How To Use Jeb Auto Decrypt Strings In Protected Binary Code Jeb In
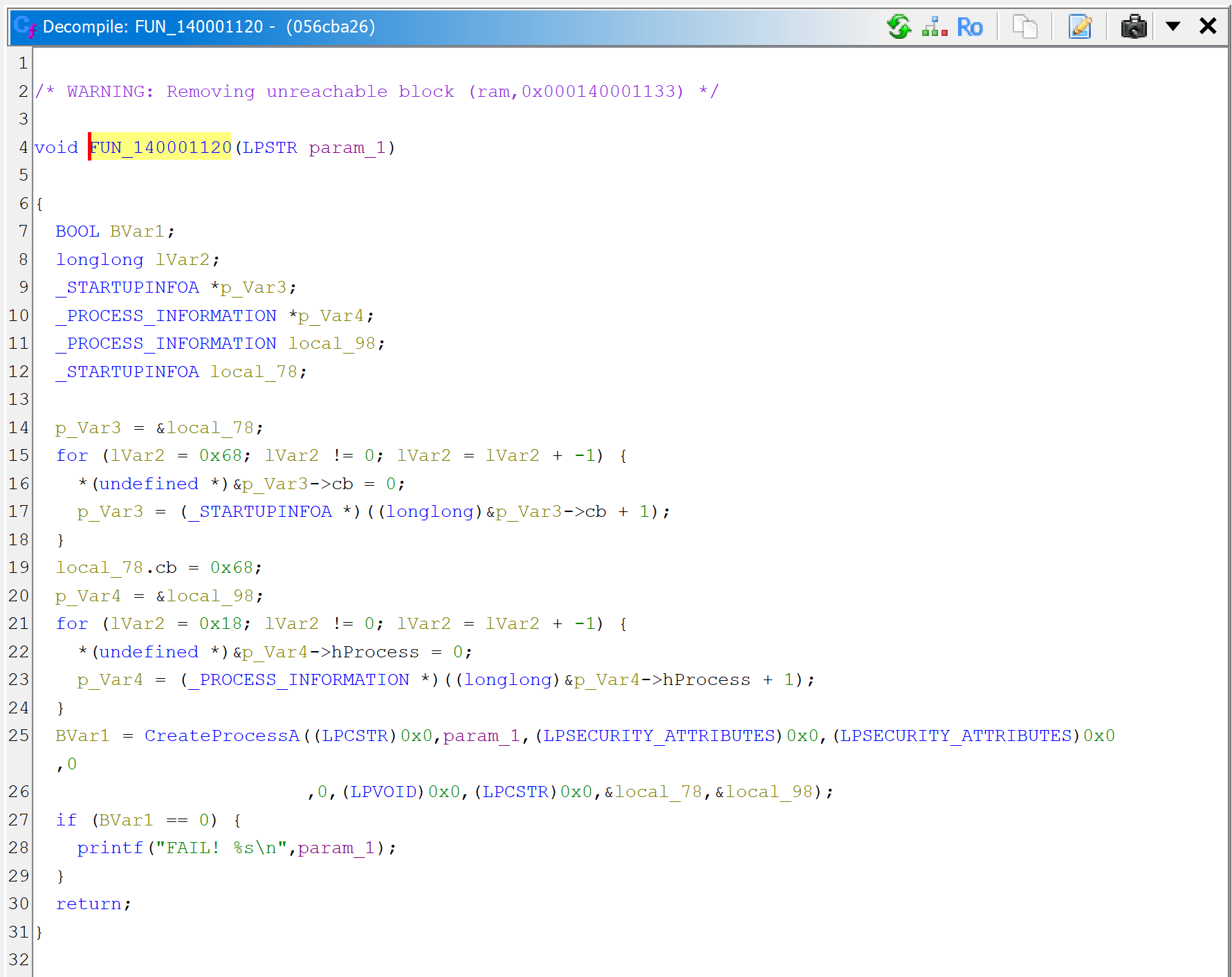
How To Use Jeb Auto Decrypt Strings In Protected Binary Code Jeb In How to use jeb – auto decrypt strings in protected binary code this is the second entry in our series showing how to use jeb and its well known and lesser known features to reverse engineer malware more efficiently. It is almost always preferable to perform dex deobfuscation of any kind (including string decryption) at the ir level, using dexdec's ir api.
