How To Implement Zero Trust Security

Zero Trust Security Step By Step Implementation Cogify Find deployment guides, assessment tools, and adoption frameworks to implement zero trust principles that protect and enable secure operations across identity, endpoints, applications, data, infrastructure, and networks in your organization. As attackers become more sophisticated, companies need more powerful security. learn how to implement zero trust to keep operations secure.

How To Implement A Zero Trust Security Model Our guide on how to implement zero trust security breaks down core principles, key components, and best practices for building a modern security framework. Learn how to implement zero trust security and the steps you need to take. understand why implementation involves a policy of never trusting and always verifying the authenticity and privileges of devices and users. Learn how to implement zero trust security with clear pillars, a practical roadmap, and tactics that solve challenges and cut risk across cloud environments. Learn the key principles, tips, and best practices for how to implement zero trust security in your organization while avoiding common challenges.
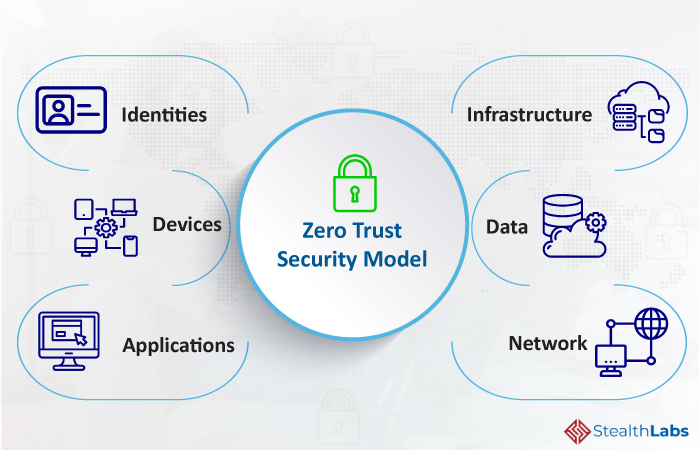
How Businesses Can Implement Zero Trust Security Learn how to implement zero trust security with clear pillars, a practical roadmap, and tactics that solve challenges and cut risk across cloud environments. Learn the key principles, tips, and best practices for how to implement zero trust security in your organization while avoiding common challenges. Master zero trust implementation with our step by step guide. from identity verification to network segmentation, build a stronger security posture today. Implementing a zero trust security model doesn't have to be intimidating. this guide covers each step of the process and tools to help maintain compliance. Get a comprehensive guide to key zero trust concepts, the most influential frameworks, top zero trust benefits, and best practices for selecting a zero trust vendor. With a clear understanding of the five pillars of zero trust and your organizational security goals in mind, you can start acting on your zero trust implementation plan. these 10 steps offer a roadmap for using zero trust principles effectively as the basis for your organization’s security posture.
Comments are closed.