How To Implement Blowfish
Blowfish Tutorial Blowfish Blowfish is an encryption technique designed by bruce schneier in 1993 as an alternative to the des encryption technique. it is significantly faster than des and provides a good encryption rate with no effective cryptanalysis technique found to date. Learn how to implement encryption and decryption using blowfish ciphers with the java cryptography architecture (jca).

Recipe Template Blowfish The code demonstrates how to use the java cryptography architecture to implement the blowfish algorithm for encryption and decryption. this example showcases the actual process described above in a concise and practical manner. Learn how to implement blowfish encryption in java using jca. step by step tutorial with code snippets and tips for beginners and advanced users. The document provides an in depth analysis of the blowfish algorithm, a symmetric block cipher designed as a fast and free alternative to existing encryption algorithms. In this article, we will learn what is the blowfish algorithm and how to encrypt and decrypt data using the blowfish algorithm in python. blowfish algorithm is an encryption method that was created as a replacement for the des algorithm.

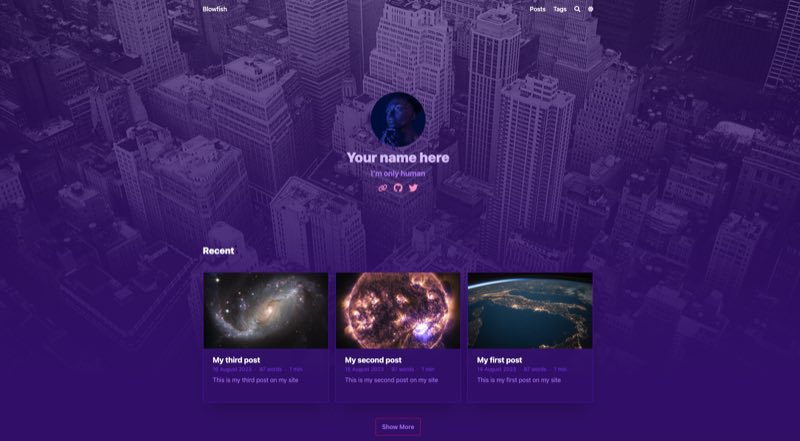
Build Your Homepage Using Blowfish And Hugo Blowfish The document provides an in depth analysis of the blowfish algorithm, a symmetric block cipher designed as a fast and free alternative to existing encryption algorithms. In this article, we will learn what is the blowfish algorithm and how to encrypt and decrypt data using the blowfish algorithm in python. blowfish algorithm is an encryption method that was created as a replacement for the des algorithm. This blowfish encryption method uses your private key to protect your data. the best thing about blowfish is that, if the material is