How To Patch Using Ghidra
Stream Patch Notes Ghidra By Prime Listen Online For Free On Soundcloud To patch an instruction, right click on the instruction you want to modify and go to “patch instruction”. from there, you will see textboxes that you can type into. In this step by step walkthrough i reverse engineer a small windows gui application in ghidra, locate a simple xor checker, and apply a binary patch to change the program’s behavior.
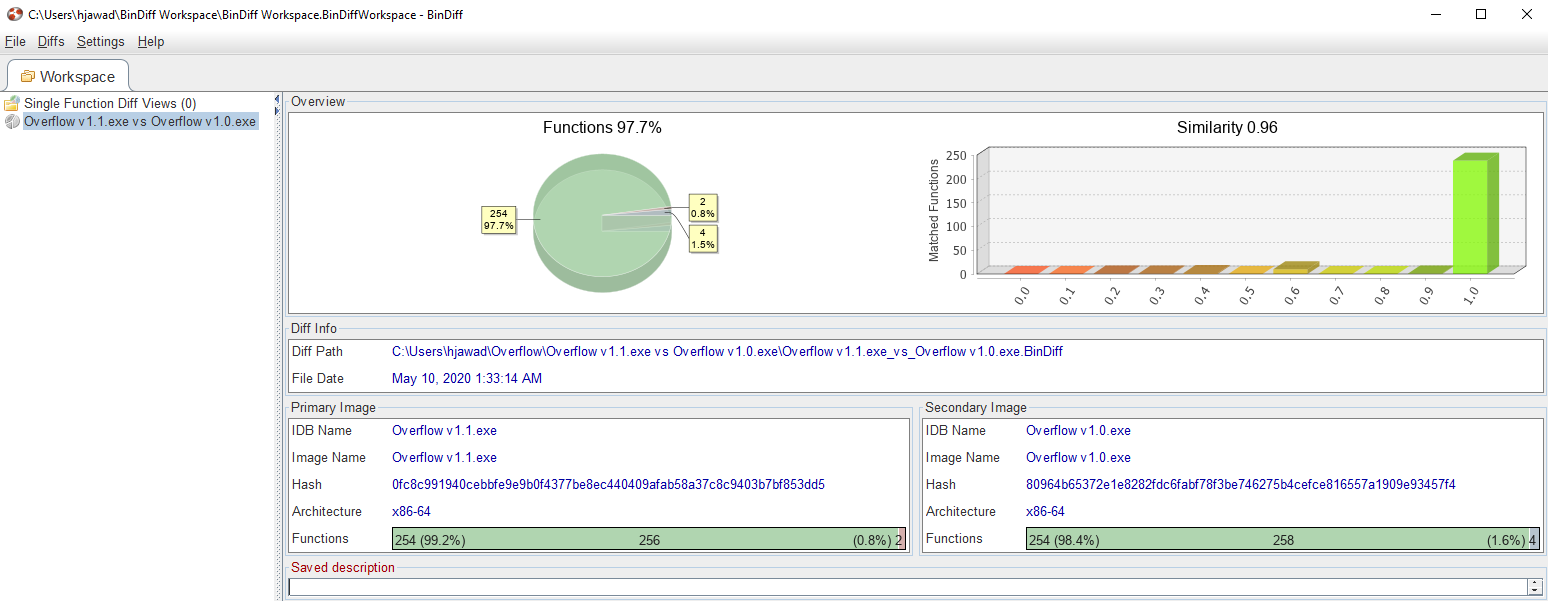
Patch Diffing With Ghidra Low Level Shenanigans Longer patches can be written into a code cave along with appropriate branching instructions to insert the patch code into the right code path. let’s take an example to see this process in action. This walk through of the beginner reverse engineering challenge “behindthescenes” from hackthebox demonstrates how to patch a binary in ghidra, and with python. We have learned how to use ghidra to reverse engineer a program and recreate the binary patch from part 5 for our case study. next time, we will study an esoteric but extremely powerful reverse engineering technique where we will slice an executable file back into relocatable object files. This repository contains reverse engineering notes and guides for educational purposes, using open source tools such as ghidra to pry into binaries for the nintendo switch.
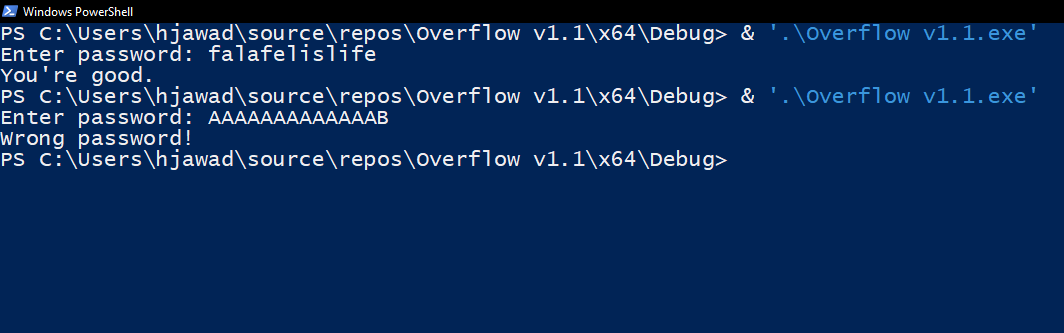
Patch Diffing With Ghidra Low Level Shenanigans We have learned how to use ghidra to reverse engineer a program and recreate the binary patch from part 5 for our case study. next time, we will study an esoteric but extremely powerful reverse engineering technique where we will slice an executable file back into relocatable object files. This repository contains reverse engineering notes and guides for educational purposes, using open source tools such as ghidra to pry into binaries for the nintendo switch. Ghidra 11.4, the latest open source reverse engineering (sre) framework from the nsa, introduces critical enhancements for malware analysis and vulnerability research. This is a workaround script that addresses some issues that ghidra has had in saving patched binaries. it saves the modifications that you made in ghidra back to the binary. In this post, we will delve into reverse engineering and patching the software using the new open source nsa tool ghidra, which rivals its expensive competitors such as ida pro in value and ease of use. With 12 years of experience in mobile app penetration testing, i’ve seen how tools like jadx, hopper, and ghidra can turn even heavily obfuscated apps into readable code. this expanded guide.
