Htb Buff Walkthrough Spyx S Blog Simple Place For Me To Blog
Htb Buff Walkthrough Spyx S Blog Simple Place For Me To Blog As i was dedicated to place one box every day i was planning to put another box. i hit hard bottom for some reason exploit is not working and i have no clue how to move now. A showcase of my cybersecurity journey through hack the box ctf challenges, highlighting skills in network enumeration, exploitation, and problem solving. ctf chronicles htb buff walkthrough.md at main · solaconsay ctf chronicles.

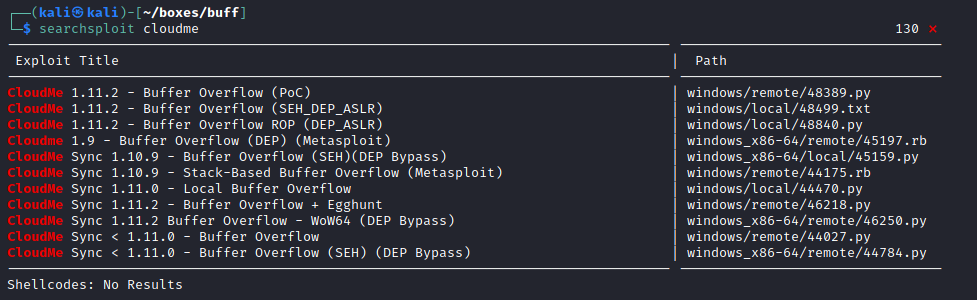
Htb Buff Walkthrough Spyx S Blog Simple Place For Me To Blog This is my write up and walkthrough for the buff box. when commencing this engagement, buff was listed in htb (hackthebox) with an easy difficulty rating. If you played or read my walktrhough on buff you know there is buffer overflow exploit as privileges escalation path to root admin. i think most people do is find python exploit on exploit db and use it. Welcome back dear reader, this time we tackle the hackthabox buff machine that was tricky at times with a series of unexpected behaviors. i'll explain what the problem that slowed me down was, let's not waste any more time and jump right in!. Today i’m working on box 29 100, buff from hackthebox. this was an enjoyable windows machine that featured a publicly available rce exploit for foothold, and a basic buffer overflow via a.

Htb Buff Walkthrough Spyx S Blog Simple Place For Me To Blog Welcome back dear reader, this time we tackle the hackthabox buff machine that was tricky at times with a series of unexpected behaviors. i'll explain what the problem that slowed me down was, let's not waste any more time and jump right in!. Today i’m working on box 29 100, buff from hackthebox. this was an enjoyable windows machine that featured a publicly available rce exploit for foothold, and a basic buffer overflow via a. Hackthebox | buff walkthrough | htb we are starting a daily series in which we are going to cover writeups of 37 hack the box boxes of the tjnull list for oscp preparation. 37 days of hack the box …. Today, we will be continuing with our exploration of hack the box (htb) machines, as seen in previous articles. this walkthrough is of an htb machine named buff. Introduction buff is the third windows box in my “let’s brush up on windows!” series. for the previous one, see my walkthrough on netmon. this box houses a web app for a fictional gym fitness center. it’s fairly easy, but requires good windows enumeration fundamentals. First create your chisel server on your attacking machine. the option p $port opens a listener on the port specified. then, on the victim machine you need to create a client, specifying which local port you would like to connect to through your reverse tunnel. i started my enumeration with an nmap scan of 10.10.10.198.
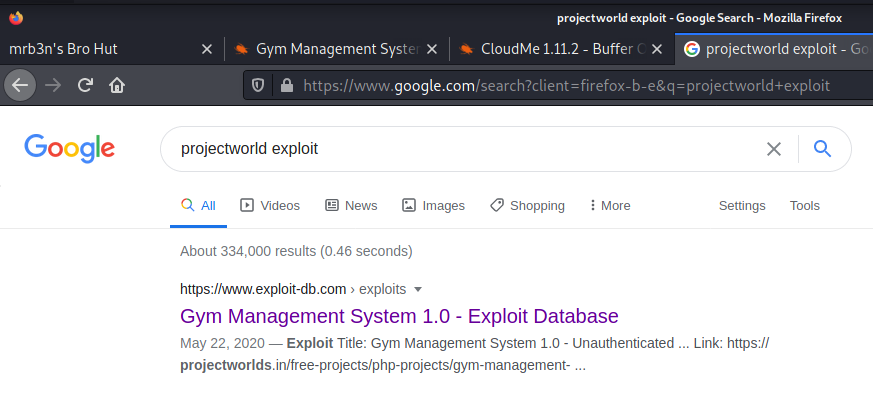
Htb Buff Walkthrough Spyx S Blog Simple Place For Me To Blog Hackthebox | buff walkthrough | htb we are starting a daily series in which we are going to cover writeups of 37 hack the box boxes of the tjnull list for oscp preparation. 37 days of hack the box …. Today, we will be continuing with our exploration of hack the box (htb) machines, as seen in previous articles. this walkthrough is of an htb machine named buff. Introduction buff is the third windows box in my “let’s brush up on windows!” series. for the previous one, see my walkthrough on netmon. this box houses a web app for a fictional gym fitness center. it’s fairly easy, but requires good windows enumeration fundamentals. First create your chisel server on your attacking machine. the option p $port opens a listener on the port specified. then, on the victim machine you need to create a client, specifying which local port you would like to connect to through your reverse tunnel. i started my enumeration with an nmap scan of 10.10.10.198.

Hackthebox Buff Walkthrough Htb By Rootissh Rootissh Introduction buff is the third windows box in my “let’s brush up on windows!” series. for the previous one, see my walkthrough on netmon. this box houses a web app for a fictional gym fitness center. it’s fairly easy, but requires good windows enumeration fundamentals. First create your chisel server on your attacking machine. the option p $port opens a listener on the port specified. then, on the victim machine you need to create a client, specifying which local port you would like to connect to through your reverse tunnel. i started my enumeration with an nmap scan of 10.10.10.198.
Comments are closed.