How To Inspect Encrypted Traffic Without Draining Network Performance

How To Inspect Encrypted Traffic Without Draining Network Performance Learn how to inspect encrypted traffic without breaking privacy. discover metadata analysis, behavioral detection, and machine learning methods to secure networks while staying compliant and privacy friendly. With metadata based traffic inspection, behavioral analysis, and deep session inspection®, fidelis delivers holistic encrypted traffic visibility, monitoring, and analysis—all without decrypting a single byte of user data.
Encrypted Network Traffic Encrypted Network Traffic Analysis Fpyk Inspecting tls encrypted traffic is a balancing act between security and visibility. by choosing the right tools and following best practices, we can gain valuable insights into network behavior without compromising privacy. Many firewalls and other security tools do not understand encrypted traffic, and many organizations have chosen to pass encrypted traffic into their networks without security inspection just to keep communication flowing. Use a tls inspection proxy if you want to inspect the traffic with something other than wireshark. inspect potentially malicious tls traffic with an ids or security appliance. Learn the most effective ways to monitor and analyze encrypted traffic for emerging technologies, such as cloud, iot, and blockchain, without compromising security or performance.

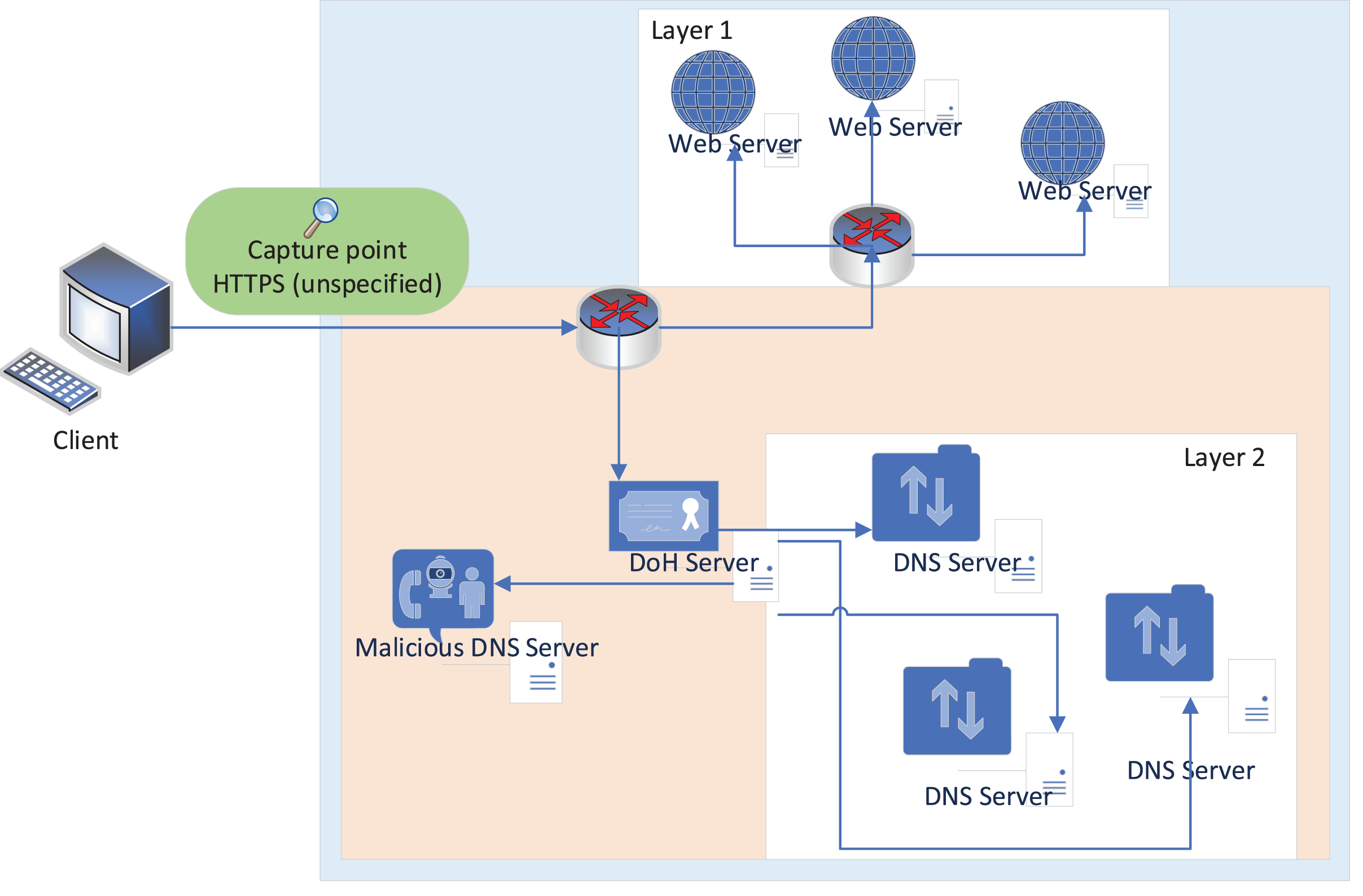
Inspect Encrypted Https Traffic Iboss Use a tls inspection proxy if you want to inspect the traffic with something other than wireshark. inspect potentially malicious tls traffic with an ids or security appliance. Learn the most effective ways to monitor and analyze encrypted traffic for emerging technologies, such as cloud, iot, and blockchain, without compromising security or performance. In response to the proliferation of diverse network traffic patterns from internet of things devices, websites, and mobile applications, understanding and classifying encrypted traffic are crucial for network administrators, cybersecurity professionals, and policy enforcement entities. Using these data elements or enhanced telemetry, encrypted traffic analytics can help detect malicious activity in encrypted traffic by applying advanced security analytics. The survey emphasizes the instrumental role of ml and dl in deciphering encrypted traffic nuances without undermining the core advantages of encryption, spotlighting the need for innovative solutions that reduce false positives and improve real time processing performance in encrypted networks. It enables network security devices to inspect the content of encrypted traffic to identify and block malicious activity. ssl inspection also helps organizations comply with regulatory requirements for data protection and privacy.
Comments are closed.