How Your Org Looks To Cyber Criminals
Cyber Security Layers Cybercrime And Cyber Criminals Consider adopting this approach to clarify your ideas, focus your efforts, use your time and resources productively, and ultimately increase the chances of your project and cybercrime strategy succeeding. Law enforcement performs an essential role in achieving our nation’s cybersecurity objectives by investigating a wide range of cyber crimes, from theft and fraud to child exploitation, and apprehending and prosecuting those responsible.

Cyber Criminals Are Getting Faster Information Age Acs The convention is a comprehensive global treaty, which provides states with a range of essential tools and measures to combat the criminal use of information and communication technologies. Look at your organization from an outsider's perspective to identify vulnerabilities or gaps that can be exploited. conduct regular cybersecurity training and educate your staf on how to remain vigilant to suspicious emails, phone calls or text links. By disrupting cyber threats and prosecuting bad actors, the criminal division deters cybercrime, in some instances causing cybercrime groups to shutter in the wake of disruption actions. Collaborations between industry experts and the public sector are disrupting cybercriminals. here’s how this can be scaled up and accelerated. the internet allows criminals to operate seamlessly across borders, accessing a marketplace of victims anywhere, anytime and at scale.
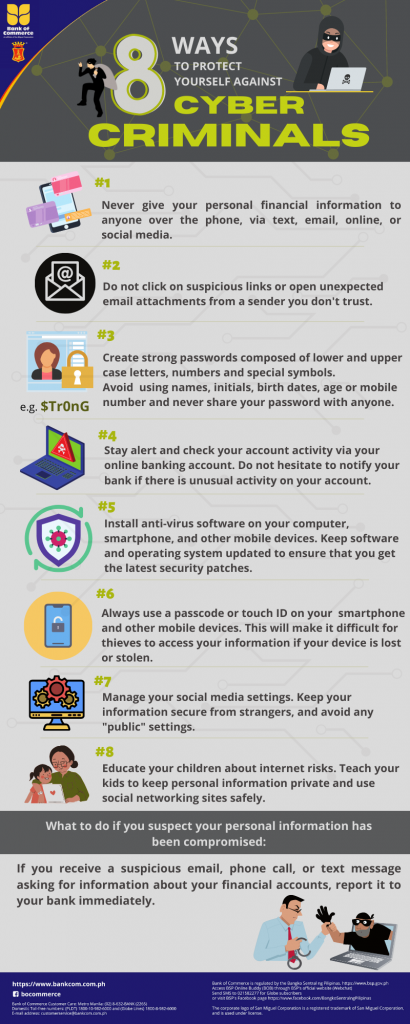
8 Ways To Protect Yourself Against Cyber Criminals Bank Of Commerce By disrupting cyber threats and prosecuting bad actors, the criminal division deters cybercrime, in some instances causing cybercrime groups to shutter in the wake of disruption actions. Collaborations between industry experts and the public sector are disrupting cybercriminals. here’s how this can be scaled up and accelerated. the internet allows criminals to operate seamlessly across borders, accessing a marketplace of victims anywhere, anytime and at scale. While many businesses still rely on reactive strategies, the most effective organizations take a proactive approach to cybersecurity risk management. a proactive cybersecurity strategy focuses on identifying risks before they become a breach, strengthening defenses, and continuously improving visibility across their organization’s it environment. Cyber security is on everyone's lips these days. there are regular headlines about criminal hackers breaking into organisations. a quick glance at the alarming figures reveals the scale of the threat: the fact that organisations are exposed to attacks on their it environment is nothing new. Targeted attacks are becoming pervasive. here's a look at how those targets are chosen and how your organization might avoid being one of them. Here’s a crafted list of things cybercriminals look for when selecting a target. hopefully, knowing this stuff can help you spot weaknesses, fix problems, and keep your organization safe.

Reduce The Impact Of Cyber Criminals For Your Organisation While many businesses still rely on reactive strategies, the most effective organizations take a proactive approach to cybersecurity risk management. a proactive cybersecurity strategy focuses on identifying risks before they become a breach, strengthening defenses, and continuously improving visibility across their organization’s it environment. Cyber security is on everyone's lips these days. there are regular headlines about criminal hackers breaking into organisations. a quick glance at the alarming figures reveals the scale of the threat: the fact that organisations are exposed to attacks on their it environment is nothing new. Targeted attacks are becoming pervasive. here's a look at how those targets are chosen and how your organization might avoid being one of them. Here’s a crafted list of things cybercriminals look for when selecting a target. hopefully, knowing this stuff can help you spot weaknesses, fix problems, and keep your organization safe.
Comments are closed.