How To Implement A Devsecops Pipeline With Zero Trust Evan Gertis Conf42 Devsecops 2022

Conf42 How To Implement A Devsecops Pipeline With Zero Trust How to implement a devsecops pipeline with zero trust video size: abstract the purpose of this talk is to discuss how to implement a full scale developer security operations into a devops pipeline secured with a zero trust network. How to implement a devsecops pipeline with zero trust the purpose of this talk is to discuss how to implement a full scale developer security operations into a devops pipeline secured with a zero trust network.
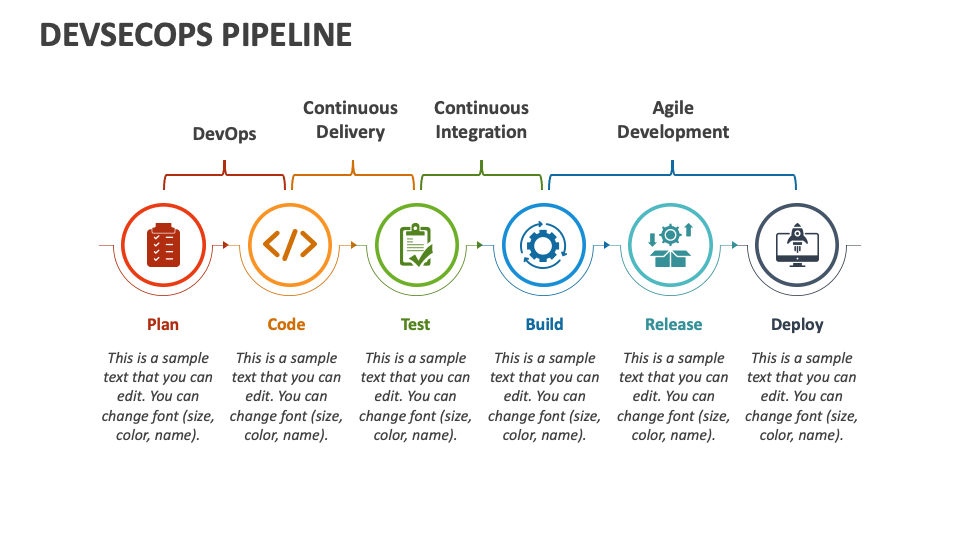
Devsecops Pipeline Powerpoint And Google Slides Template Ppt Slides This article describes best practices for securing your devops environments with a zero trust approach for preventing bad actors from compromising developer boxes, infecting release pipelines with malicious scripts, and gaining access to production data via test environments. Learn how centralized log management is crucial in devsecops during this instructive session from a technical engineer. Building a secure ci cd pipeline is no longer optional—it is a fundamental requirement for modern software development. in this guide, we will walk through implementing a zero trust devsecops pipeline that integrates security at every stage of the development lifecycle. In this blog, we will explore how to implement zero trust principles in ci cd pipelines within devsecops environments, including practical steps for integrating authentication,.
Github Ghanatava Devsecops Pipeline A Devsecops Pipeline Using Jenkins Building a secure ci cd pipeline is no longer optional—it is a fundamental requirement for modern software development. in this guide, we will walk through implementing a zero trust devsecops pipeline that integrates security at every stage of the development lifecycle. In this blog, we will explore how to implement zero trust principles in ci cd pipelines within devsecops environments, including practical steps for integrating authentication,. The owasp devsecops guideline project explains how to best implement a secure pipeline, using best practices and introducing automation tools to help 'shift left' security issues. This tutorial walks through a practical, real world approach to implementing zero trust principles in devsecops pipelines using: by applying these principles, you can build a ci cd. Learn how to implement zero trust in devsecops, enforcing authentication, authorisation, and monitoring across all pipeline layers. An effective enterprise devsecops implementation framework incorporates zero trust principles to ensure secure access across complex infrastructures. this integration creates a tight alignment between continuous security in the ci cd pipeline and continuous verification for system access.

Pipeline Security Devsecops Pipeline E Spin Group The owasp devsecops guideline project explains how to best implement a secure pipeline, using best practices and introducing automation tools to help 'shift left' security issues. This tutorial walks through a practical, real world approach to implementing zero trust principles in devsecops pipelines using: by applying these principles, you can build a ci cd. Learn how to implement zero trust in devsecops, enforcing authentication, authorisation, and monitoring across all pipeline layers. An effective enterprise devsecops implementation framework incorporates zero trust principles to ensure secure access across complex infrastructures. this integration creates a tight alignment between continuous security in the ci cd pipeline and continuous verification for system access.
Comments are closed.