How Tor Works Pptx
How Tor Works The document provides an overview of how the tor network functions, including its design and components like relays, encryption, and bridges. it discusses the importance of using tor for maintaining anonymity online and the potential vulnerabilities to the network from compromised isps or relays. Tor network is a group of volunteer operated servers. users connect through a series of virtual tunnels rather than making a direct connection, thus allowing organizations and individuals to share information over public networks without compromising their privacy.
Introduction To Tor How It Works And Why You Should Use It Explore the tor network: its architecture, encryption, users, and security risks. learn how tor provides online anonymity. Explore how tor works, bridge relays, network growth, exit nodes, timing attacks, tor browser, hidden services, and using tor as a socks5 proxy. learn about encryption keys, finding hidden services, and communicating securely online. What is the tor network? “the onion router” a distributed volunteer based network which uses random pathways and encryption to prevent traffic analysis. “the tor network is a group of volunteer operated servers that allows people to improve their privacy and security on the internet.” – the tor project website. Tor uses a technique called onion routing that encrypts and bounces communications through multiple nodes on the network to hide a user's location and usage. the document provides an overview of how tor works and maintains anonymity for users and dark web services.
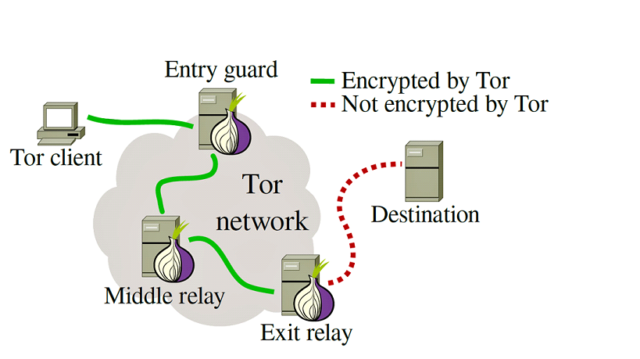
Tor Explained What Is Tor And How Does It Work Is It Illegal What is the tor network? “the onion router” a distributed volunteer based network which uses random pathways and encryption to prevent traffic analysis. “the tor network is a group of volunteer operated servers that allows people to improve their privacy and security on the internet.” – the tor project website. Tor uses a technique called onion routing that encrypts and bounces communications through multiple nodes on the network to hide a user's location and usage. the document provides an overview of how tor works and maintains anonymity for users and dark web services. Directory servers directories in tor are a small group of redundant, well known onion routers to track changes in network topology and node state each directory acts as an http server, clients fetch network info ors post signed statements to the directories directories must be synchronized tor assumes that a threshold of participants agree on. This page introduces the tor network a volunteer run system that protects privacy, resists censorship, and helps people communicate and browse anonymously. it explains what tor does, why it's needed, and how its distributed design keeps users safe. Individuals use tor to keep websites from tracking them, or to connect to those internet services blocked by their local internet providers. tor's hidden services let users publish web sites and other services without needing to reveal the location of the site. Explore the intricacies of the tor network with this professional powerpoint presentation. discover how tor enables anonymous browsing, its operational mechanisms, and its significance in online privacy.

How Tor Works Directory servers directories in tor are a small group of redundant, well known onion routers to track changes in network topology and node state each directory acts as an http server, clients fetch network info ors post signed statements to the directories directories must be synchronized tor assumes that a threshold of participants agree on. This page introduces the tor network a volunteer run system that protects privacy, resists censorship, and helps people communicate and browse anonymously. it explains what tor does, why it's needed, and how its distributed design keeps users safe. Individuals use tor to keep websites from tracking them, or to connect to those internet services blocked by their local internet providers. tor's hidden services let users publish web sites and other services without needing to reveal the location of the site. Explore the intricacies of the tor network with this professional powerpoint presentation. discover how tor enables anonymous browsing, its operational mechanisms, and its significance in online privacy.
How Tor Works Individuals use tor to keep websites from tracking them, or to connect to those internet services blocked by their local internet providers. tor's hidden services let users publish web sites and other services without needing to reveal the location of the site. Explore the intricacies of the tor network with this professional powerpoint presentation. discover how tor enables anonymous browsing, its operational mechanisms, and its significance in online privacy.
Comments are closed.