Html Checkmarx Security Vulnerability In Uploading File Cordova

Html Checkmarx Security Vulnerability In Uploading File Cordova In my angular code, i read the file as follows: the thing is, user will need to upload the file from their local drive, and i cannot limit which folder in their laptop that they have to put the file. i'm not sure also on how to "sanitize" the input filename, as target itself is an object. any ideas?. If the vulnerability is cataloged in our database then results are shown, giving detailed information about the nature of the threat and its severity. also, a list of packages (and relevant versions) that are affected by the vulnerability is shown.

Html Checkmarx Security Vulnerability In Uploading File Cordova A stored cross site scripting (xss) vulnerability in the “port settings” page allows authenticated users to inject arbitrary javascript through the `descr` parameter when editing a device’s port settings, which then executes when the page is viewed. Below is a list taken for owasp cheat sheet series on how to secure a file upload functionality. please refer to the cheat sheet for a comprehensive recommendations. In this case, a missing validation check in the script can be exploited to upload and execute malicious files. the code below lets a user upload a picture of a flag (in this case, a secureflag picture) to the web server. the html form uses a file input field to let the user select a file for upload. A simple, seemingly harmless file can become a trojan horse, enabling an attacker to take control of the system or disrupt its operation. in this article, we will review file upload vulnerabilities. we will detail the various techniques used by attackers to bypass security mechanisms.
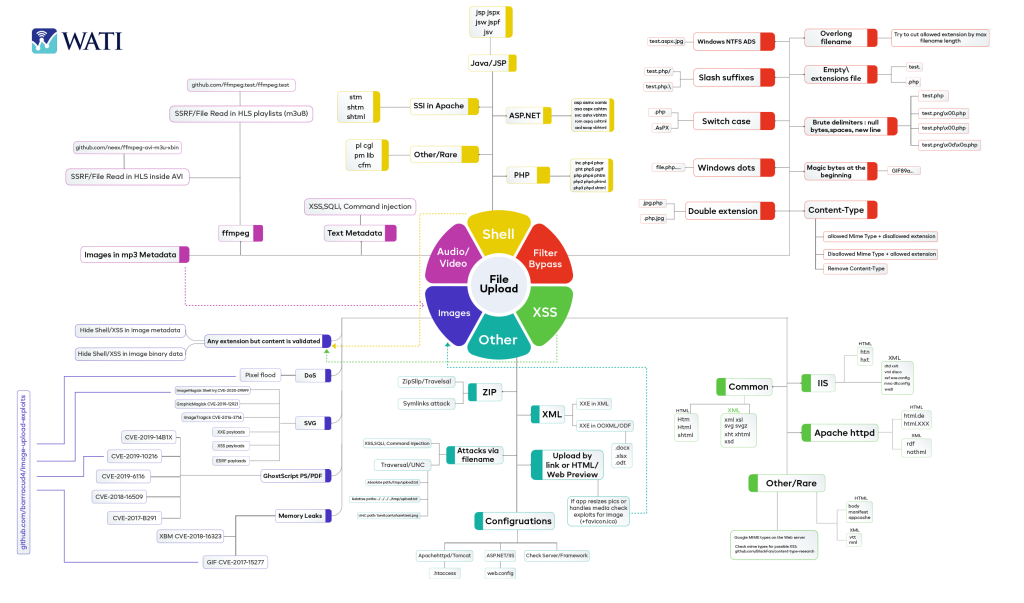
File Upload Vulnerability In this case, a missing validation check in the script can be exploited to upload and execute malicious files. the code below lets a user upload a picture of a flag (in this case, a secureflag picture) to the web server. the html form uses a file input field to let the user select a file for upload. A simple, seemingly harmless file can become a trojan horse, enabling an attacker to take control of the system or disrupt its operation. in this article, we will review file upload vulnerabilities. we will detail the various techniques used by attackers to bypass security mechanisms. A file upload vulnerability occurs when a web application allows users to upload files without properly checking their type, content, or purpose. this security flaw can let attackers upload harmful files like scripts or malware instead of safe files such as images or documents. An attacker can exploit this by crafting a malicious image file that, when processed by imagemagick, can disclose information from the local filesystem of the server running the vulnerable version of the software. We have resolved a security issue in the camera plugin that could have affected certain cordova (android) applications. an attacker who could install (or lead the victim to install) a specially crafted (or malicious) android application would be able to access pictures taken with the app externally. We'll show you how to bypass common defense mechanisms in order to upload a web shell, enabling you to take full control of a vulnerable web server. given how common file upload functions are, knowing how to test them properly is essential knowledge.
Comments are closed.