encrypted, it can be challenging to decrypt it without the original key. This guide demonstrates how to implement blowfish encryption and decryption using java, covering key lengths from 32 to 448 bits. you'll learn to properly initialize the cipher, manage keys, and process data streams securely. Implementations of blowfish that require the fastest speeds should unroll the loop and ensure that all sub keys are stored in cache. the sub keys are calculated using the blowfish algorithm. Explore blowfish encryption's java jca implementation, providing robust security and flexibility. learn how to use it effectively.
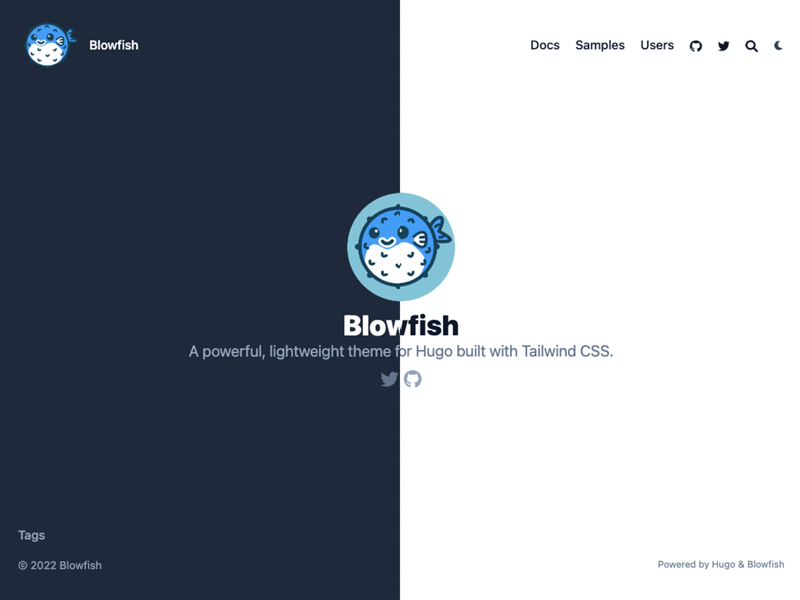
Homepage Layout Blowfish This blowfish encryption method uses your private key to protect your data. the best thing about blowfish is that, if the material is encrypted, it can be challenging to decrypt it without the original key. This guide demonstrates how to implement blowfish encryption and decryption using java, covering key lengths from 32 to 448 bits. you'll learn to properly initialize the cipher, manage keys, and process data streams securely. Implementations of blowfish that require the fastest speeds should unroll the loop and ensure that all sub keys are stored in cache. the sub keys are calculated using the blowfish algorithm. Explore blowfish encryption's java jca implementation, providing robust security and flexibility. learn how to use it effectively.
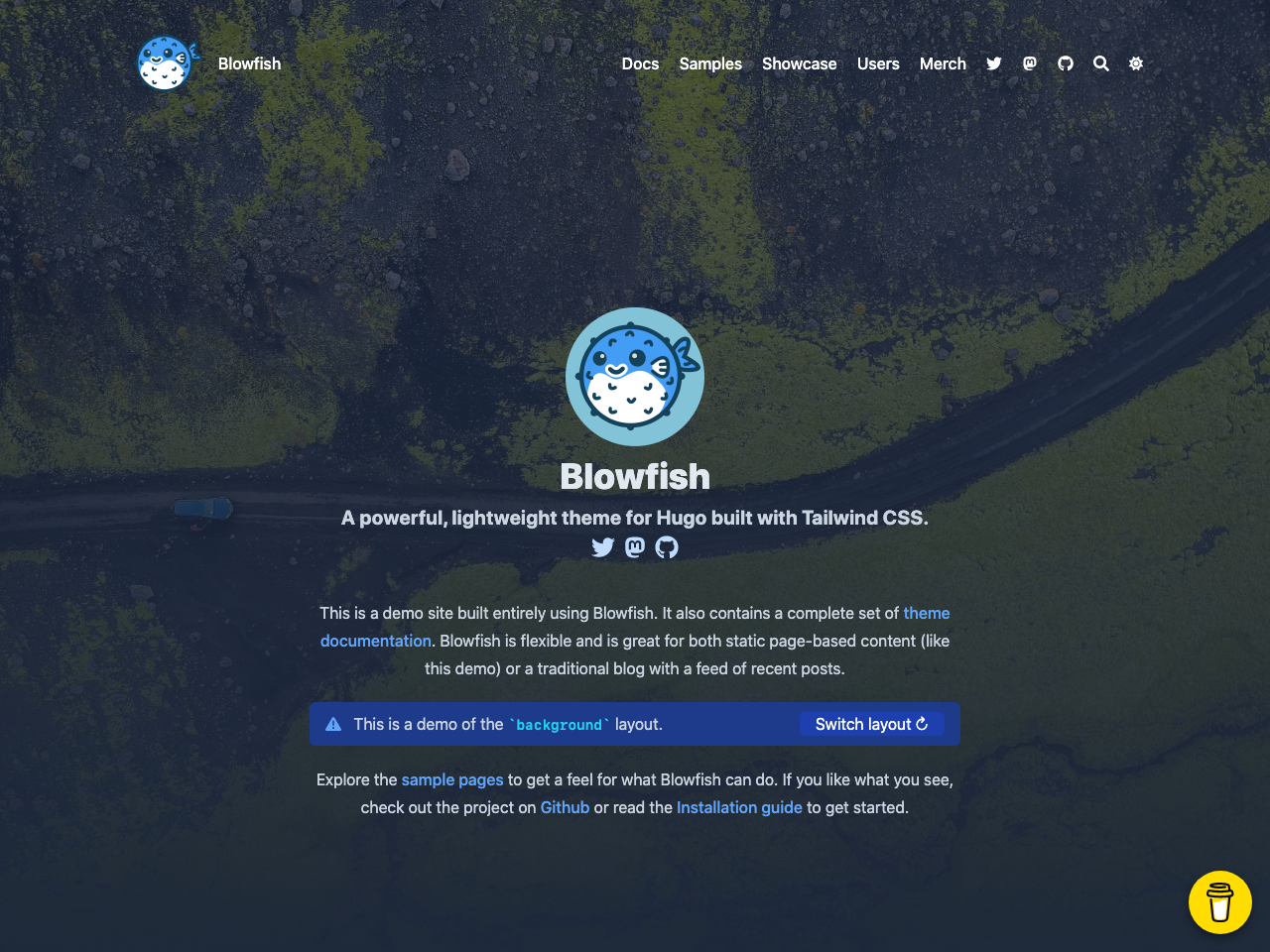
Blowfish Jamstack Themes Implementations of blowfish that require the fastest speeds should unroll the loop and ensure that all sub keys are stored in cache. the sub keys are calculated using the blowfish algorithm. Explore blowfish encryption's java jca implementation, providing robust security and flexibility. learn how to use it effectively.

Premium Ai Image Blowfish
Comments are closed.