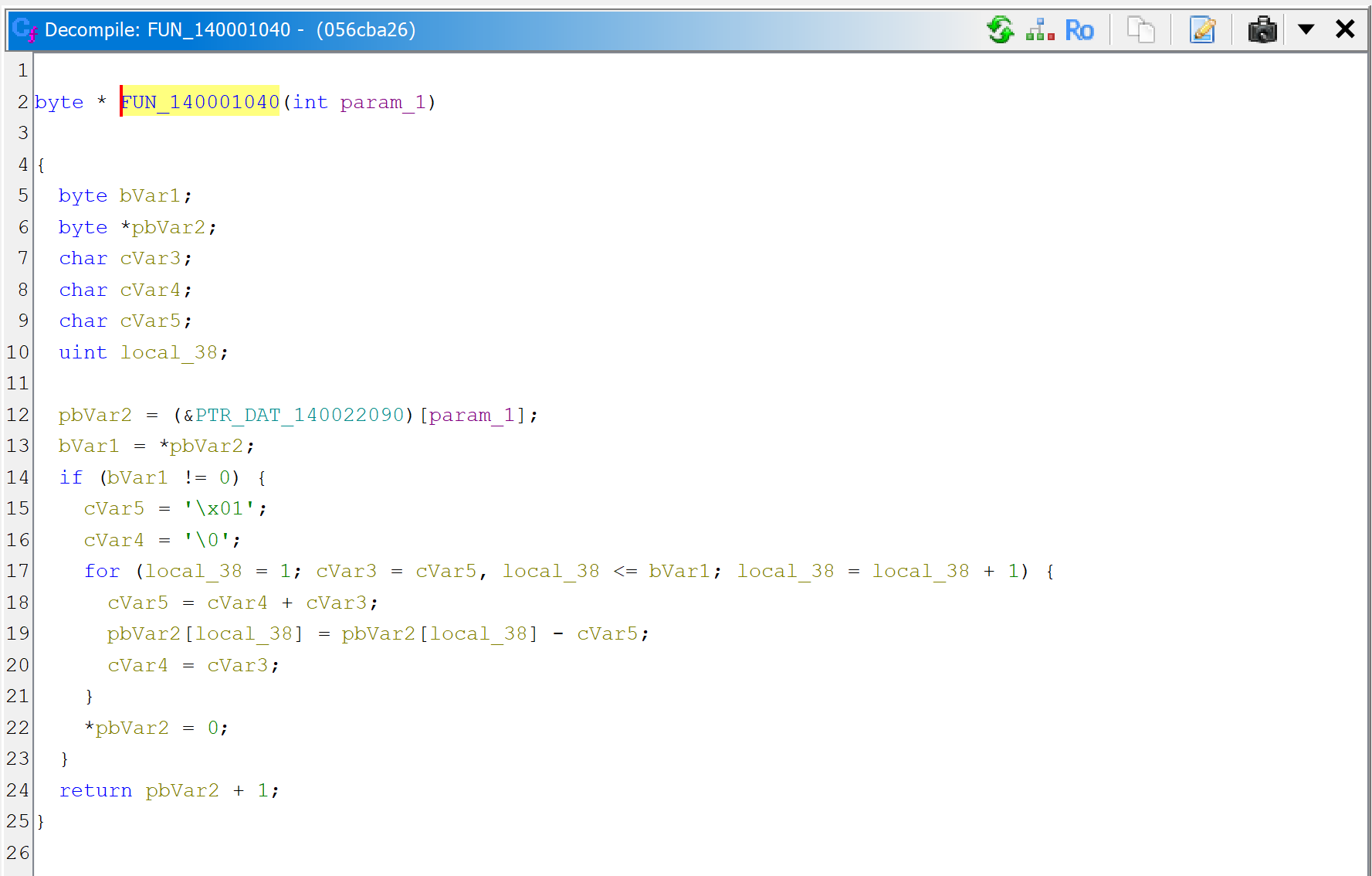
How To Use Jeb Auto Decrypt Strings In Protected Binary Code Jeb In So, we’ll do something simpler: the jeb user is expected to select the string to decrypt, the script will automatically decrypt the string and add a comment next to it with the. This is the second entry in our series showing how to use jeb and its well known and lesser known features to reverse engineer malware more efficiently. part 1 is here. How to use jeb – auto decrypt strings in protected binary code this is the second entry in our series showing how to use jeb and its well known and lesser known features to reverse engineer malware more efficiently. How to use jeb – auto decrypt strings in protected binary code this is the second entry in our series showing how to use jeb and its well known and lesser known features to reverse engineer malware more efficiently.
