How To Start Threat Intelligence
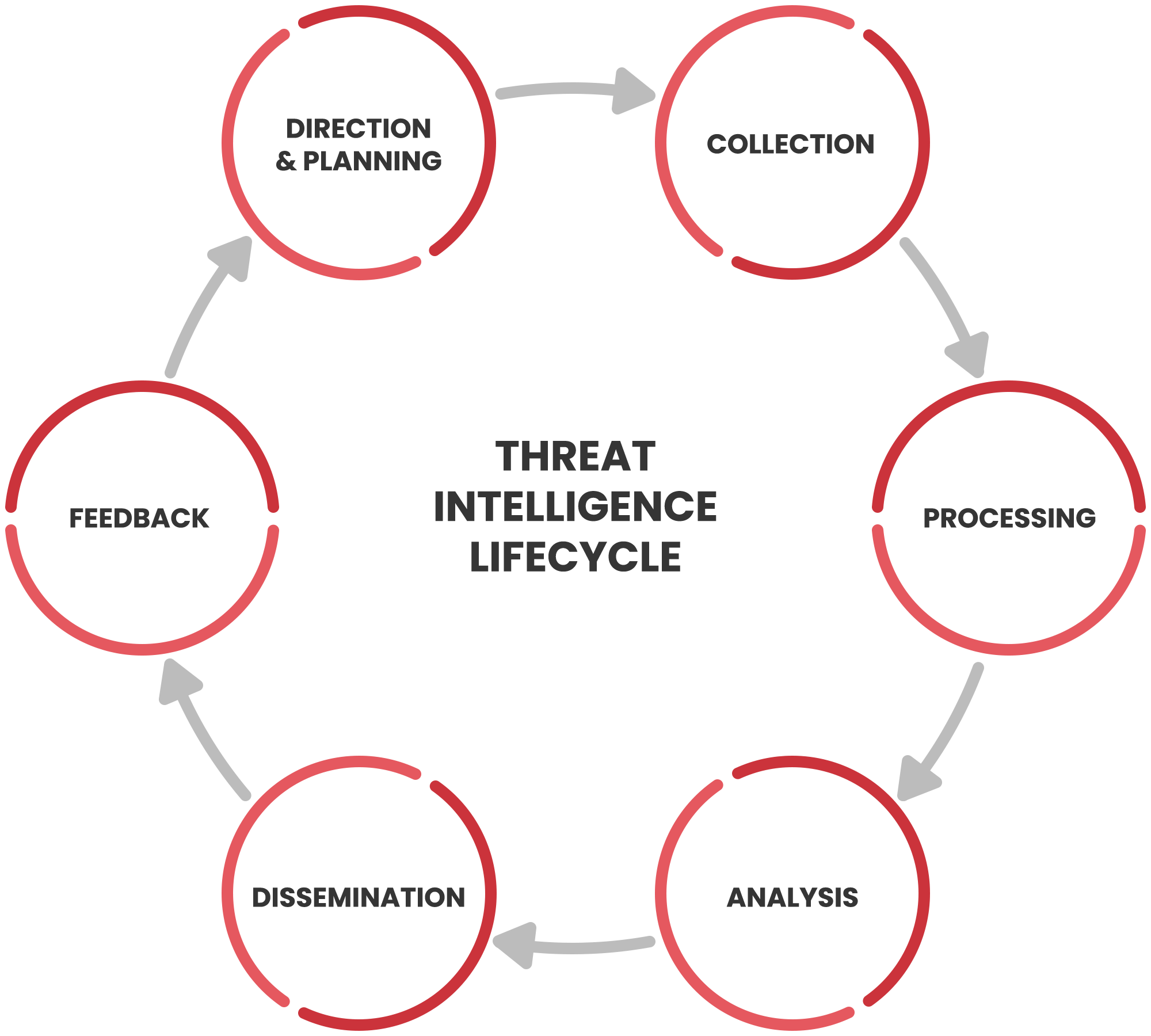
Threat Intelligence Rt Co Cybersecurity A well implemented cti program can help operationalize intelligence and generate actionable insights into the threat landscape, allowing organizations to proactively identify, understand, and. Step by step guide to establishing an effective threat intelligence program. learn how to collect, analyze, and act on cyber threat data.
Mastering Threat Intelligence Platforms Start Me In this comprehensive guide, we’ve covered the essential steps to build a threat intelligence program from scratch. if you’d like further details on any section or additional insights, feel. Follow a detailed roadmap to become a threat intelligence analyst with the skills, projects, and career moves that get results. Threat hunting is an essential component of your cybersecurity strategy. whether you're getting started or in an advanced state, this article will help you ramp up your threat intelligence program. what is threat hunting? the cybersecurity industry is shifting from a reactive to a proactive approach. To get started immediately, set a simple goal for the next 48 hours: track 10 suspicious ips or domains, map behaviors to three mitre att&ck techniques, and document your findings in a lab journal.

Mastering Threat Intelligence Platforms Start Me Threat hunting is an essential component of your cybersecurity strategy. whether you're getting started or in an advanced state, this article will help you ramp up your threat intelligence program. what is threat hunting? the cybersecurity industry is shifting from a reactive to a proactive approach. To get started immediately, set a simple goal for the next 48 hours: track 10 suspicious ips or domains, map behaviors to three mitre att&ck techniques, and document your findings in a lab journal. If you’re looking to start a career in threat intelligence in 2025, now is the right time to prepare. this guide will walk you through what the role involves, what skills and qualifications you need, and how to take your first steps. In this post, we’ll explore a step by step guide for setting up a threat intelligence program, a framework for integrating real time feeds into siem systems, and a playbook for handling zero day exploits. In this comprehensive guide, we will walk you through each step of creating a robust threat intelligence program, ensuring your digital assets and data remain secure. 1. understand your goals and needs. begin by clearly defining your organization’s goals and specific needs regarding cybersecurity. Learn how to build a successful threat intelligence program in six steps. from defining objectives to monitoring, enhance your organization's security posture.

