How To Get Json Of Permissions Aws Iam Stackoverflow Aws Iam Training Iam Policies Tutorial

Refine Permissions For Externally Accessible Roles Using Iam Access This section presents detailed syntax, descriptions, and examples of the elements, variables, and evaluation logic of json policies in iam. for more general information, see overview of json policies. Iam permissions are available on all service pages. each iam permission details its own description, access level, resolved resource type arn pattern, condition keys, as well as the api methods that are known to consume that permission.

Now Create And Manage Aws Iam Roles More Easily With The Updated Iam Understanding iam policies and utilizing json for policy management are essential skills for developers working with aws. overall, managing iam policies using json offers developers a flexible and powerful way to define and control permissions in aws. A cli tool to manage aws iam roles and the policies is useful to operate their definitions as json files. supports exporting roles policies your aws account has already registered, importing new roles policies, and validating whether them on aws to equal the definitions at local. By mastering iam policies, you can protect your aws environment, enable your teams to work faster, and avoid the nightmare of over permissioned accounts. I'm looking for a simple way to export all iam users, roles and policies from an aws organization account. this should include iam resources from member accounts in the export.

Move Over Json Policy Summaries Make Understanding Iam Policies By mastering iam policies, you can protect your aws environment, enable your teams to work faster, and avoid the nightmare of over permissioned accounts. I'm looking for a simple way to export all iam users, roles and policies from an aws organization account. this should include iam resources from member accounts in the export. In this article, we will walk through the process of using the aws policy generator to create a json document that grants an iam user the permissions to create other iam users and add them to. Use this operation to obtain a snapshot of the configuration of iam permissions (users, groups, roles, and policies) in your account. policies returned by this operation are url encoded compliant with rfc 3986 . you can use a url decoding method to convert the policy back to plain json text. Granular control using policies: iam policies are json based documents that allow you to control access at a granular level. you can apply these policies to users, groups, or roles to define what actions they can take on specific aws resources. By setting up iam roles and policies, integrating aws sdk in your backend, and enforcing role based access in both the frontend and backend, you can create a secure and scalable web application.

Move Over Json Policy Summaries Make Understanding Iam Policies In this article, we will walk through the process of using the aws policy generator to create a json document that grants an iam user the permissions to create other iam users and add them to. Use this operation to obtain a snapshot of the configuration of iam permissions (users, groups, roles, and policies) in your account. policies returned by this operation are url encoded compliant with rfc 3986 . you can use a url decoding method to convert the policy back to plain json text. Granular control using policies: iam policies are json based documents that allow you to control access at a granular level. you can apply these policies to users, groups, or roles to define what actions they can take on specific aws resources. By setting up iam roles and policies, integrating aws sdk in your backend, and enforcing role based access in both the frontend and backend, you can create a secure and scalable web application.
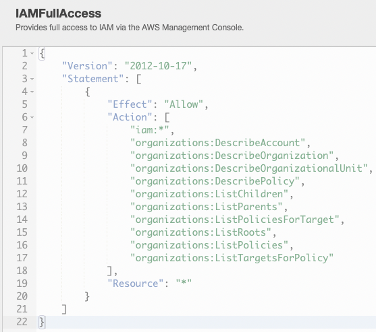
Using Permission Boundaries To Delegate Permissions In Aws Iam Ivision Granular control using policies: iam policies are json based documents that allow you to control access at a granular level. you can apply these policies to users, groups, or roles to define what actions they can take on specific aws resources. By setting up iam roles and policies, integrating aws sdk in your backend, and enforcing role based access in both the frontend and backend, you can create a secure and scalable web application.
Comments are closed.