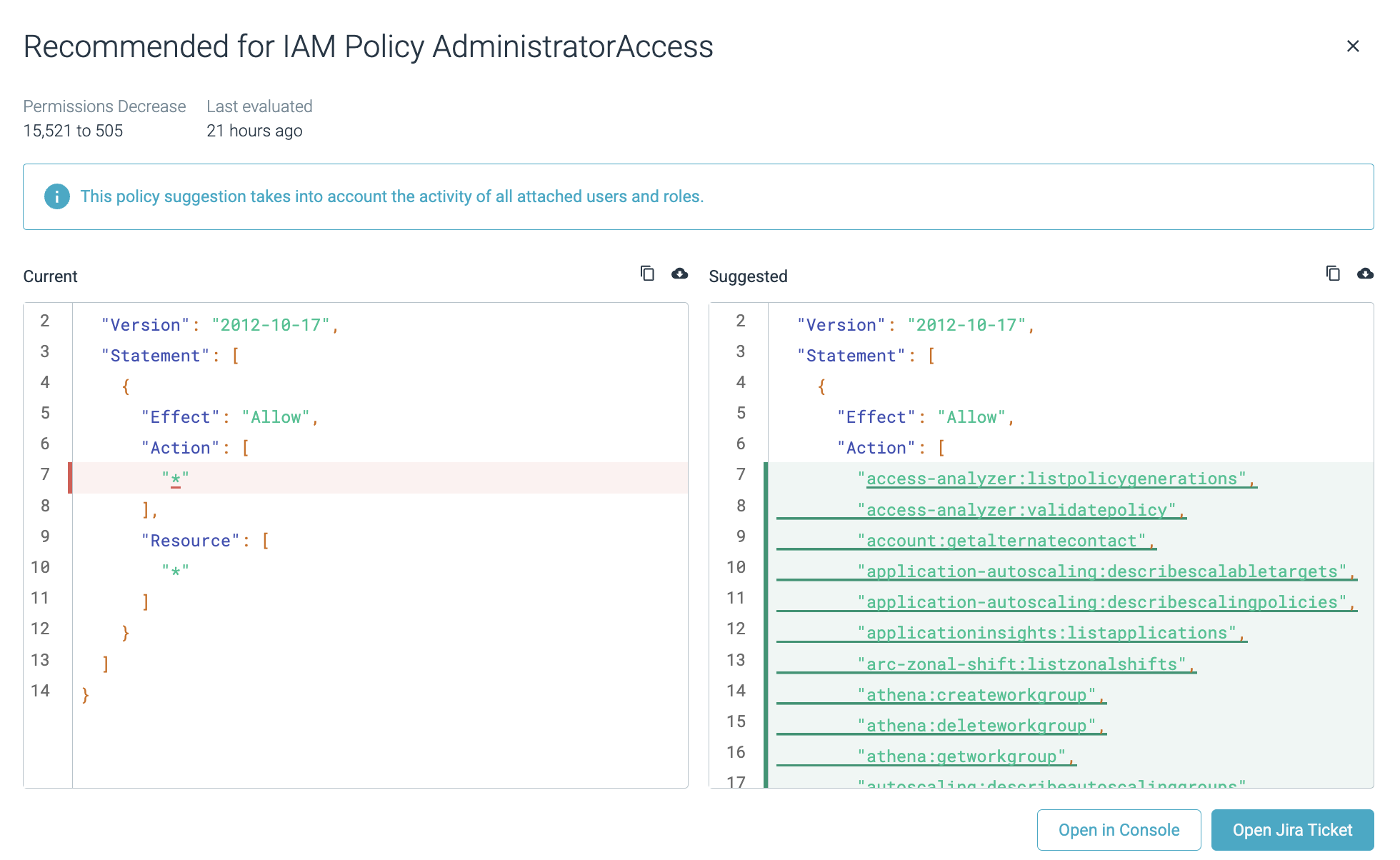
Iam Policies Sysdig Docs Sysdig uses policies to generate events based on data collected from cloud environments. these policies provide visibility into system behavior, enabling you to understand potential risks and take proactive measures. Create a sysdig specific identity access management (iam) policy to be used for granting programmatic access to sysdig. copy the code snippet and paste into this policy. When your aws accounts are successfully connected to sysdig secure with advanced ciem, sysdig detects and analyzes the policies, roles, users, and groups you’ve configured in aws for identity and access weak points and proposes remediation steps. Review the iam policies and instructions to create a new iam policy. click open in console to open the aws management console to perform the actions given in the remediation instructions.
