How To Do Two Factor Authentication Like A Pro

Master Two Factor Authentication Secure Your App Today Step by step guide to setting up two factor authentication (2fa) with authenticator apps, hardware keys, and backup codes for maximum security. Passwords are no longer enough. our complete guide explains what 2fa is, how it works, and why it's essential for modern security and compliance (soc 2, iso 27001, gdpr, pdpa).
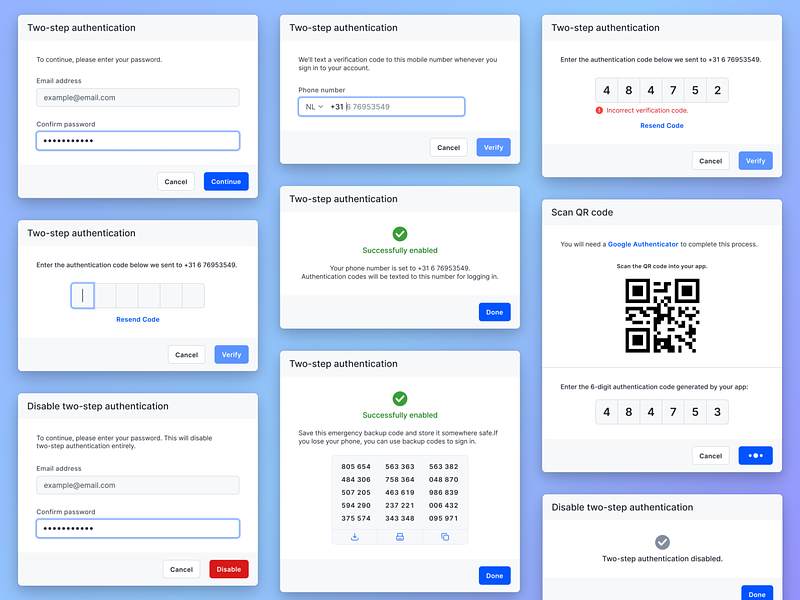
Two Factor Authentication Designs Themes Templates And Downloadable Complete guide to two factor and multi factor authentication, including recommended tools like duo and yubikey for account protection. Here’s the 101: 2fa adds an extra layer of security to your online accounts. when activated, this protocol will ask you for something other than your username and password whenever you log in. By adding a second factor—such as a time‑based one‑time password (totp), hardware token or passkey—you drastically reduce the risk of credential stuffing, phishing, session hijacking and other common threats. Learn about two factor authentication, different 2fa methods, and how to secure your accounts with multi factor authentication.

How To Do Two Factor Authentication Like A Pro Popular Science By adding a second factor—such as a time‑based one‑time password (totp), hardware token or passkey—you drastically reduce the risk of credential stuffing, phishing, session hijacking and other common threats. Learn about two factor authentication, different 2fa methods, and how to secure your accounts with multi factor authentication. Two factor authentication (2fa) adds a second layer of login security. discover the best methods and how to enable them. why do we need two factor authentication (2fa)? weak and or stolen passwords are one of the biggest cybersecurity risks. One of the most effective ways to fortify your online defenses is by implementing two factor authentication (2fa), and in this comprehensive guide, we'll walk you through the process, step by step of how to setup 2fa and recovery your (2fa) authenticator setting is loose or misplace your device. Google’s 2 step authentication is one of the most widely used systems, and mastering it can significantly enhance your digital safety. in this article, we will explore how to effectively use google 2 step authentication like a pro. Two factor authentication comes in several flavors, each with its strengths and weaknesses. the most familiar form is sms based 2fa, where a one time code is sent to your phone.

Successfully Introduce Two Factor Authentication To Your Team Two factor authentication (2fa) adds a second layer of login security. discover the best methods and how to enable them. why do we need two factor authentication (2fa)? weak and or stolen passwords are one of the biggest cybersecurity risks. One of the most effective ways to fortify your online defenses is by implementing two factor authentication (2fa), and in this comprehensive guide, we'll walk you through the process, step by step of how to setup 2fa and recovery your (2fa) authenticator setting is loose or misplace your device. Google’s 2 step authentication is one of the most widely used systems, and mastering it can significantly enhance your digital safety. in this article, we will explore how to effectively use google 2 step authentication like a pro. Two factor authentication comes in several flavors, each with its strengths and weaknesses. the most familiar form is sms based 2fa, where a one time code is sent to your phone.
Two Factor Authentication For Beginners Sapher Google’s 2 step authentication is one of the most widely used systems, and mastering it can significantly enhance your digital safety. in this article, we will explore how to effectively use google 2 step authentication like a pro. Two factor authentication comes in several flavors, each with its strengths and weaknesses. the most familiar form is sms based 2fa, where a one time code is sent to your phone.

How To Successfully Introduce Two Factor Authentication To Your Team
Comments are closed.