How To Hunt And Investigate Linux Malware Any Run S Cybersecurity Blog
How To Hunt And Investigate Linux Malware Any Run S Cybersecurity Blog Learn to hunt for linux malware with any.run's threat intelligence lookup and see how you can use it together with the interactive sandbox. Ti lookup allows you to search across threat data extracted from the latest malware and phishing samples analyzed by over 500,000 professionals and 15,000 companies around the globe in any.run’s interactive sandbox. it is one of the best tools for researching attacks and incidents.
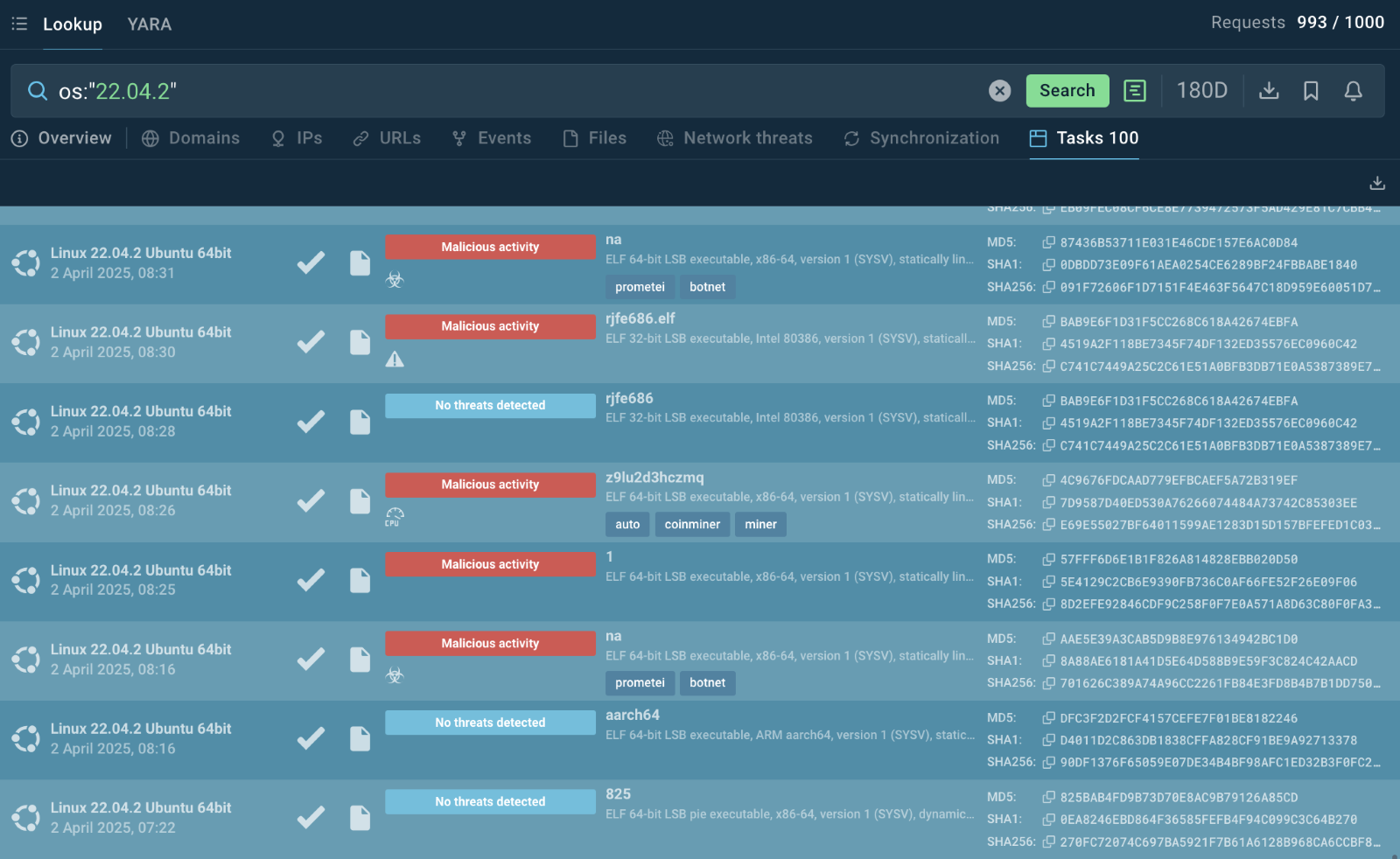
How To Hunt And Investigate Linux Malware Any Run S Cybersecurity Blog It lets you search across threat data extracted from the latest malware and phishing samples analyzed by over 500,000 professionals and 15,000 companies around the globe in any.run’s interactive sandbox. The interactive sandbox simplifies malware analysis of threats that target both windows and linux systems. the threat intelligence products, ti lookup, yara search, and feeds, help you find iocs or files to learn more about the threats and respond to incidents faster. Let’s see how cybersecurity teams use any.run to detect and analyze malware written in languages like python and node.js, and built to target different systems. Ti lookup allows you to search across threat data extracted from the latest malware and phishing samples analyzed by over 500,000 professionals and 15,000 companies around the globe in any.run’s interactive sandbox. it is one of the best tools for researching attacks and incidents.
