How To Protect Ssh Servers With Duo Network Gateway
How To Configure Duo Network Gateway Ssh Part 2 Identify the ssh servers you'd like to protect with duo network gateway and make sure that duo network gateway is able to communicate locally with each server over the ssh ports they are configured to use. Duo network gateway (dng) allows your users to access your on premises websites, web applications, and ssh servers without having to worry about managing vpn credentials, while also.

Duo Network Gateway Pomerium This section describes steps for adding protected ssh applications to a dng deployed within secure firewall cloud native. Duo, in addition to providing stronger user authentication, also provides policy authorization, such as authentication policy control and trusted endpoint verification, before permitting network access to the protected ssh host. The video shows you how to allow remote user to securely access internal ssh services using duo network gateway. we will leverage duo network gateway we installed in the previous lab and enable ssh relay application. Dng is a reverse proxy that allows users to access your on premises websites, web applications, and certain transmission control protocol or tcp services (rdp, ssh) without having to worry about managing vpn credentials, while also adding login security with the duo prompt.
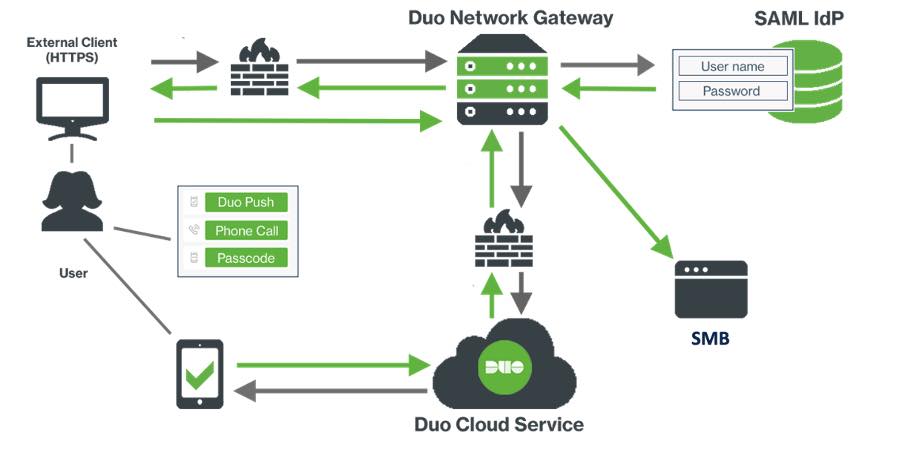
Announcing Ga Of Smb Support For Duo Network Gateway Duo Security The video shows you how to allow remote user to securely access internal ssh services using duo network gateway. we will leverage duo network gateway we installed in the previous lab and enable ssh relay application. Dng is a reverse proxy that allows users to access your on premises websites, web applications, and certain transmission control protocol or tcp services (rdp, ssh) without having to worry about managing vpn credentials, while also adding login security with the duo prompt. This tutorial shows how to compile and configure duo unix to protect ssh logins with system password duo mobile push. it covers duo portal preparation, source installation, and all necessary server side configuration files. In this video, we take a look at how to configure the duo network gateway to protect remote access smb file shares without the need for a vpn. youtu.be b0filq4vtzw. To protect remote access via ssh, use login duo. to enable two factor authentication for any ssh login method (password, pubkey, etc.) for any user, edit your sshd config (usually in etc or etc ssh) to add the following line:. The ssh servers yaml map allows you to define ssh servers to protect with duo network gateway. create separate maps within ssh servers for each set of ssh servers you'd like to protect.

Duo Network Gateway High Availability At Elsie Tucker Blog This tutorial shows how to compile and configure duo unix to protect ssh logins with system password duo mobile push. it covers duo portal preparation, source installation, and all necessary server side configuration files. In this video, we take a look at how to configure the duo network gateway to protect remote access smb file shares without the need for a vpn. youtu.be b0filq4vtzw. To protect remote access via ssh, use login duo. to enable two factor authentication for any ssh login method (password, pubkey, etc.) for any user, edit your sshd config (usually in etc or etc ssh) to add the following line:. The ssh servers yaml map allows you to define ssh servers to protect with duo network gateway. create separate maps within ssh servers for each set of ssh servers you'd like to protect.
