How To Recover A Deleted Process Binary On Linux Linux Process Forensics

Deleted Process Binary Attack On Linux Sandfly Security In this detailed guide, we explore how to recover deleted files from running processes on linux by leveraging the proc filesystem. You can easily recover a deleted linux process binary that has been removed by malware or other malcious actor. we'll show you how to do it.
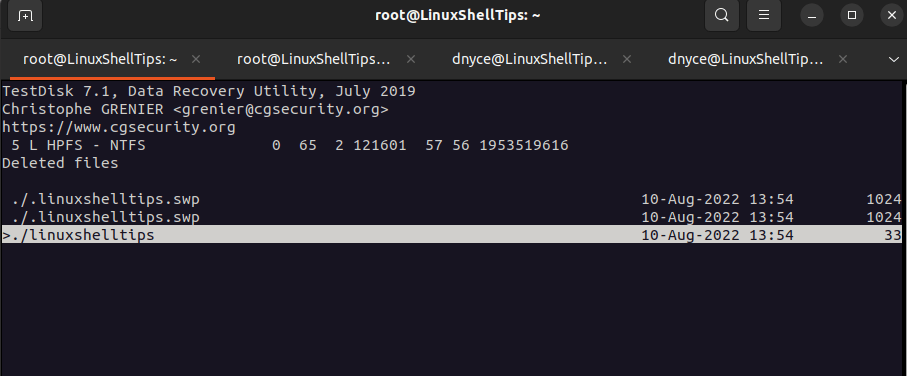
How To Recover Lost And Deleted Data In Linux Now that we’ve saved the linux binary somewhere off the system, we can recover the hashes easily. if you are using netcat to simulate the attack, you can recover the deleted binary and run a hash on the system netcat command and the recovered binary and see they match. I have a process running very long time. i accidentally deleted the binary executable file of the process. since the process is still running and doesn't get affected, there must be the original. This is because the underlying inode, which stores the file’s data and metadata, remains intact as long as the process is running. by leveraging linux’s proc
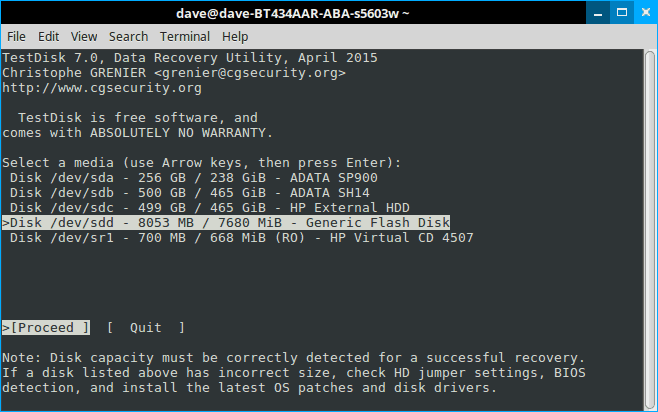
How To Recover Deleted Files In Linux Beginner S Guide This is because the underlying inode, which stores the file’s data and metadata, remains intact as long as the process is running. by leveraging linux’s proc
Comments are closed.