How To Prevent Memory Corruption Risks Labex

How To Prevent Memory Corruption Risks Labex This comprehensive tutorial explores essential techniques and best practices for preventing memory related risks in c development, providing developers with practical strategies to write more robust and secure code. Memory safe programming languages, such as rust and go, are designed to prevent common memory corruption issues like buffer overflows and use after free vulnerabilities.
How To Prevent Memory Corruption Risks Labex Adding flash programming safeguards to the firmware will reduce the risk of problems and ensure robust field updates. the following material increases firmware robustness through understanding of the potential issues and provides methods to prevent them. By leveraging static and dynamic analysis tools, following good coding practices, and using memory safe techniques like smart pointers and automatic memory management, developers can significantly reduce the risk of memory corruption and improve the stability and security of their applications. Learn what causes memory leaks and corruption in operating system memory management and how to prevent them using debugging tools, memory protection, and good programming practices. Learn what memory corruption vulnerabilities are, how they expose it infrastructure to attacks, and the best practices for defending against buffer overflows, dangling pointers, and use after free exploits.
Labex Learn To Code With Ai And Hands On Labs Learn what causes memory leaks and corruption in operating system memory management and how to prevent them using debugging tools, memory protection, and good programming practices. Learn what memory corruption vulnerabilities are, how they expose it infrastructure to attacks, and the best practices for defending against buffer overflows, dangling pointers, and use after free exploits. Buffer overflows and use after free errors are examples of common memory corruption vulnerabilities. learn how to mitigate memory safety vulnerabilities at runtime. The aim of this article is to provide a software method that explains how to deal with corruption of memory data sets stored in non volatile devices, such as small eeprom or flash memories. Learn how to prevent data corruption with strategies like read only mounts, single writer principle, and regular backups for safer file access. Learn essential c stack memory management techniques to prevent unintended modifications, protect program integrity, and avoid potential memory related errors in software development.
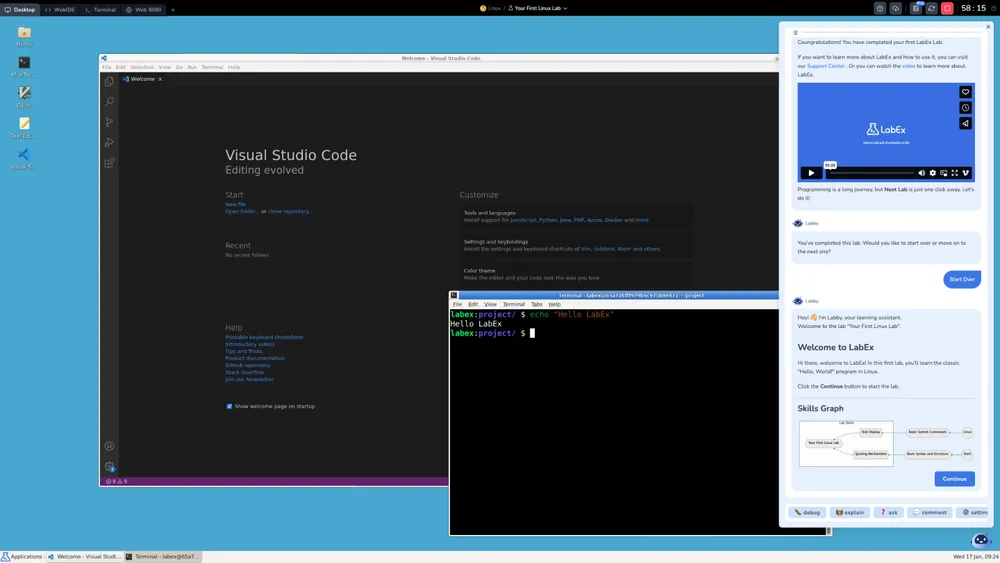
Free Linux Devops Cybersecurity Labs Labex Buffer overflows and use after free errors are examples of common memory corruption vulnerabilities. learn how to mitigate memory safety vulnerabilities at runtime. The aim of this article is to provide a software method that explains how to deal with corruption of memory data sets stored in non volatile devices, such as small eeprom or flash memories. Learn how to prevent data corruption with strategies like read only mounts, single writer principle, and regular backups for safer file access. Learn essential c stack memory management techniques to prevent unintended modifications, protect program integrity, and avoid potential memory related errors in software development.
Database Exercises Database Challenges Labex Learn how to prevent data corruption with strategies like read only mounts, single writer principle, and regular backups for safer file access. Learn essential c stack memory management techniques to prevent unintended modifications, protect program integrity, and avoid potential memory related errors in software development.

News Labex
Comments are closed.