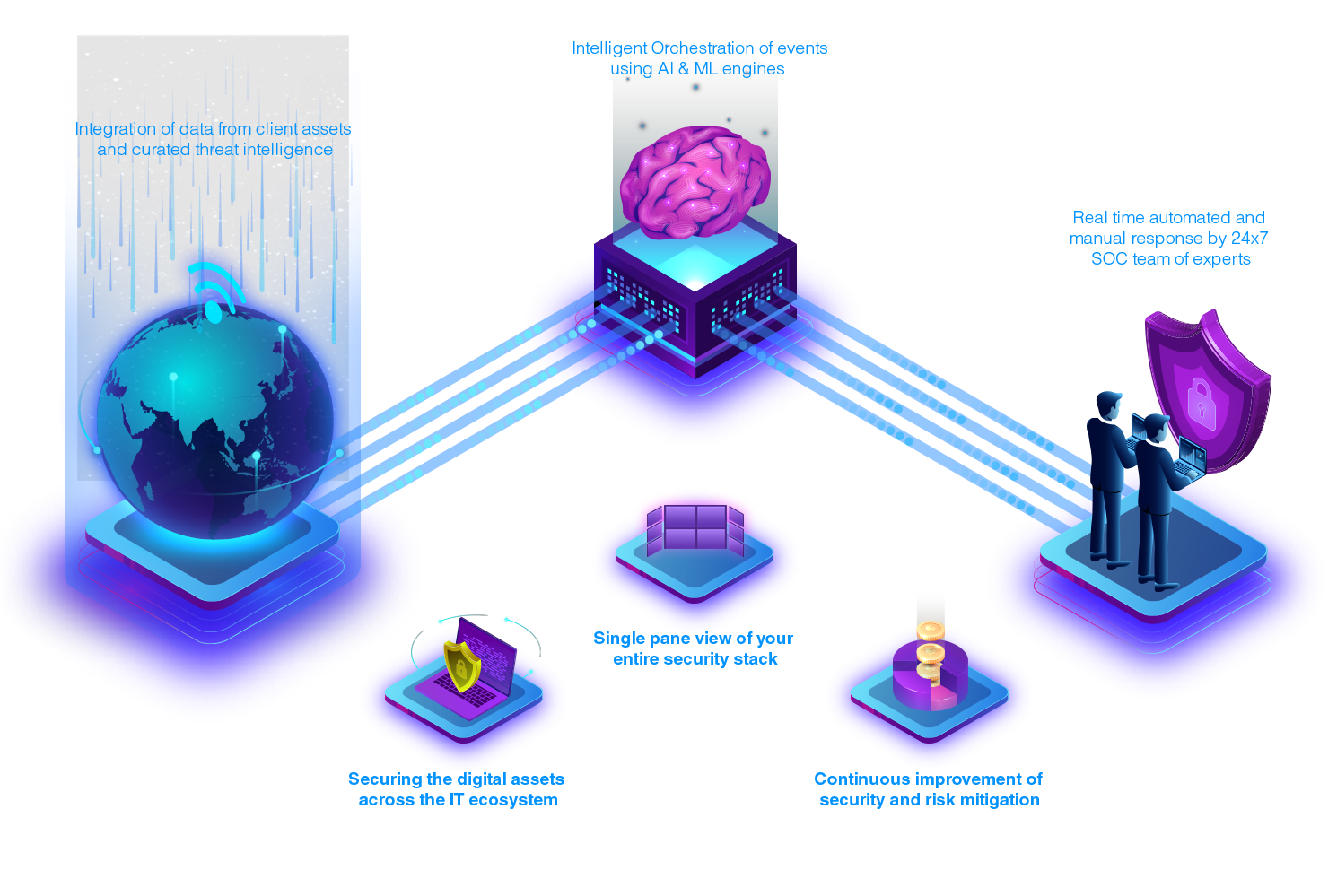
Threat Intelligence Platform Tip Threat Intel Platform If you’re looking to start a career in threat intelligence in 2025, now is the right time to prepare. this guide will walk you through what the role involves, what skills and qualifications you need, and how to take your first steps. In this post, we’ll explore a step by step guide for setting up a threat intelligence program, a framework for integrating real time feeds into siem systems, and a playbook for handling zero day exploits. In this comprehensive guide, we will walk you through each step of creating a robust threat intelligence program, ensuring your digital assets and data remain secure. 1. understand your goals and needs. begin by clearly defining your organization’s goals and specific needs regarding cybersecurity. Learn how to build a successful threat intelligence program in six steps. from defining objectives to monitoring, enhance your organization's security posture.

What Is Threat Intelligence Webopedia In this comprehensive guide, we will walk you through each step of creating a robust threat intelligence program, ensuring your digital assets and data remain secure. 1. understand your goals and needs. begin by clearly defining your organization’s goals and specific needs regarding cybersecurity. Learn how to build a successful threat intelligence program in six steps. from defining objectives to monitoring, enhance your organization's security posture.
Threat Intelligence Cyber Threat Intelligence Platform
Comments are closed.