How To Master External Attack Surface Management
A Practical Guide To Attack Surface Management Elasticito Microsoft defender external attack surface management (defender easm) continuously discovers and maps your digital attack surface to provide an external view of your online infrastructure. External attack surface management (easm) gives enterprises the external visibility to protect what attackers see first. this article explains how easm tools work, why they matter, and how firemon’s solutions help reduce digital risk.
External Attack Surface Management Attaxion Learn what attack surface management is and how asm helps find vulnerabilities. discover how to reduce your attack surface before attackers exploit exposed assets. Learn what external attack surface management (easm) is, why legacy tools don't work, and how security teams are addressing blind spots before attackers do. Configure microsoft defender external attack surface management (easm) to reduce your organization's external risks, learn how by following this blogpost. Learn what external attack surface management (easm) is, why it’s critical for modern security programs, and how to manage your organization’s external facing digital assets.

External Attack Surface Management Attaxion Configure microsoft defender external attack surface management (easm) to reduce your organization's external risks, learn how by following this blogpost. Learn what external attack surface management (easm) is, why it’s critical for modern security programs, and how to manage your organization’s external facing digital assets. External attack surface management (easm) is the continuous process of discovering, monitoring, and securing all internet facing assets that attackers could target. In this guide, we’ll explain how external facing vulnerabilities can get out of hand so quickly, how to rein in vulnerability creep, and how to manage your external attack surface going forward to reduce risk. Learn how to secure your external attack surface with proactive monitoring, deception technology, and real time threat intelligence. Over the next few thousand words, we’ll define easm, explore how it works, dig into how it reduces cyber risk, and walk through implementation best practices—all in a tone cisos, it leaders, and tech savvy readers can connect with.
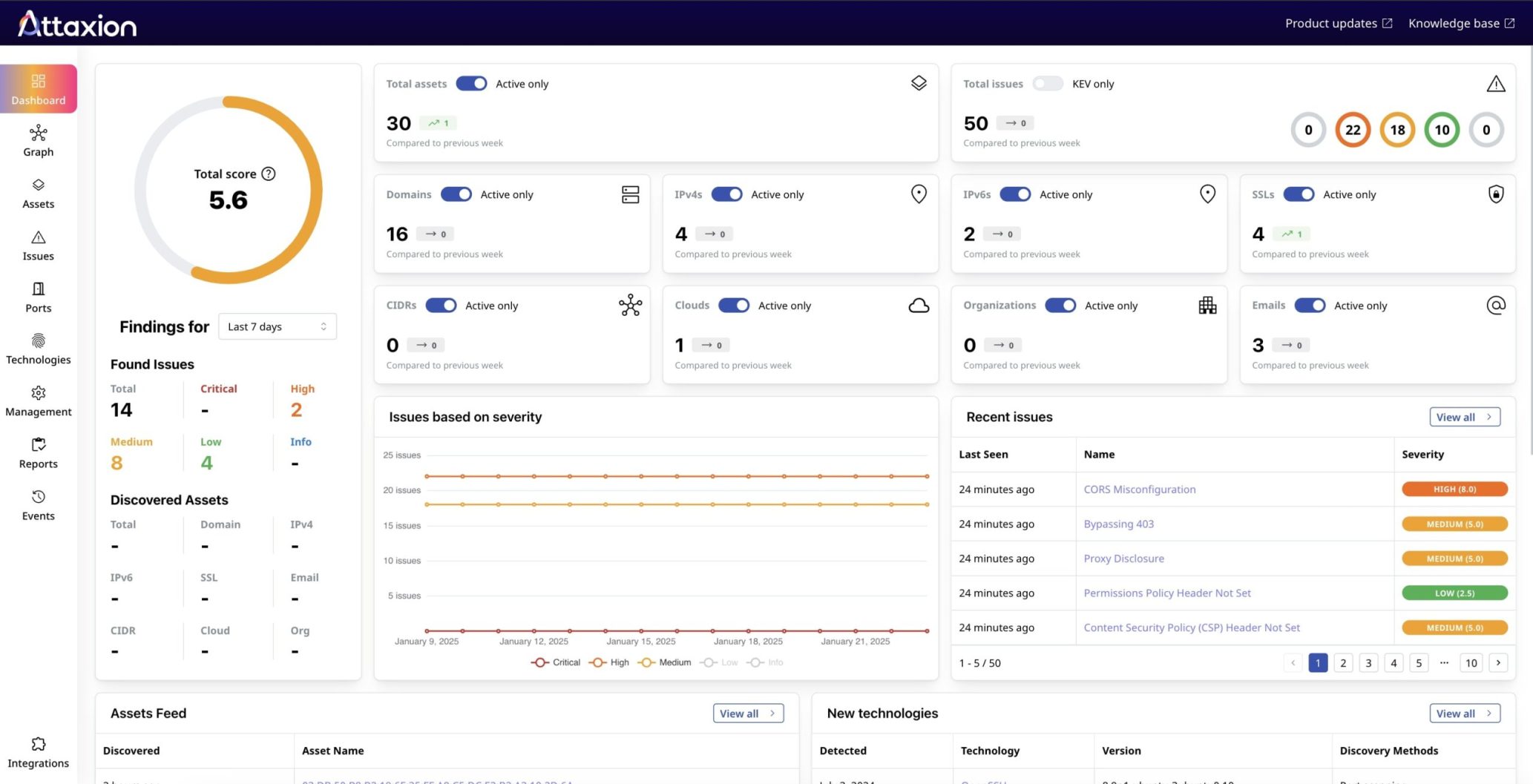
External Attack Surface Management Attaxion External attack surface management (easm) is the continuous process of discovering, monitoring, and securing all internet facing assets that attackers could target. In this guide, we’ll explain how external facing vulnerabilities can get out of hand so quickly, how to rein in vulnerability creep, and how to manage your external attack surface going forward to reduce risk. Learn how to secure your external attack surface with proactive monitoring, deception technology, and real time threat intelligence. Over the next few thousand words, we’ll define easm, explore how it works, dig into how it reduces cyber risk, and walk through implementation best practices—all in a tone cisos, it leaders, and tech savvy readers can connect with.

External Attack Surface Management Securityscorecard Learn how to secure your external attack surface with proactive monitoring, deception technology, and real time threat intelligence. Over the next few thousand words, we’ll define easm, explore how it works, dig into how it reduces cyber risk, and walk through implementation best practices—all in a tone cisos, it leaders, and tech savvy readers can connect with.

External Attack Surface Management Buyer S Guide Hadrian
Comments are closed.