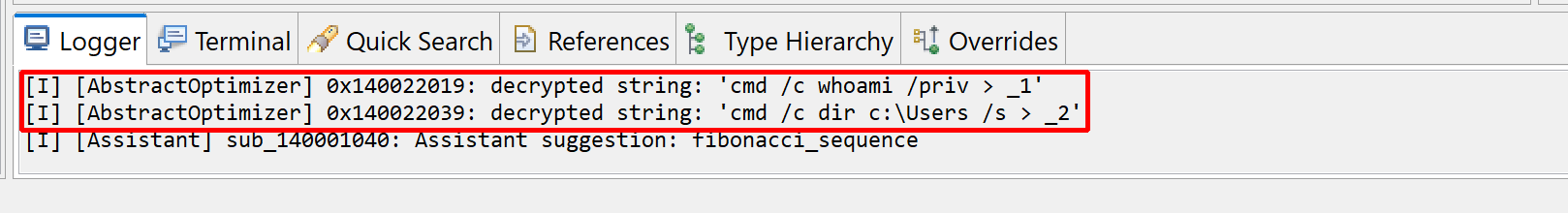
How To Use Jeb Auto Decrypt Strings In Protected Binary Code Jeb In How to use jeb – auto decrypt strings in protected binary code this is the second entry in our series showing how to use jeb and its well known and lesser known features to reverse engineer malware more efficiently. How to use jeb – auto decrypt strings in protected binary code this is the second entry in our series showing how to use jeb and its well known and lesser known features to reverse engineer malware more efficiently. How to use jeb – auto decrypt strings in protected binary code this is the second entry in our series showing how to use jeb and its well known and lesser known features to reverse engineer malware more efficiently. In this article, i want to demonstrate how to automatically generate frida hooks using jeb. the demo use case consists of generating a frida hook to bypass the tls pinning for okhttp. Hi! i'm writing a python script in jeb where i need to decrypt an aes encrypted string. in python. The hypothesis was that jeb somehow executes this code in its runtime. to verify this idea, we've prepared a modified version of the apk file by unpacking it with apktool, patching strings, and packing the apk back up.
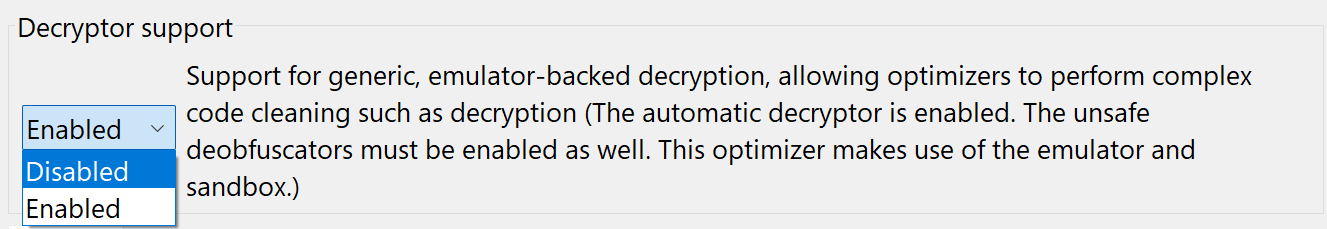
How To Use Jeb Auto Decrypt Strings In Protected Binary Code Jeb In How to use jeb – auto decrypt strings in protected binary code this is the second entry in our series showing how to use jeb and its well known and lesser known features to reverse engineer malware more efficiently. In this article, i want to demonstrate how to automatically generate frida hooks using jeb. the demo use case consists of generating a frida hook to bypass the tls pinning for okhttp. Hi! i'm writing a python script in jeb where i need to decrypt an aes encrypted string. in python. The hypothesis was that jeb somehow executes this code in its runtime. to verify this idea, we've prepared a modified version of the apk file by unpacking it with apktool, patching strings, and packing the apk back up.
Comments are closed.