How To Bypass Rootbeer S Root Detection Seciron
How To Bypass Rootbeer S Root Detection Seciron However, there is no obfuscation of the code or other protections which means many anti root solutions can be easily bypassed. this article demonstrates how to bypass rootbeer’s anti root mechanism. In my previous post, i made a comparison between the different well known and open source root detection bypass tools for android. in that post, i encouraged analysts to learn how to.
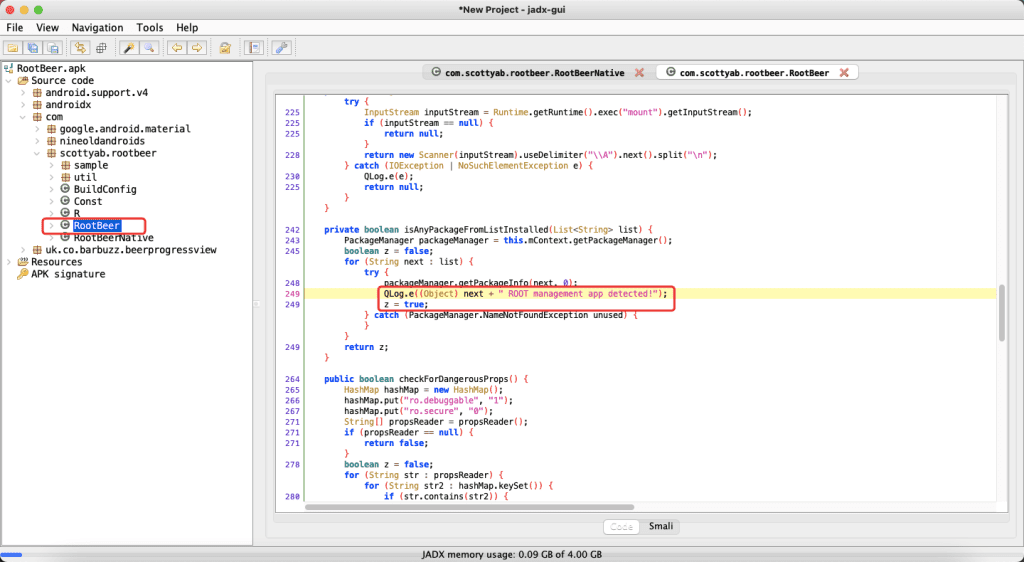
How To Bypass Rootbeer S Root Detection Seciron In this article, i will demonstrate how to bypass the rootbeer library. for this demonstration, i will use a sample rootbeer application. Project: rootbeer root detection bypass try this code out now by running $ frida codeshare ub3rsick ${projectslug} f your binary fingerprint: 2a67af38a0e050692ce6e616d7c315e7f4967f60b6513be6e177e7872bd47bf6 $ {errormsg}. This repository contains a powerful frida script designed to bypass root detection mechanisms in android applications. by intercepting both native and java based checks, this script effectively hides the presence of root, enabling smooth testing and debugging on rooted devices. We need rooted devices to test or analyze android apps more efficiently. however, applications with root detection mechanism prevent them from opening on rooted devices. in this article, we will learn how to bypass the root detection mechanism over two different techniques.
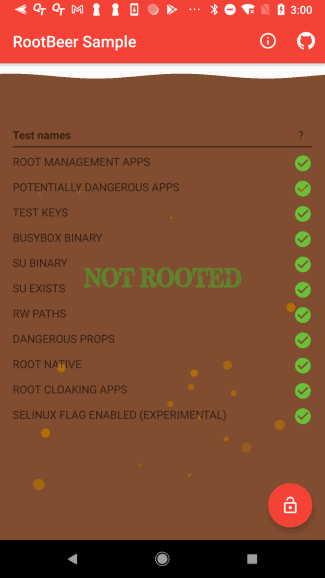
How To Bypass Rootbeer S Root Detection Seciron This repository contains a powerful frida script designed to bypass root detection mechanisms in android applications. by intercepting both native and java based checks, this script effectively hides the presence of root, enabling smooth testing and debugging on rooted devices. We need rooted devices to test or analyze android apps more efficiently. however, applications with root detection mechanism prevent them from opening on rooted devices. in this article, we will learn how to bypass the root detection mechanism over two different techniques. This module bypasses root checks the pro way. this module not only hooks java logic, but also hooks native system calls logic (logic written in c c native java code). In this part we are going to be looking to bypass the rootbeer sample application. for those of you that haven’t come across rootbeer before it is an open source root detection library. This works because appcloner can bypass emulation detection by modifying the internal structure of the cloned app rather than the device itself. this feature customize key aspects of the app, such as package name, signature, and permissions, which can deceive standard emulation checks. In this post, i’ll discuss how to change an application’s process during runtime through dynamic instrumentation using frida. the goal of this post is the same, and that is to bypass all the root detection checks used by rootbeer library.

How To Bypass Rootbeer S Root Detection Seciron This module bypasses root checks the pro way. this module not only hooks java logic, but also hooks native system calls logic (logic written in c c native java code). In this part we are going to be looking to bypass the rootbeer sample application. for those of you that haven’t come across rootbeer before it is an open source root detection library. This works because appcloner can bypass emulation detection by modifying the internal structure of the cloned app rather than the device itself. this feature customize key aspects of the app, such as package name, signature, and permissions, which can deceive standard emulation checks. In this post, i’ll discuss how to change an application’s process during runtime through dynamic instrumentation using frida. the goal of this post is the same, and that is to bypass all the root detection checks used by rootbeer library.
Comments are closed.