Http3 Explained Pdf Transmission Control Protocol Transport Layer

Transport Layer Introduction Pdf Port Computer Networking Http3 explained free download as pdf file (.pdf), text file (.txt) or read online for free. this document provides an overview and introduction to http 3 and its underlying quic protocol. it discusses some of the limitations of http 2 over tcp, including head of line blocking issues. Much like http 2 was once introduced to transport http over the wire in a completely new way, http 3 is yet again introducing a new way to send http over the network.

Unit4 Transport Layer Pdf Transmission Control Protocol Port Transmission control protocol (tcp) reliable byte stream service all data reach receiver: in order they were sent, with no data corrupted reliable, in order delivery corruption: checksums detect loss reordering: sequence numbers reliable delivery: acknowledgments and retransmissions. Chapter 3: our goals understand principles behind transport layer services: multiplexing, de multiplexing reliable data transfer flow control congestion control. In the previous two chapter we gave a brief overview of the tcp ip transport layer protocols, namely, user datagram protocol (udp) and transmission control protocol (tcp). this chapter continues the discussion of udp and tcp but in more details. Tcp uses a sliding window protocol without selective or negative acknowledgments. selective acknowledgments would let the protocol say it’s missing a range of bytes.

Transport Layer Protocols Geeksforgeeks In the previous two chapter we gave a brief overview of the tcp ip transport layer protocols, namely, user datagram protocol (udp) and transmission control protocol (tcp). this chapter continues the discussion of udp and tcp but in more details. Tcp uses a sliding window protocol without selective or negative acknowledgments. selective acknowledgments would let the protocol say it’s missing a range of bytes. Transport layer: overview our goal: understand principles behind transport layer services: multiplexing, demultiplexing reliable data transfer flow control. The transport layer provides transparent transfer of data between hosts. it provides end to end control and information transfer with the quality of service needed by the application program. it is the first true end to end layer, implemented in all end systems (es). At the data link layer, two routers communicate directly via a physical channel, whether wired or wireless, whereas at the transport layer, this physical channel is replaced by the entire network. The transport layer is responsible for flow control. it uses the sliding window protocol that makes the data transmission more efficient as well as it controls the flow of data so that the receiver does not become overwhelmed.
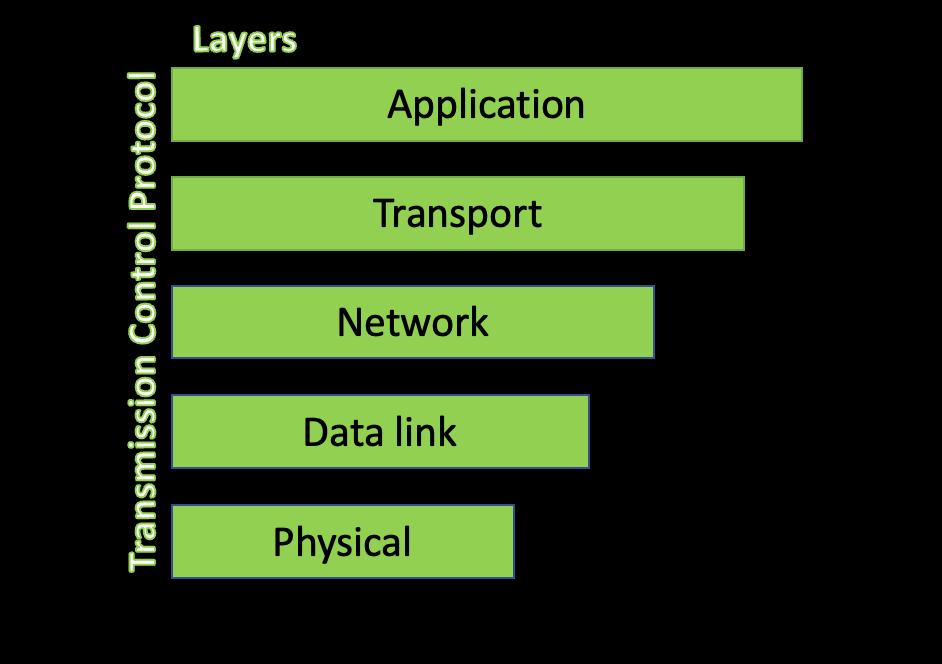
Transport Layer Protocols Transport layer: overview our goal: understand principles behind transport layer services: multiplexing, demultiplexing reliable data transfer flow control. The transport layer provides transparent transfer of data between hosts. it provides end to end control and information transfer with the quality of service needed by the application program. it is the first true end to end layer, implemented in all end systems (es). At the data link layer, two routers communicate directly via a physical channel, whether wired or wireless, whereas at the transport layer, this physical channel is replaced by the entire network. The transport layer is responsible for flow control. it uses the sliding window protocol that makes the data transmission more efficient as well as it controls the flow of data so that the receiver does not become overwhelmed.
Transmission Control Protocol Internet Protocol Studocu At the data link layer, two routers communicate directly via a physical channel, whether wired or wireless, whereas at the transport layer, this physical channel is replaced by the entire network. The transport layer is responsible for flow control. it uses the sliding window protocol that makes the data transmission more efficient as well as it controls the flow of data so that the receiver does not become overwhelmed.
Comments are closed.