How Tor Works

How Tor Works This page introduces the tor network a volunteer run system that protects privacy, resists censorship, and helps people communicate and browse anonymously. it explains what tor does, why it's needed, and how its distributed design keeps users safe. This comprehensive guide will explain what tor is, how it works, and why it matters for digital privacy and freedom. we'll break down complex technical concepts into beginner friendly explanations, helping you understand the technology that enables millions of people to browse the internet anonymously.
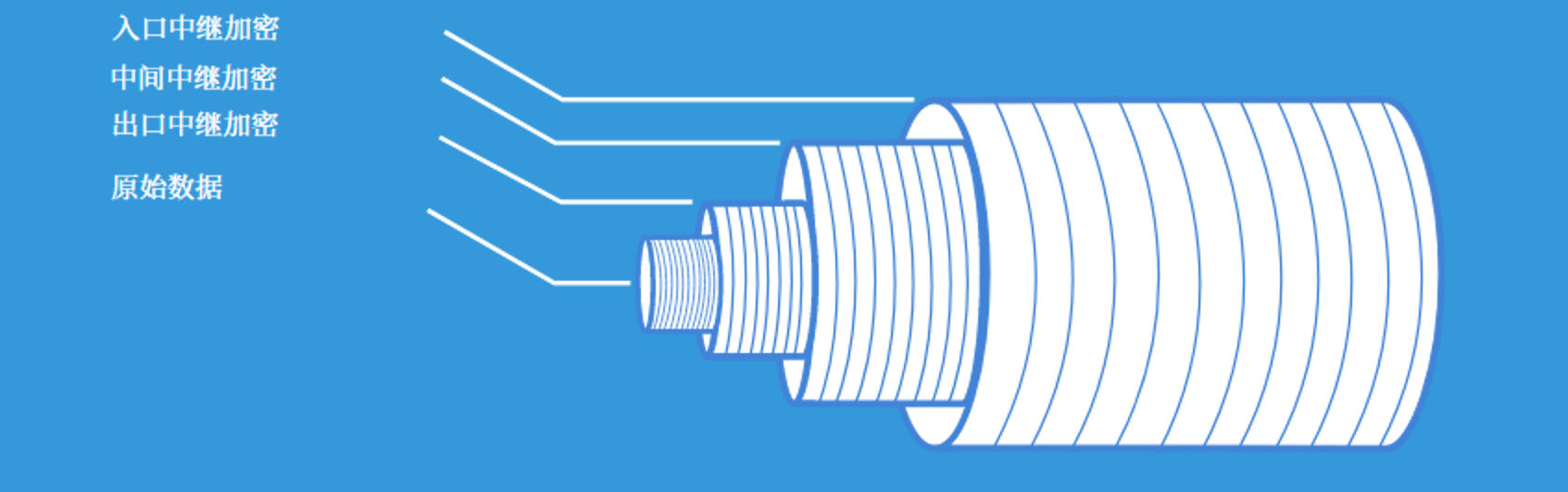
How Tor Works Working of tor the tor browser is based on a technology called onion routing which means a peer to peer relay network that enables users to surf the internet anonymously. So yes, criminals could in theory use tor, but they already have better options, and it seems unlikely that taking tor away from the world will stop them from doing their bad things. at the same time, tor and other privacy measures can fight identity theft, physical crimes like stalking, and so on. Tor is a network and a browser that anonymize your web traffic by encrypting and routing it through multiple servers. learn about tor's pros and cons, how it compares to vpns, and how to use it safely. Using tor, your computer never communicates with the server directly. tor creates a twisted path through 3 tor nodes and sends the data via that circuit. the core principle of tor is onion routing which is a technique for anonymous & secure communication over a public network.

How Tor Network Works Real Deep Web Tor is a network and a browser that anonymize your web traffic by encrypting and routing it through multiple servers. learn about tor's pros and cons, how it compares to vpns, and how to use it safely. Using tor, your computer never communicates with the server directly. tor creates a twisted path through 3 tor nodes and sends the data via that circuit. the core principle of tor is onion routing which is a technique for anonymous & secure communication over a public network. Learn how the tor browser works, what the onion network is, and how to use it for online anonymity and privacy. this comprehensive guide covers the pros and cons, installation, features, and tips of the tor browser. Learn what tor is, how it protects privacy, its uses beyond the dark web, and why it's essential for anonymous, censorship free browsing online. Learn what the tor browser is, how it works, whether it’s safe, and how to use it responsibly. get essential tips so you can browse online privately. Tor uses an open source browser that routes data through encrypted layers via nodes, masking the sender’s ip address. only the first and last nodes can reveal the sender’s identity and message content.
