How To Encrypt Files On Linux With Ccrypt
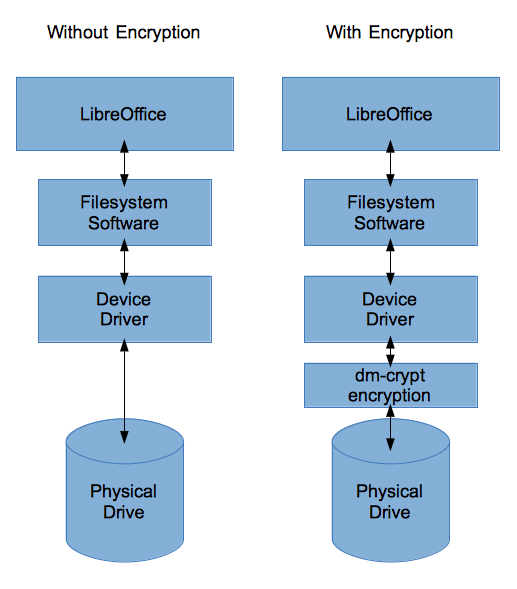
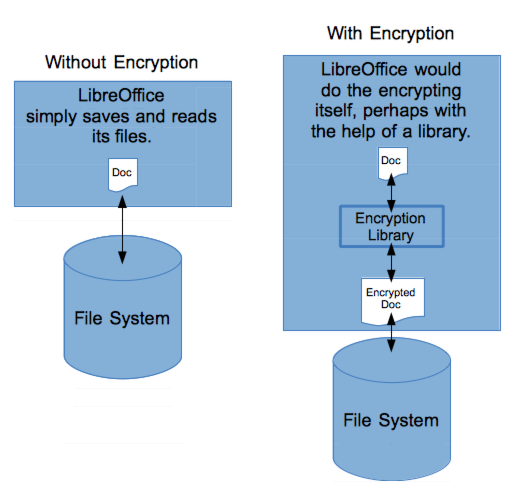
How To Encrypt A Linux File System With Dm Crypt Linux With options we can encrypt decrypt the files and directories for our own means, and features such as automatic deletion, of unencrypted originals, ccrypt is versatile enough for various usage environments. It hooks into the low level file i o functions (including write region and insert file contents) so that they automatically encrypt or decrypt a file if the file appears to need it (based on the extension of the file name).

Encrypt Files And Directories On Linux Using Veracrypt Computingforgeeks Encrypt by typing this in a terminal window: ccrypt file name. replace “ file name ” with the name of your file. you will be asked to submit a password two times. the encrypted file will have the .cpt extension. now you can send the file via email or store on a usb thumb drive and it will be secure. Learn how to encrypt and decrypt files in linux using ccrypt. easy to follow guide with practical examples for securing your sensitive information. The ccrypt utility is a security tool that encrypts and decrypts files and streams on demand. it uses the advanced encryption standard (aes), which is considered very secure. Ccrypt encrypts and decrypts files and streams using the rijndael cipher (aes) with 256 bit keys. it replaces the original file with an encrypted version bearing a `.cpt` extension, and the original is securely overwritten rather than simply deleted.
How To Encrypt A Linux File System With Dm Crypt Linux The ccrypt utility is a security tool that encrypts and decrypts files and streams on demand. it uses the advanced encryption standard (aes), which is considered very secure. Ccrypt encrypts and decrypts files and streams using the rijndael cipher (aes) with 256 bit keys. it replaces the original file with an encrypted version bearing a `.cpt` extension, and the original is securely overwritten rather than simply deleted. The algorithm provided by ccrypt is not symmetric, i.e., one must specify whether to encrypt or decrypt. the most common way to invoke ccrypt is via the commands ccencrypt and ccdecrypt. The most common way to invoke ccrypt is via the commands ccencrypt and ccdecrypt. there is also a ccat command for decrypting a file directly to the terminal, thus reducing the likelihood of leaving temporary plaintext files around. Unlike unix crypt, the algorithm provided by ccrypt is not symmetric, i.e., one must specify whether to encrypt or decrypt. the most common way to invoke ccrypt is via the commands ccencrypt and ccdecrypt. encryption and decryption depends on a keyword (or key phrase) supplied by the user. This option causes ccrypt to use temporary files during encryption decryption, rather than overwriting the file contents destructively. this method leaves the original file contents lying around in unused sectors of the file system, and thus is less secure than the default behavior.

Cryptr A Simple Cli Utility To Encrypt And Decrypt Files Everything The algorithm provided by ccrypt is not symmetric, i.e., one must specify whether to encrypt or decrypt. the most common way to invoke ccrypt is via the commands ccencrypt and ccdecrypt. The most common way to invoke ccrypt is via the commands ccencrypt and ccdecrypt. there is also a ccat command for decrypting a file directly to the terminal, thus reducing the likelihood of leaving temporary plaintext files around. Unlike unix crypt, the algorithm provided by ccrypt is not symmetric, i.e., one must specify whether to encrypt or decrypt. the most common way to invoke ccrypt is via the commands ccencrypt and ccdecrypt. encryption and decryption depends on a keyword (or key phrase) supplied by the user. This option causes ccrypt to use temporary files during encryption decryption, rather than overwriting the file contents destructively. this method leaves the original file contents lying around in unused sectors of the file system, and thus is less secure than the default behavior.
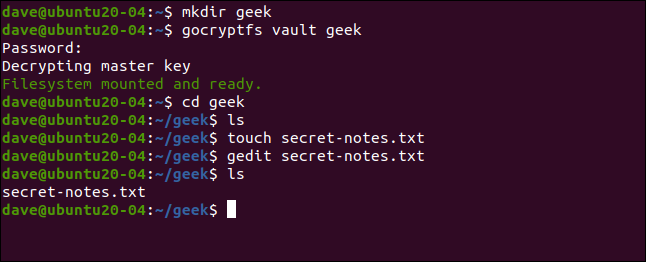
How To Encrypt Files With Gocryptfs On Linux Unlike unix crypt, the algorithm provided by ccrypt is not symmetric, i.e., one must specify whether to encrypt or decrypt. the most common way to invoke ccrypt is via the commands ccencrypt and ccdecrypt. encryption and decryption depends on a keyword (or key phrase) supplied by the user. This option causes ccrypt to use temporary files during encryption decryption, rather than overwriting the file contents destructively. this method leaves the original file contents lying around in unused sectors of the file system, and thus is less secure than the default behavior.
Comments are closed.