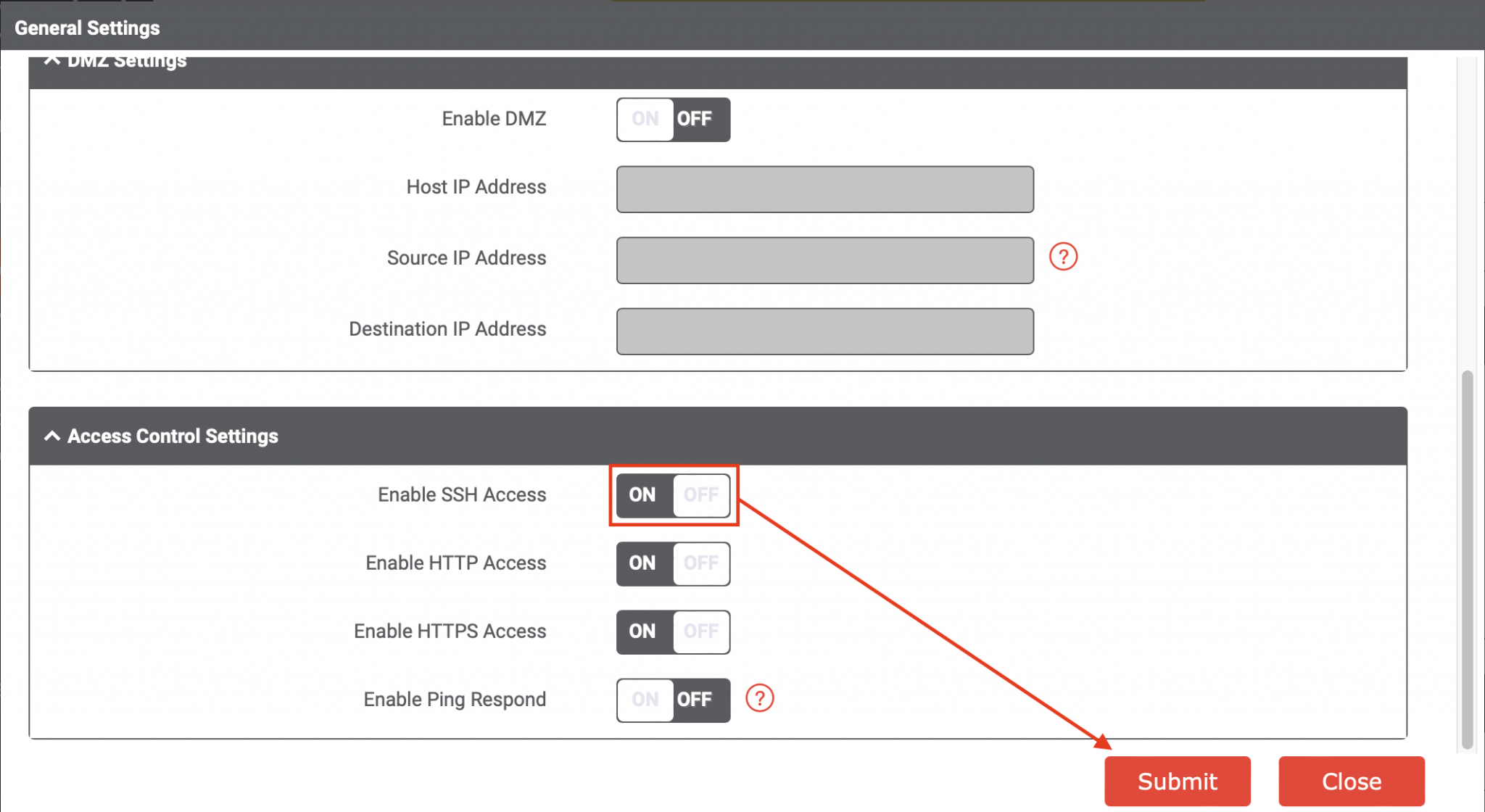
Ssh Into Your Iot Enterprise Gateway Ncd Io To protect remote access via ssh, use login duo. to enable two factor authentication for any ssh login method (password, pubkey, etc.) for any user, edit your sshd config (usually in etc or etc ssh) to add the following line:. The ssh servers yaml map allows you to define ssh servers to protect with duo network gateway. create separate maps within ssh servers for each set of ssh servers you'd like to protect.
How We Deployed Duo 2fa For Ssh To 600 Ubiquiti Servers
Comments are closed.