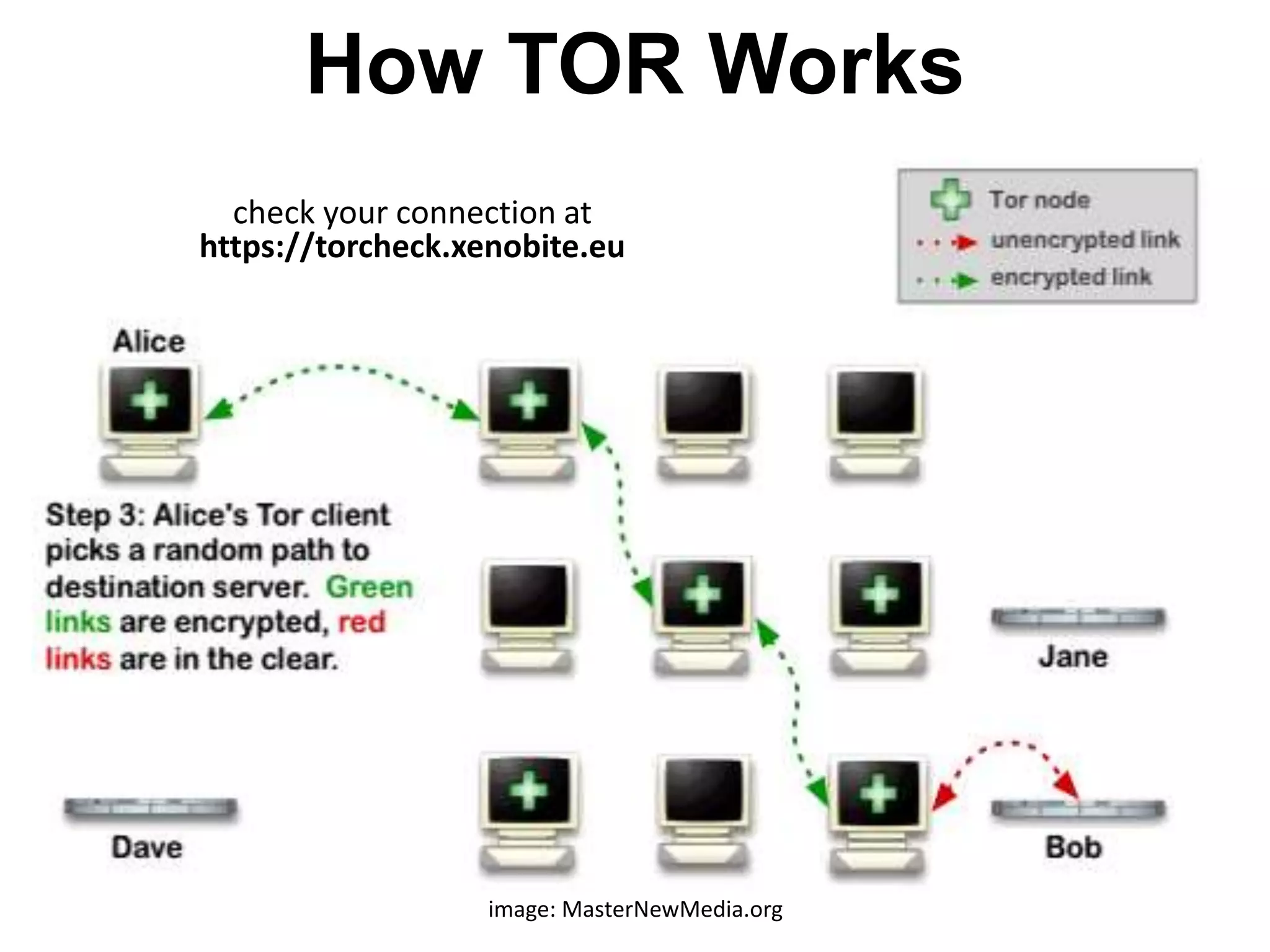
How Tor Works Pptx Learn how the tor browser works, what the onion network is, and how to use it for online anonymity and privacy. this comprehensive guide covers the pros and cons, installation, features, and tips of the tor browser. Learn what tor is, how it protects privacy, its uses beyond the dark web, and why it's essential for anonymous, censorship free browsing online. Learn what the tor browser is, how it works, whether it’s safe, and how to use it responsibly. get essential tips so you can browse online privately. Tor uses an open source browser that routes data through encrypted layers via nodes, masking the sender’s ip address. only the first and last nodes can reveal the sender’s identity and message content.
How Tor Works Pptx Learn what the tor browser is, how it works, whether it’s safe, and how to use it responsibly. get essential tips so you can browse online privately. Tor uses an open source browser that routes data through encrypted layers via nodes, masking the sender’s ip address. only the first and last nodes can reveal the sender’s identity and message content.
Comments are closed.