How To Hack A Web Server
How To Hack A Server Web Server Types And Vulnerabilities This documentation provides a comprehensive breakdown of common hacking techniques used to gain unauthorized access to a server and offers insight into preventive measures to secure servers against such attacks. This article has provided a comprehensive overview of web server hacking, from common attack techniques to the tools and steps involved in ethical hacking. by applying these principles, you can enhance the security of your web servers and ensure a robust defense against cyber threats.
How To Hack A Web Server Many web servers on the internet are unix based, so understanding unix commands is crucial if you want to try hacking web servers. Hacking isn’t limited to the genius criminals in the movies. read on to learn how to hack a website with this guide!. This blog post takes you through a step by step journey of how a hacker might infiltrate a web server, starting from gaining initial access (a "foothold") to achieving full control (known as "root" access). There are a lot of different ways you can hack a web server, but the easiest way is to use something called an sql injection, which involves executing operating system commands on the web server.

How To Hack A Web Server This blog post takes you through a step by step journey of how a hacker might infiltrate a web server, starting from gaining initial access (a "foothold") to achieving full control (known as "root" access). There are a lot of different ways you can hack a web server, but the easiest way is to use something called an sql injection, which involves executing operating system commands on the web server. In this video, i show you how to hack your own vulnerable server using kali linux and metasploitable 2. this penetration testing demo is 100% safe, legal, and perfect for beginners who want. In this article, we will walk through the process of using metasploit to exploit a web server, highlighting key steps such as reconnaissance, vulnerability identification, selecting an exploit, configuring the payload, and post exploitation actions. What is web server hacking? how many types of attacks are there? complete guide to web server hacking. read now. Uncover vulnerabilities with ethical hacking! learn to gain control of web servers, test for weaknesses, and improve security with our guide.

How Do Hackers Get Into Computers Through Websites Padsjza In this video, i show you how to hack your own vulnerable server using kali linux and metasploitable 2. this penetration testing demo is 100% safe, legal, and perfect for beginners who want. In this article, we will walk through the process of using metasploit to exploit a web server, highlighting key steps such as reconnaissance, vulnerability identification, selecting an exploit, configuring the payload, and post exploitation actions. What is web server hacking? how many types of attacks are there? complete guide to web server hacking. read now. Uncover vulnerabilities with ethical hacking! learn to gain control of web servers, test for weaknesses, and improve security with our guide.
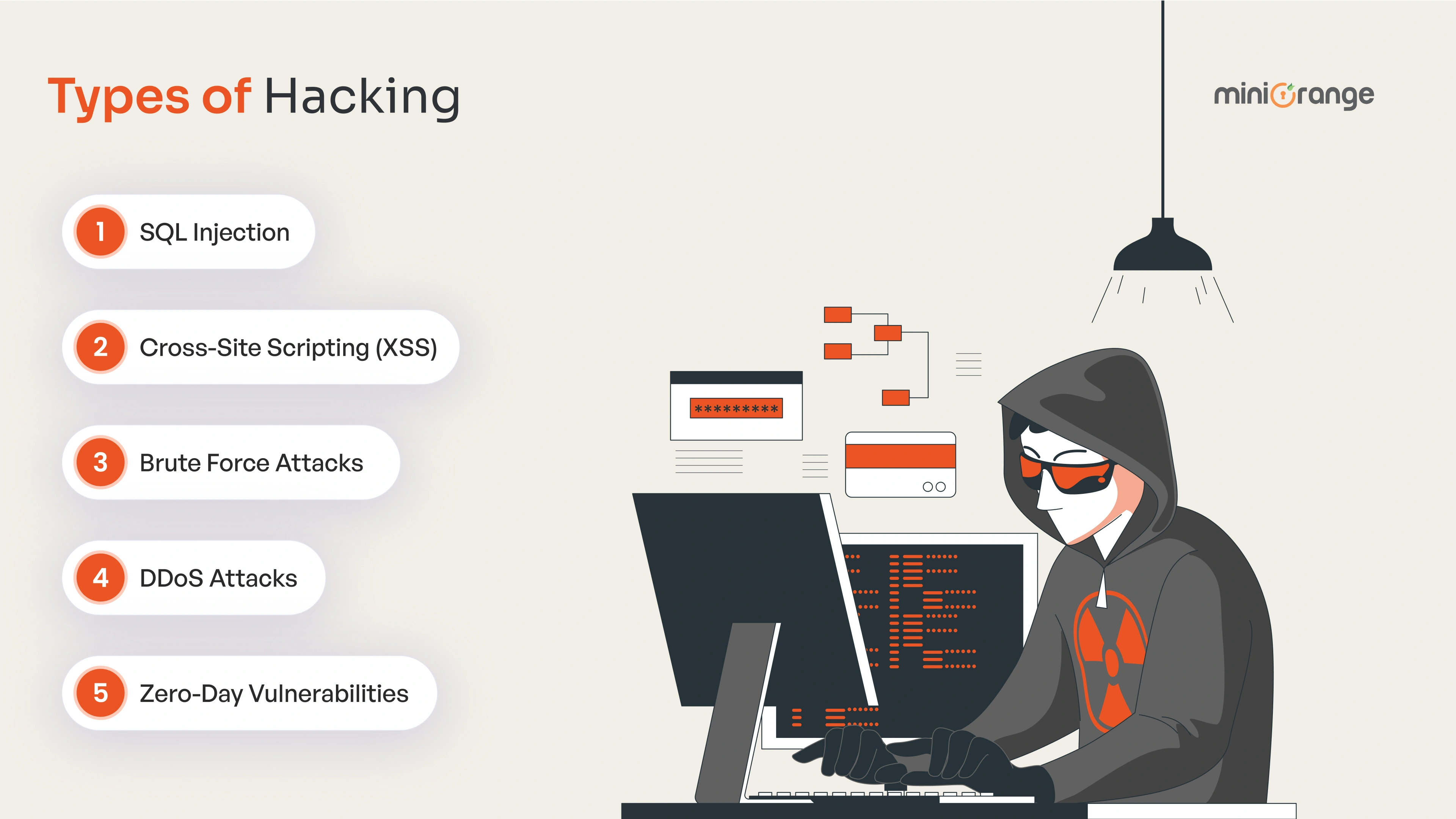
16 Expert Security Tips To Protect Your Website From Hackers What is web server hacking? how many types of attacks are there? complete guide to web server hacking. read now. Uncover vulnerabilities with ethical hacking! learn to gain control of web servers, test for weaknesses, and improve security with our guide.
Comments are closed.