Htb Mongod Walkthrough
Htb Mongod Welcome back to another writeup of an htb machine from the starting point series. this machine is the 7th machine from the starting point series and is reserved for vip users only. without. Htb: mongod walkthrough february 09, 2025 writeup — mongod by araiz naqvi prepared by araiz naqvi. overview difficulty: easy operating system: linux objective: capture flag via mongodb tools used: nmap, mongosh, openvpn.

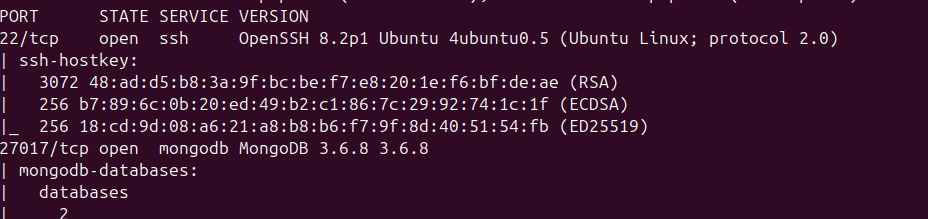
Htb Mongod We start with an nmap scan to identify open ports and services running on the target machine: results: 27017 tcp open mongodb mongodb 3.6.8. mongodb is running on port 27017, and based on the version (3.6.8), it might be misconfigured. I will cover solution steps of the “mongod” machine, which is part of the ‘starting point’ labs and has a difficulty rating of ‘very easy’. this is a vip machine so you’d need an upgrade from your free plan. Learning outcomes in the first tier, you will gain essential skills in the world of cybersecurity pen testing. you'll start by learning how to connect to various services, such as ftp, smb, telnet,. First we will check all the available dbs. command ::: show dbs. we have bunch of dbs and all of them are interesting. but we know which one to check (sensitive information) now we need to see whats inside. type: show collections and we can see a collection called flag. now we need to get the contents of the flag.

Htb Mongod This Is Another Of The Very Easy Htb By Sec Rffuste Learning outcomes in the first tier, you will gain essential skills in the world of cybersecurity pen testing. you'll start by learning how to connect to various services, such as ftp, smb, telnet,. First we will check all the available dbs. command ::: show dbs. we have bunch of dbs and all of them are interesting. but we know which one to check (sensitive information) now we need to see whats inside. type: show collections and we can see a collection called flag. now we need to get the contents of the flag. This is a simple walkthrough of the tier 0 htb box “mongod”. looking at the tags of the machine we can see some interesting ones like: “mongodb”, “databases”, and “anonymous guest access” so we already know that this box will be focused around the database mongodb and will most likely have guest access to the database. Using kali linux, htb’s mongod box was a tricky one! hack the box throws a curve ball by adding the mongo switch pretty () at the end of the submission string. since i’m not a mongo expert, it took me a while to find the command. i don’t think pretty () is a common mongo command. maybe i’m wrong!. Perform a rapid triage analysis of the collected artifacts to determine whether the system has been compromised, identify any attacker activity (initial access, persistence, privilege escalation, lateral movement, or data access exfiltration), and summarize your findings with an initial incident assessment and recommended next steps. After connecting to htb’s environment through either their pwnbox or openvpn let’s go ahead and spawn our target and then get started with this first task. we’re gonna knock out these first two tasks with an nmap scan, we’re not wasting any time today. here you see me run.
Htb Mongod This Is Another Of The Very Easy Htb By Sec Rffuste This is a simple walkthrough of the tier 0 htb box “mongod”. looking at the tags of the machine we can see some interesting ones like: “mongodb”, “databases”, and “anonymous guest access” so we already know that this box will be focused around the database mongodb and will most likely have guest access to the database. Using kali linux, htb’s mongod box was a tricky one! hack the box throws a curve ball by adding the mongo switch pretty () at the end of the submission string. since i’m not a mongo expert, it took me a while to find the command. i don’t think pretty () is a common mongo command. maybe i’m wrong!. Perform a rapid triage analysis of the collected artifacts to determine whether the system has been compromised, identify any attacker activity (initial access, persistence, privilege escalation, lateral movement, or data access exfiltration), and summarize your findings with an initial incident assessment and recommended next steps. After connecting to htb’s environment through either their pwnbox or openvpn let’s go ahead and spawn our target and then get started with this first task. we’re gonna knock out these first two tasks with an nmap scan, we’re not wasting any time today. here you see me run.

Htb Walkthrough Mongod Mongodb By Ahmad Sopyan Medium Perform a rapid triage analysis of the collected artifacts to determine whether the system has been compromised, identify any attacker activity (initial access, persistence, privilege escalation, lateral movement, or data access exfiltration), and summarize your findings with an initial incident assessment and recommended next steps. After connecting to htb’s environment through either their pwnbox or openvpn let’s go ahead and spawn our target and then get started with this first task. we’re gonna knock out these first two tasks with an nmap scan, we’re not wasting any time today. here you see me run.
Comments are closed.