How To Secure Amazon Ec2 With Sysdig

Security Tools For Containers Kubernetes And Cloud Sysdig Elastic compute cloud (ec2) is arguably one of the most popular aws services, and really needs no introduction but here is one anyway. with sysdig, you can secure ec2 by detecting threats and vulnerabilities, controlling configuration and permission risks, and meeting compliance requirements. With sysdig, you can secure ec2 by detecting threats and vulnerabilities, controlling configuration and permission risks, and meeting compliance requirements.
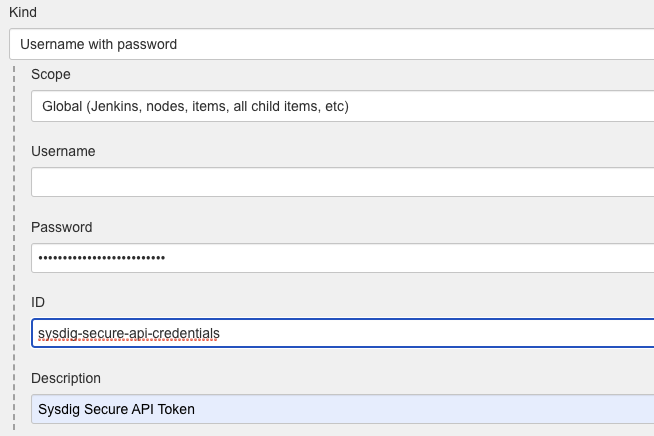
Sysdig Secure Container Image Scanner Jenkins Plugin Elastic compute cloud (ec2) is arguably one of the most popular aws services. with sysdig, you can secure ec2 by detecting threats and vulnerabilities, controlling configuration and permission risks, and meeting compliance requirements. Although this workshop approaches security from a sysdig centric perspective, the concepts and practices included are useful for anyone interested in learning how to secure cloud services and containers. Today, we will uncover how changes in your aws ec2 configuration can create major security holes. we will then hunt for these high risk configuration events using native tools, and then we will compare this to how sysdig secure helps in these situations. Check out this recent article from sysdig to learn methods for determining which events are actual threats and how stream detection helps with #threatdetection.
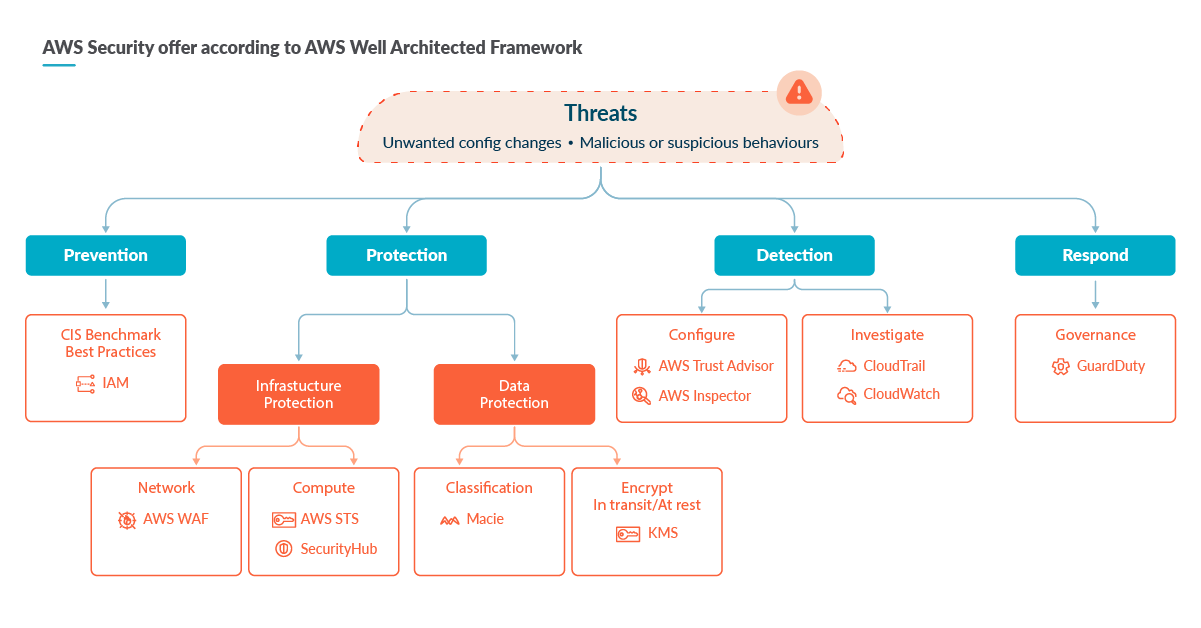
Improving Aws Security Services With Sysdig Secure Sysdig Today, we will uncover how changes in your aws ec2 configuration can create major security holes. we will then hunt for these high risk configuration events using native tools, and then we will compare this to how sysdig secure helps in these situations. Check out this recent article from sysdig to learn methods for determining which events are actual threats and how stream detection helps with #threatdetection. In this workshop, you'll experience some of the security challenges of kubernetes eks first hand and how sysdig can help. we have provisioned a separate eks cluster and ec2 instance (to serve as a jumpbox bastion) for each of you. Protect your aws workloads in real time with runtime security built on falco, the open standard for cloud threat detection. get a comprehensive view into access permissions across your aws accounts, eliminate excessive permissions, and enforce least privilege. This section explains how to install the sysdig agent container on each host within your ecs cluster. after installation, the agent will automatically begin runtime threat detection across all hosts, services, and tasks. This topic describes the process of connecting your aws environment to sysdig. you can connect single accounts or entire organizations using terraform or cloudformation.

Improving Aws Security Services With Sysdig Secure Sysdig In this workshop, you'll experience some of the security challenges of kubernetes eks first hand and how sysdig can help. we have provisioned a separate eks cluster and ec2 instance (to serve as a jumpbox bastion) for each of you. Protect your aws workloads in real time with runtime security built on falco, the open standard for cloud threat detection. get a comprehensive view into access permissions across your aws accounts, eliminate excessive permissions, and enforce least privilege. This section explains how to install the sysdig agent container on each host within your ecs cluster. after installation, the agent will automatically begin runtime threat detection across all hosts, services, and tasks. This topic describes the process of connecting your aws environment to sysdig. you can connect single accounts or entire organizations using terraform or cloudformation.

Prioritize Alerts And Findings With Sysdig Secure Sysdig This section explains how to install the sysdig agent container on each host within your ecs cluster. after installation, the agent will automatically begin runtime threat detection across all hosts, services, and tasks. This topic describes the process of connecting your aws environment to sysdig. you can connect single accounts or entire organizations using terraform or cloudformation.
Comments are closed.