How To Use Google Hacking Database 2023

Google Hacking Database Fcode Labs In this in depth guide, we‘ll delve into the world of google hacking and the ghdb. we‘ll explore its history, see real world examples of google hacking in action, and learn concrete steps you can take to protect your own systems and data. let‘s get started!. In this article, we will cover everything you need to know about ghdb, including its history, importance, applications, techniques, and how to use it effectively. we will also explore how to protect your systems from google dorking attacks and the legal implications of using ghdb.
Google Hacking Database Mojoplora The google hacking database is a powerful tool for cybersecurity professionals when used ethically. it enables researchers to discover vulnerabilities, assess security configurations, and gather osint. Basically, ghdb authorizes security researchers, penetration testers, and ethical hackers to aim for enhanced internet safety. in this blog, we will talk about the fundamentals of the ghdb, exploring its significance, benefits, and practical applications. In this short video, we will cover the basics of how to use the google hacking database, including how to find the ghdb, how to search for specific queries, and how to interpret the. The google hacking database (ghdb) is intended for educational and ethical purposes only. users of this database are advised to operate within the boundaries of the law and to use the information responsibly.
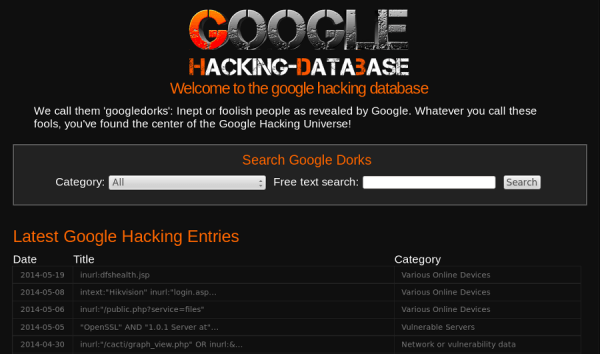
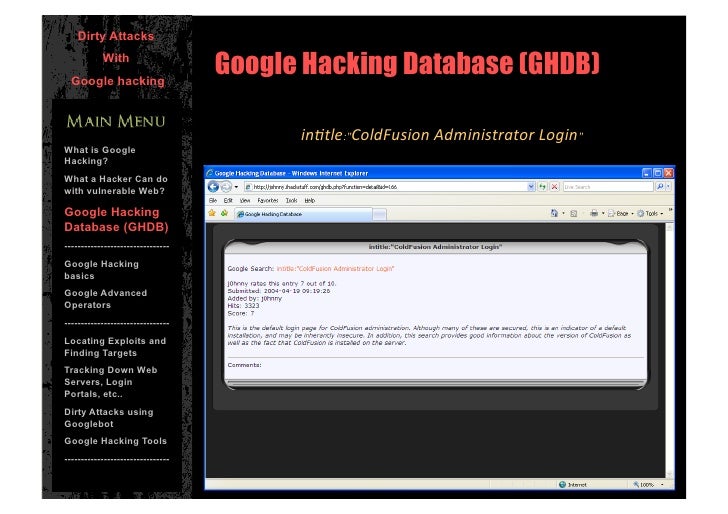
Google Hacking Database Bpotravel In this short video, we will cover the basics of how to use the google hacking database, including how to find the ghdb, how to search for specific queries, and how to interpret the. The google hacking database (ghdb) is intended for educational and ethical purposes only. users of this database are advised to operate within the boundaries of the law and to use the information responsibly. The ghdb is an index of search queries (we call them dorks) used to find publicly available information, intended for pentesters and security researchers. This blog explores the categories of ghdb, real life google hacking techniques, and methods to prevent such attacks, ensuring organizations can protect their sensitive information from being indexed by search engines. It’s a skill used by penetration testers, bug bounty hunters, and cybersecurity professionals to uncover hidden data and secure systems. in this guide, we’ll introduce you to a few essential google hacking tools, show you how to install them, and teach you how to use them effectively. Google dorking hacking is a method attackers use to find sensitive information concerning vulnerabilities in applications indexed by google.

Google Hacking Database Bpotravel The ghdb is an index of search queries (we call them dorks) used to find publicly available information, intended for pentesters and security researchers. This blog explores the categories of ghdb, real life google hacking techniques, and methods to prevent such attacks, ensuring organizations can protect their sensitive information from being indexed by search engines. It’s a skill used by penetration testers, bug bounty hunters, and cybersecurity professionals to uncover hidden data and secure systems. in this guide, we’ll introduce you to a few essential google hacking tools, show you how to install them, and teach you how to use them effectively. Google dorking hacking is a method attackers use to find sensitive information concerning vulnerabilities in applications indexed by google.

Google Hacking Database Bpotravel It’s a skill used by penetration testers, bug bounty hunters, and cybersecurity professionals to uncover hidden data and secure systems. in this guide, we’ll introduce you to a few essential google hacking tools, show you how to install them, and teach you how to use them effectively. Google dorking hacking is a method attackers use to find sensitive information concerning vulnerabilities in applications indexed by google.
Google Hacking Database Explore Dorks Security Vulnerabilities
Comments are closed.