How To Test For Weak Ssl Tls Https Ciphers
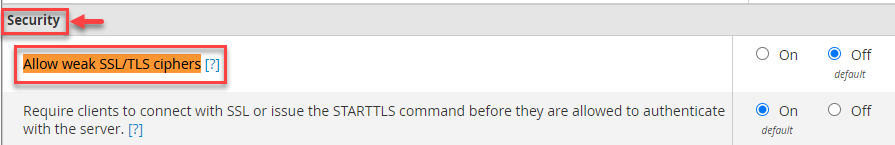
How To Allow Weak Ssl Tls Ciphers In Whm Eukhost It is important to check the ssl configuration being used to avoid putting in place cryptographic support which could be easily defeated. to reach this goal ssl based services should not offer the possibility to choose weak cipher suite. There are a large number of protocol versions, ciphers, and extensions supported by tls. many of these are considered to be legacy, and have cryptographic weaknesses, such as those listed below.

How To Allow Weak Ssl Tls Ciphers In Whm Eukhost It is important to check the ssl configuration being used to avoid putting in place cryptographic support which could be easily defeated. to reach this goal ssl based services should not offer the possibility to choose weak cipher suite. A misconfigured ssl protocol can lead to serious security issues, so regular reviews of the ssl configuration are key to identifying and eliminating weak cipher suites. Using the weak cipher suite tester is straightforward. follow these steps to audit any tls endpoint — from web servers to load balancers, email gateways, or vpn terminators. Check ssl tls services for vulnerabilities and weak ciphers with this online ssl scan. makes use of the excellent sslyze and openssl to gather the certificate details and measure security of the ssl tls implementation.
How To Disable Weak Ciphers In Ssl Tls Powershell Ninjaone Using the weak cipher suite tester is straightforward. follow these steps to audit any tls endpoint — from web servers to load balancers, email gateways, or vpn terminators. Check ssl tls services for vulnerabilities and weak ciphers with this online ssl scan. makes use of the excellent sslyze and openssl to gather the certificate details and measure security of the ssl tls implementation. Testssl.sh is a free and open source command line tool which checks a server’s support of tls ssl ciphers, protocols as well as recent cryptographic flaws and more. In this article, we will walk you through how to use owasp zap to test for weak ssl tls configurations in web application s, providing a step by step guide on how to set up and execute the tests, as well as interpret the results. This article provides a brief introduction to ssl tls networking, how to identify weak and insecure elements in your ssl setup, and what actions you can take to secure your system and protect user data. Identify weak tls ssl configurations including deprecated protocols, weak ciphers, and certificate issues. testing guide with testssl.sh and sslyze.
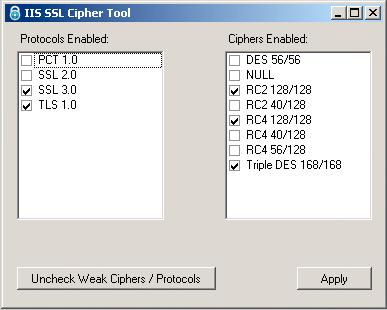
Windows App Disable Iis Sslv2 Ssl 3 And Weak Ciphers Enable Tls 1 2 Testssl.sh is a free and open source command line tool which checks a server’s support of tls ssl ciphers, protocols as well as recent cryptographic flaws and more. In this article, we will walk you through how to use owasp zap to test for weak ssl tls configurations in web application s, providing a step by step guide on how to set up and execute the tests, as well as interpret the results. This article provides a brief introduction to ssl tls networking, how to identify weak and insecure elements in your ssl setup, and what actions you can take to secure your system and protect user data. Identify weak tls ssl configurations including deprecated protocols, weak ciphers, and certificate issues. testing guide with testssl.sh and sslyze.
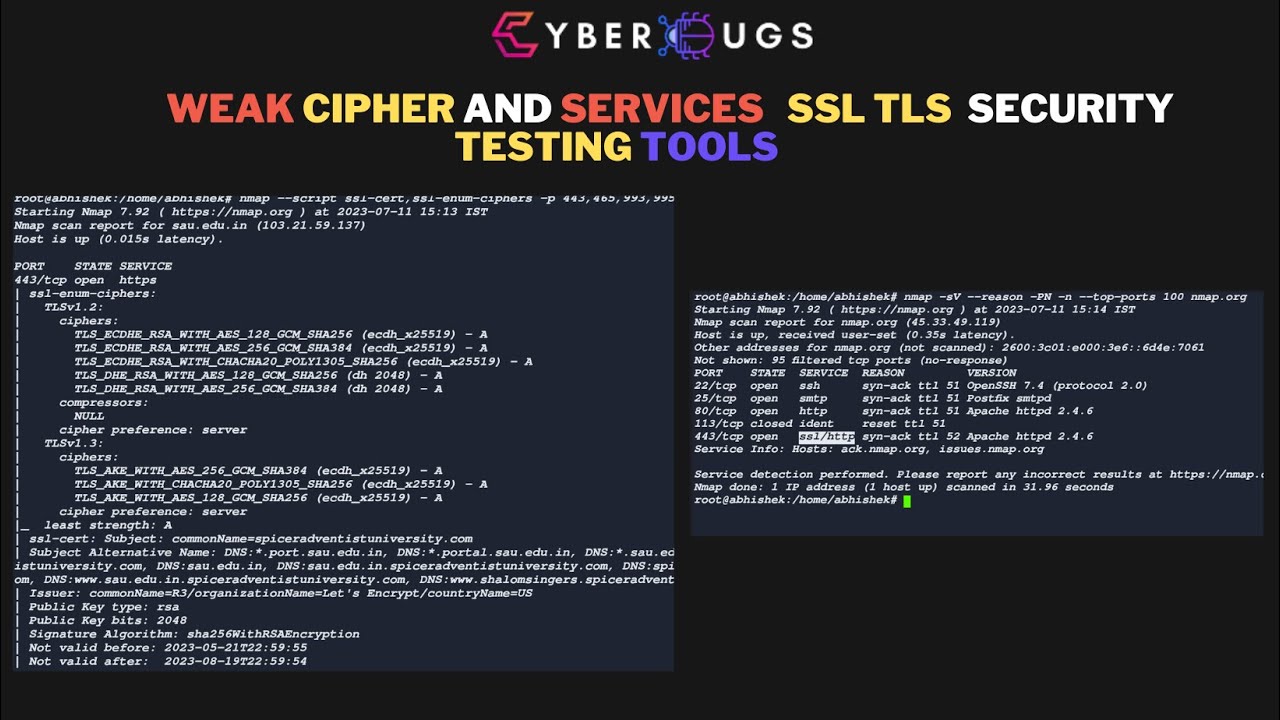
Disabling Weak Tls Ciphers For Port 443 In Esxi Blgqmg This article provides a brief introduction to ssl tls networking, how to identify weak and insecure elements in your ssl setup, and what actions you can take to secure your system and protect user data. Identify weak tls ssl configurations including deprecated protocols, weak ciphers, and certificate issues. testing guide with testssl.sh and sslyze.
Comments are closed.