How Zero Trust Edge Security Transforms Hybrid Remote Work Charitable
How Zero Trust Edge Security Transforms Hybrid Remote Work Charitable Zero trust edge security (or zero trust for short) transformed their operations. their staff went from a “hope” based strategy manually jumping through numerous security hoops to a “data” based strategy, becoming a secure and resilient organization. As part of zero trust adoption guidance, this article describes the business scenario of securing remote and hybrid work. note that securing your business data and infrastructure are the topics of separate business scenarios and are not included in this guidance.

Protect Users Everywhere With Integrated Zero Trust Hybrid Security Hybrid and remote work are now permanent across the nonprofit sector. while flexibility has expanded reach and engagement, it has also quietly increased cyber risk. As part of zero trust adoption guidance, this article describes the business scenario of securing remote and hybrid work. note that securing your business data and infrastructure are the topics of separate business scenarios and are not included in this guidance. In this blog series, i’m sharing how you can adjust your cybersecurity strategy to meet the requirements of a remote and or hybrid workforce, where employees use personal devices and cloud services outside the corporate network. In this blog series, we’ll discuss two zero trust business scenarios: enabling a more productive hybrid or remote work environment and rapidly modernizing your organization’s security posture through a zero trust architecture.

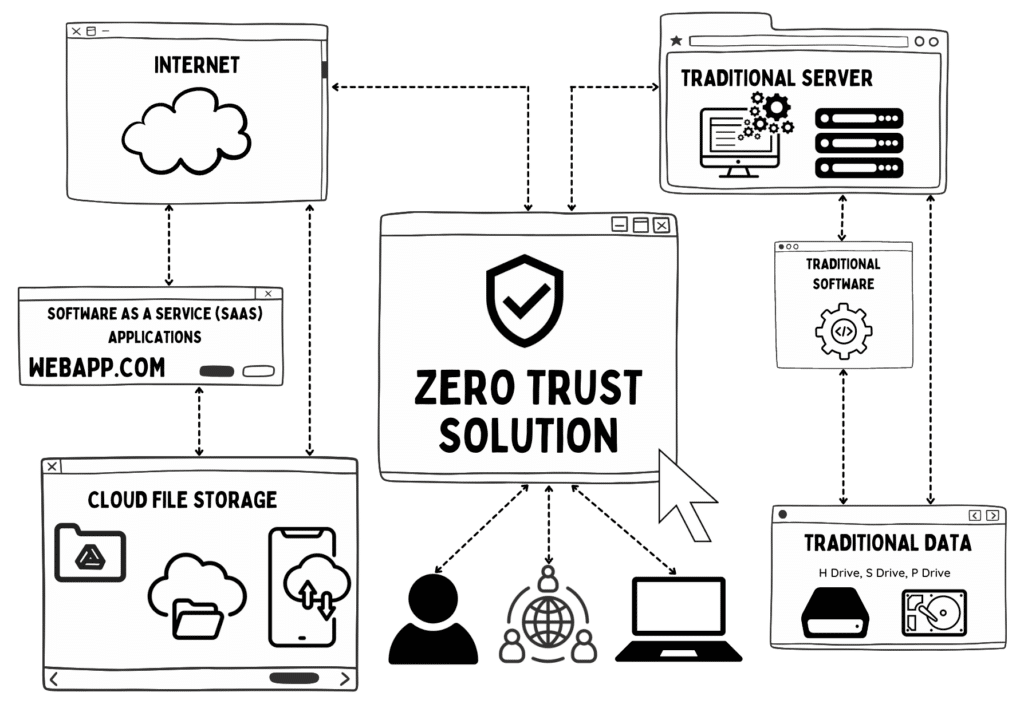
Secure Remote And Hybrid Work With Zero Trust Microsoft Learn In this blog series, i’m sharing how you can adjust your cybersecurity strategy to meet the requirements of a remote and or hybrid workforce, where employees use personal devices and cloud services outside the corporate network. In this blog series, we’ll discuss two zero trust business scenarios: enabling a more productive hybrid or remote work environment and rapidly modernizing your organization’s security posture through a zero trust architecture. If you’re rethinking your approach to hybrid work security right now, check out our complete guide to securing the modern workplace. alternatively, explore the security and compliance vendors baking ztna, sase, and intelligent processes into their toolkits and platforms. Zero trust is a cybersecurity philosophy that operates on a simple but powerful principle: “never trust, always verify.” in zero trust architecture, no user or device — whether inside or. Implement zero trust architecture in 2025 across hybrid cloud, remote work, and legacy systems. a step by step guide with practical deployment strategies. Advanced zero trust solutions can support all hybrid environments in which applications are provided via the cloud to ensure the security of today’s remote and onsite workforce. zero trust has become a standard approach for many organizations to secure network access for their remote workers.

Secure Remote And Hybrid Work With Zero Trust Microsoft Learn If you’re rethinking your approach to hybrid work security right now, check out our complete guide to securing the modern workplace. alternatively, explore the security and compliance vendors baking ztna, sase, and intelligent processes into their toolkits and platforms. Zero trust is a cybersecurity philosophy that operates on a simple but powerful principle: “never trust, always verify.” in zero trust architecture, no user or device — whether inside or. Implement zero trust architecture in 2025 across hybrid cloud, remote work, and legacy systems. a step by step guide with practical deployment strategies. Advanced zero trust solutions can support all hybrid environments in which applications are provided via the cloud to ensure the security of today’s remote and onsite workforce. zero trust has become a standard approach for many organizations to secure network access for their remote workers.

Secure Remote And Hybrid Work With Zero Trust Microsoft Learn Implement zero trust architecture in 2025 across hybrid cloud, remote work, and legacy systems. a step by step guide with practical deployment strategies. Advanced zero trust solutions can support all hybrid environments in which applications are provided via the cloud to ensure the security of today’s remote and onsite workforce. zero trust has become a standard approach for many organizations to secure network access for their remote workers.
Comments are closed.