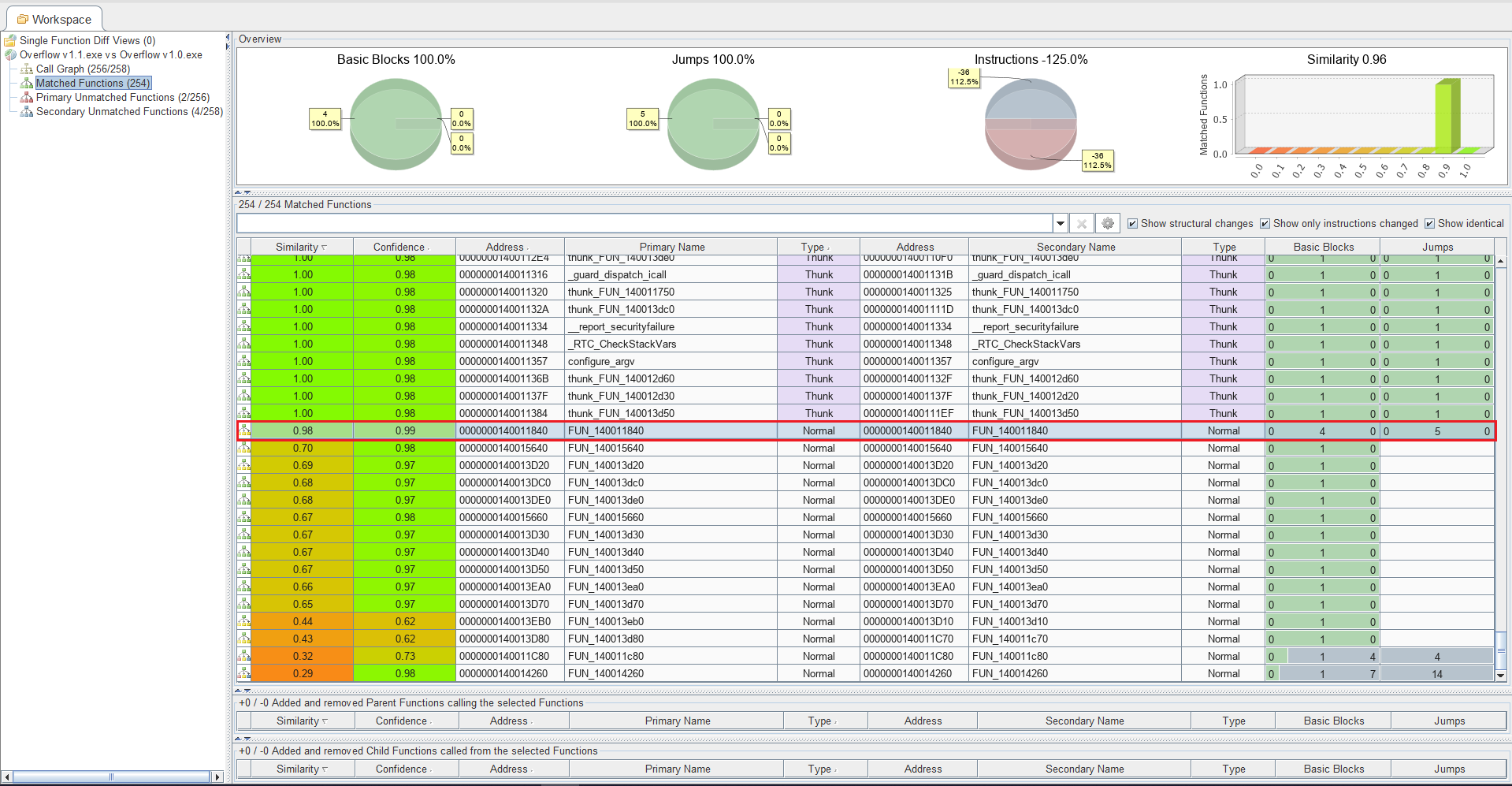
Patch Diffing With Ghidra Low Level Shenanigans Ghidra 11.4, the latest open source reverse engineering (sre) framework from the nsa, introduces critical enhancements for malware analysis and vulnerability research. This is a workaround script that addresses some issues that ghidra has had in saving patched binaries. it saves the modifications that you made in ghidra back to the binary. In this post, we will delve into reverse engineering and patching the software using the new open source nsa tool ghidra, which rivals its expensive competitors such as ida pro in value and ease of use. With 12 years of experience in mobile app penetration testing, i’ve seen how tools like jadx, hopper, and ghidra can turn even heavily obfuscated apps into readable code. this expanded guide.
Comments are closed.