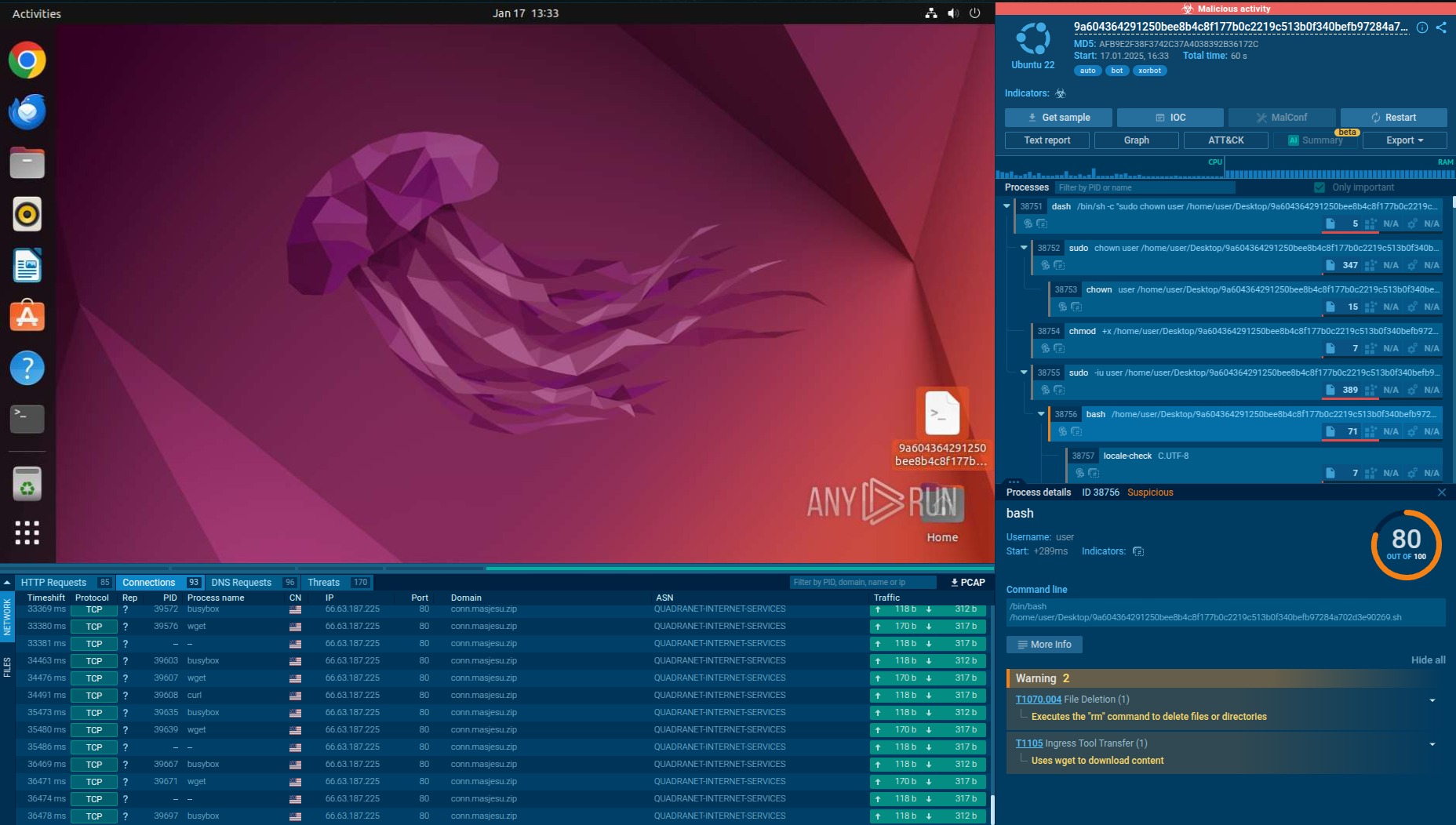
How To Hunt And Investigate Linux Malware Any Run S Cybersecurity Blog Let’s see how cybersecurity teams use any.run to detect and analyze malware written in languages like python and node.js, and built to target different systems. Ti lookup allows you to search across threat data extracted from the latest malware and phishing samples analyzed by over 500,000 professionals and 15,000 companies around the globe in any.run’s interactive sandbox. it is one of the best tools for researching attacks and incidents. This article explores the importance of linux malware analysis and presents detailed case studies using any.run's advanced malware analysis. Step by step guide to detect and analyze linux malware and attacks: botnets, miners, and more. includes commands, verification, and troubleshooting. Any.run provides full visibility and real time malware analysis, enabling security teams to respond to threats efficiently. this article explores key commands, techniques, and best practices to leverage any.run and strengthen your cybersecurity posture. See how you can strengthen your security posture by analyzing linux malware, such as mirai, and understanding its behavior.

How To Hunt And Investigate Linux Malware Any Run S Cybersecurity Blog This article explores the importance of linux malware analysis and presents detailed case studies using any.run's advanced malware analysis. Step by step guide to detect and analyze linux malware and attacks: botnets, miners, and more. includes commands, verification, and troubleshooting. Any.run provides full visibility and real time malware analysis, enabling security teams to respond to threats efficiently. this article explores key commands, techniques, and best practices to leverage any.run and strengthen your cybersecurity posture. See how you can strengthen your security posture by analyzing linux malware, such as mirai, and understanding its behavior.
Comments are closed.