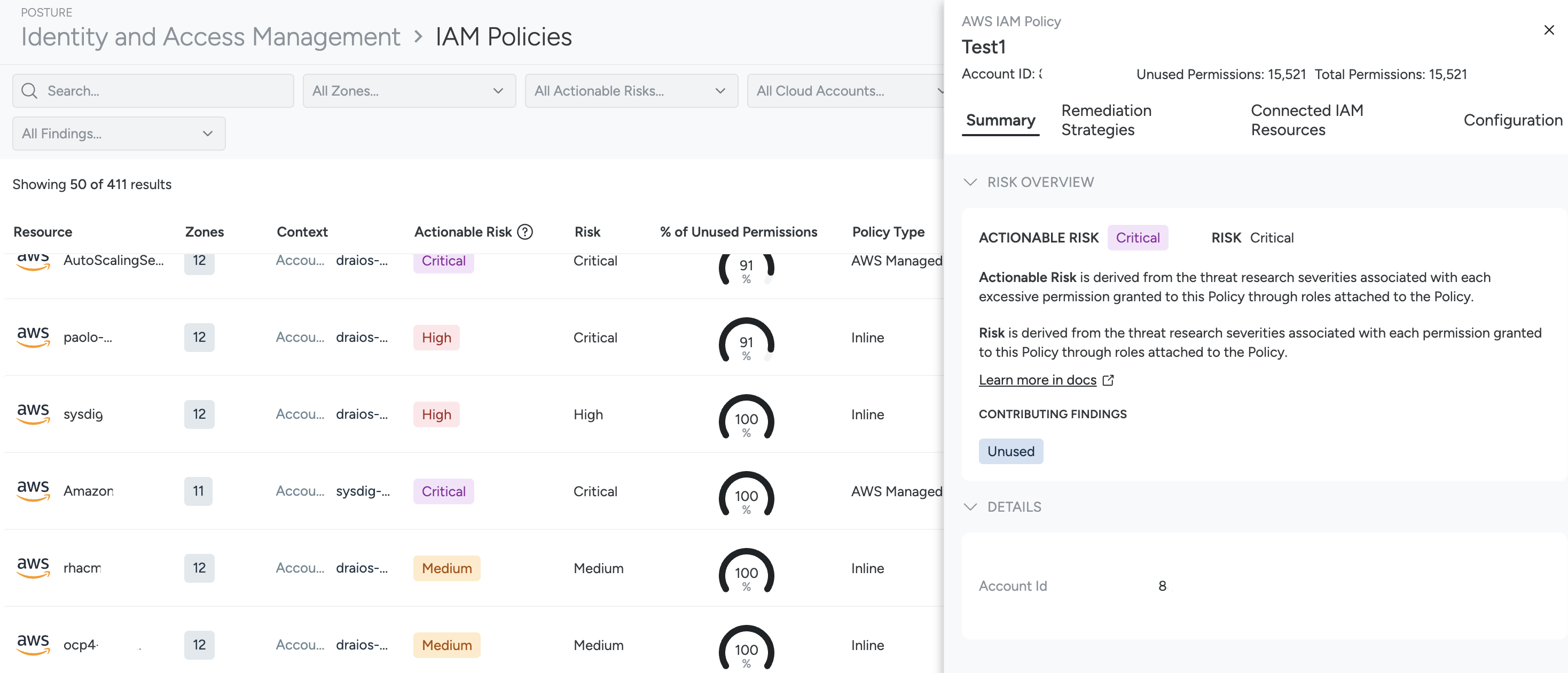
Iam Policies Sysdig Docs When your aws accounts are successfully connected to sysdig secure with advanced ciem, sysdig detects and analyzes the policies, roles, users, and groups you’ve configured in aws for identity and access weak points and proposes remediation steps. Review the iam policies and instructions to create a new iam policy. click open in console to open the aws management console to perform the actions given in the remediation instructions. Download a pdf of the policy compliance report to get an overview of specific compliance policies within a defined zone. the report highlights the status of passing requirements and controls, along with the count of passing and failing resources for each control. Get support for sysdig products. access documentation, contact customer success, and check system status. The identity overview page provides a high level view of your cloud identity and access management (iam) posture, displaying key metrics, trends, and top findings to help you quickly identify and prioritize areas for improvement. Sysdig’s ciem tracks key iam risks like inactive or unused permissions, inactive users, and high risk policies. you can drill into users or roles to see exact permission usage and last active dates, and receive suggested least privilege versions of existing policies, making cleanup fast and low risk.
Iam Policies Sysdig Docs Download a pdf of the policy compliance report to get an overview of specific compliance policies within a defined zone. the report highlights the status of passing requirements and controls, along with the count of passing and failing resources for each control. Get support for sysdig products. access documentation, contact customer success, and check system status. The identity overview page provides a high level view of your cloud identity and access management (iam) posture, displaying key metrics, trends, and top findings to help you quickly identify and prioritize areas for improvement. Sysdig’s ciem tracks key iam risks like inactive or unused permissions, inactive users, and high risk policies. you can drill into users or roles to see exact permission usage and last active dates, and receive suggested least privilege versions of existing policies, making cleanup fast and low risk.
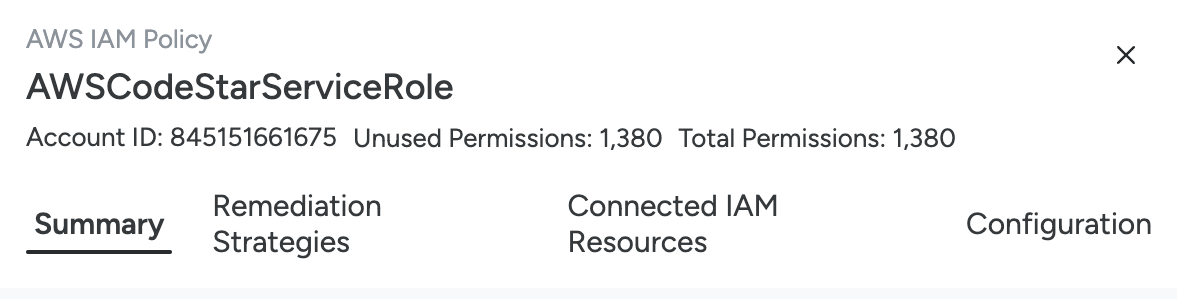
Iam Policies Sysdig Docs The identity overview page provides a high level view of your cloud identity and access management (iam) posture, displaying key metrics, trends, and top findings to help you quickly identify and prioritize areas for improvement. Sysdig’s ciem tracks key iam risks like inactive or unused permissions, inactive users, and high risk policies. you can drill into users or roles to see exact permission usage and last active dates, and receive suggested least privilege versions of existing policies, making cleanup fast and low risk.
Iam Policies Sysdig Docs
Comments are closed.