How To Remove Ghostlocker Ransomware And Decrypt Ghost Files Bugsfighter

How To Remove Ghostlocker Ransomware And Decrypt Ghost Files Bugsfighter This tutorial will help you remove ghostlocker ransomware and decrypt .ghost files in windows 11 or windows 10. Removing ghostlocker ransomware from the operating system will prevent it from further encryptions. unfortunately, removal will not restore already locked files. the sole solution is to recover the data from a backup (if one was created prior and is stored elsewhere).
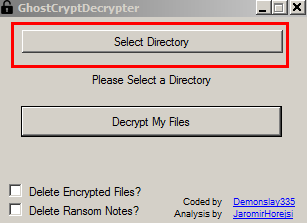
Remove Ghostcrypt Crypto Virus And Decrypt Z81928819 Encrypted Files Don’t let ghostlocker ransomware haunt your network. uncover its silent infiltration, ransom tricks, and best strategies to block this spooky threat. Have you had files encrypted by ghostlocker ransomware? our specialized solutions can efficiently restore your information. if you have been affected by ghostlocker ransomware, it is essential to act immediately to recover your files. Learn how to remove ransomware and download free decryption tools to get your files back. powered by kaspersky. The message delivered by the ghostlocker ransomware warns victims that their files have been enciphered using strong cryptographic algorithms, namely rsa 2048 and aes 12, and additionally, sensitive data has been exfiltrated from their system.
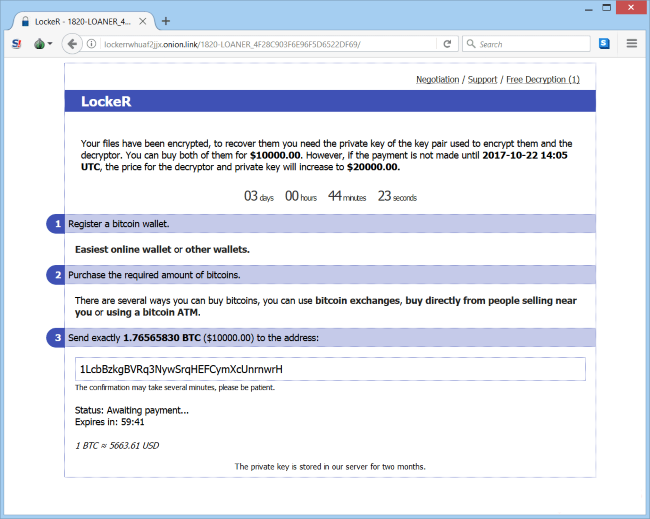
How To Remove Locker Ransomware And Decrypt Files Learn how to remove ransomware and download free decryption tools to get your files back. powered by kaspersky. The message delivered by the ghostlocker ransomware warns victims that their files have been enciphered using strong cryptographic algorithms, namely rsa 2048 and aes 12, and additionally, sensitive data has been exfiltrated from their system. Ransomware removal is challenging, but not impossible. learn how to remove ransomware and take measures to prevent infection in the first place. Our free ransomware decryption tools can help decrypt files encrypted by the following forms of ransomware. just click a name to see the signs of infection and get our free fix. To learn how to implement a series of security controls to reduce the impact of ransomware attacks and potentially avoid the need for decryption tools, read this post. Ghostlocker has the functionality for delayed encryption, privilege escalation and the ability to kill processes and services on the infected hosts, among others. upon completing the encryption process the malware will append .ghost extension to the locked files.
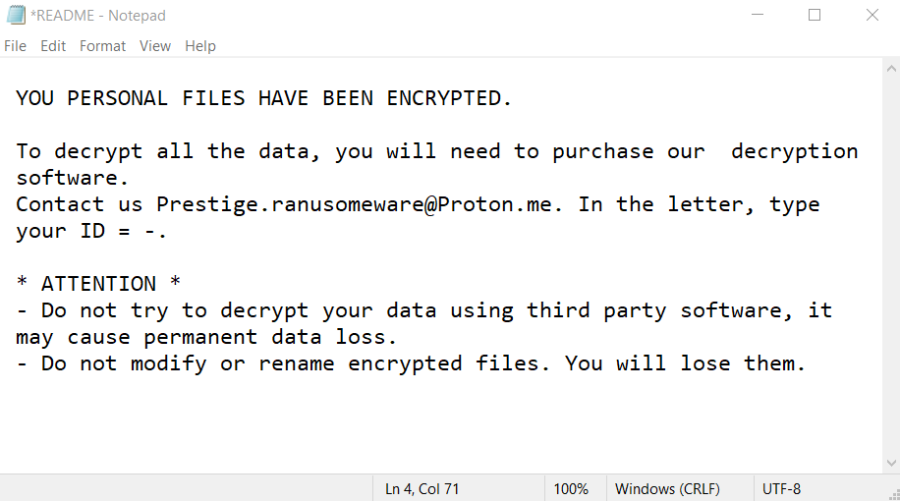
How To Remove Prestige Ransomware And Decrypt Enc Files Bugsfighter Ransomware removal is challenging, but not impossible. learn how to remove ransomware and take measures to prevent infection in the first place. Our free ransomware decryption tools can help decrypt files encrypted by the following forms of ransomware. just click a name to see the signs of infection and get our free fix. To learn how to implement a series of security controls to reduce the impact of ransomware attacks and potentially avoid the need for decryption tools, read this post. Ghostlocker has the functionality for delayed encryption, privilege escalation and the ability to kill processes and services on the infected hosts, among others. upon completing the encryption process the malware will append .ghost extension to the locked files.

How To Remove Shrinklocker Ransomware And Decrypt Your Files Bugsfighter To learn how to implement a series of security controls to reduce the impact of ransomware attacks and potentially avoid the need for decryption tools, read this post. Ghostlocker has the functionality for delayed encryption, privilege escalation and the ability to kill processes and services on the infected hosts, among others. upon completing the encryption process the malware will append .ghost extension to the locked files.
Comments are closed.