Htb Swagshop
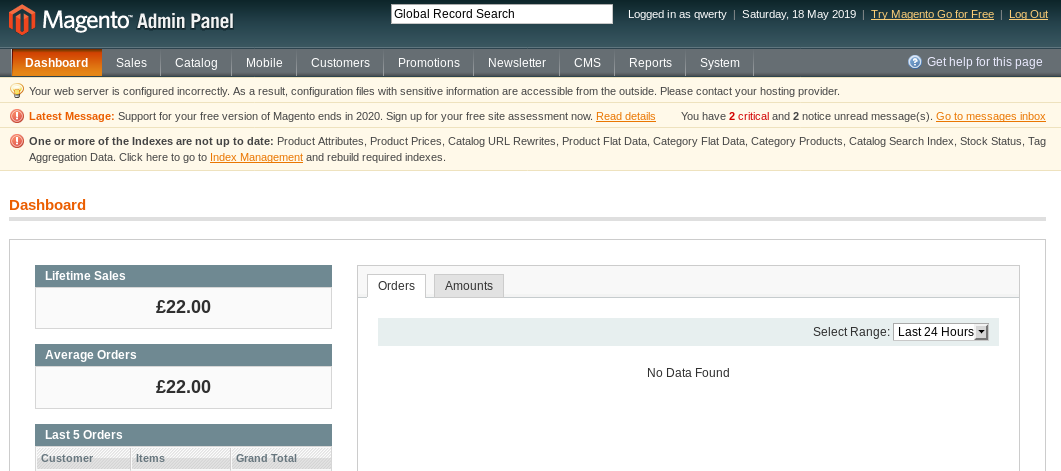
Swagshop Hipotermia Swagshop was a nice beginner easy box centered around a magento online store interface. i’ll use two exploits to get a shell. the first is an authentication bypass that allows me to add an admin user to the cms. then i can use an authenticated php object injection to get rce. i’ll also show how got rce with a malicious magento package. Having done some research on the nature of this exploit, it appears to be a php object injection vulnerability. a key aspect to this attack vector is the date when it was installed which is present in swagshop.htb app etc local.xml. this allows me to inject my own code, resulting in the rce.
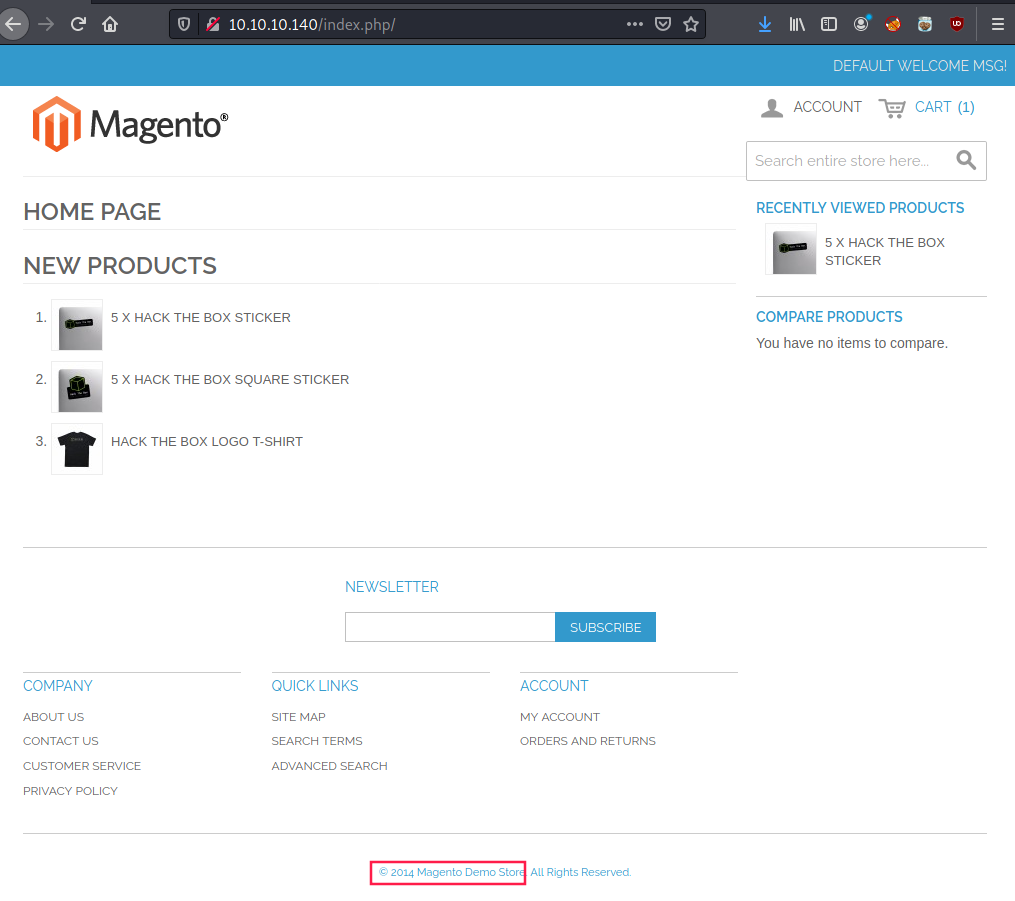
Hackthebox Swagshop Pymaster Ft Hi guys, today i want to explain how i solved the swagshop machine. since this is my first writeup feel free to correct me if i’m wrong so i can learn from it. Swagshop is an easy difficulty linux box running an old version of magento which is vulnerable to sqli and rce vulnerabilities leading to a shell. the low level user can run `vim` with 'sudo' privileges, which can be abused to escalate privileges and obtain a root shell. This post documents my walkthrough of the swagshop machine from hack the box. the machine exploits vulnerabilities in a magento 1.9 web application to gain initial access. We’ll use the same enumeration automation script we used on a few other recent boxes nmapautomator. you can find and download the script here on github. let’s run a full scan against the target: host is up (0.029s latency). host is up (0.033s latency). service detection performed. please report any incorrect results at nmap.org submit .
Github Jebidiah Anthony Htb Swagshop Htb Swagshop 10 10 10 140 This post documents my walkthrough of the swagshop machine from hack the box. the machine exploits vulnerabilities in a magento 1.9 web application to gain initial access. We’ll use the same enumeration automation script we used on a few other recent boxes nmapautomator. you can find and download the script here on github. let’s run a full scan against the target: host is up (0.029s latency). host is up (0.033s latency). service detection performed. please report any incorrect results at nmap.org submit . Swagshop is a easy difficulty linux machine which running old version on magento. it is vulnerable to sqli and rce which leads to shell as www data. privilege escalation invovles the www data can use vim in the context of root which is abused to execute commands as root. Today i’m walking you through the swagshop machine from hackthebox. swagshop is a beginner friendly linux box focused on a magento based ecommerce platform. Based on path recon, visit swagshop.htb media custom options quote r s and see click after nc lvnp 1234 on local host, swagshop.htb media custom options quote r s 5647c47908b0c805af6f92e5e1d3f92b. So, we add swagshop.htb with its ip address into the etc hosts file as shown below. now, we decide to enumerate the http service on the target machine. as soon as we open it, we see that it is an e commerce based template on magento framework.
Comments are closed.