How To Avoid Sim Swapping Leaflet Enisa
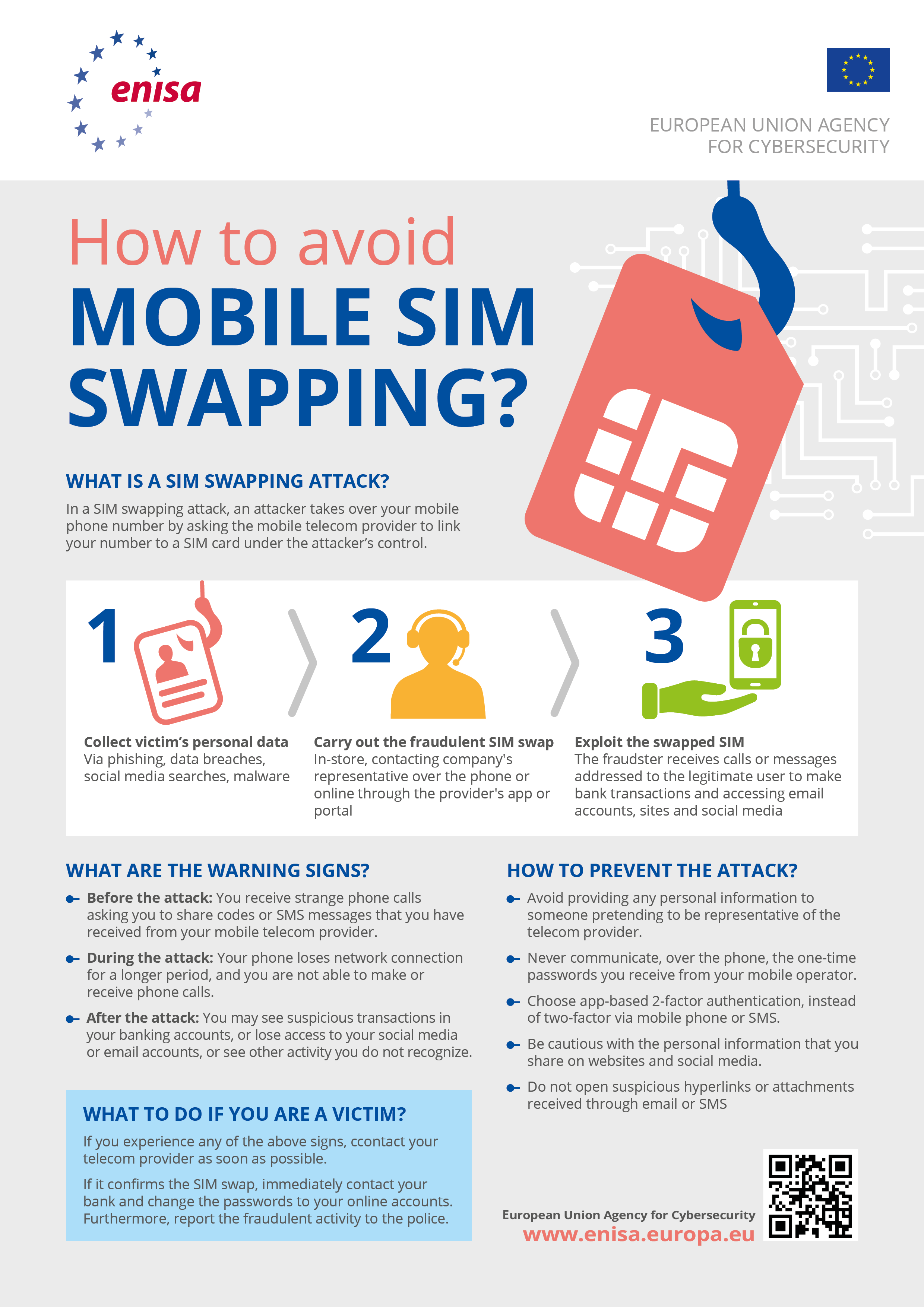
How To Avoid Sim Swapping Leaflet Enisa This leaflet, addresses the sim swapping attacks, how to recognise them and how to mitigate the risk connected to this fraud. in fact, subscriber identity module (sim) swapping is a legitimate procedure performed by a customer to change their sim card when it is lost or damaged. Try not to use your phone for personal matters to minimize exposure to sim swapping threats, or maybe use the second sim card number for non critical operations.
Countering Sim Swapping Enisa This guide outlines how to perform a sim swap when you have physical access to a device. these steps can be helpful in cases such as assisting users in regaining access to their own phone number or in troubleshooting sim related issues with carrier support. Learn about sim swap fraud, where scammers hijack phone numbers to gain control of personal accounts. discover tactics used, warning signs, and tips to protect yourself. How to prevent sim swap fraud? fortunately, there exist effective measures that both you and your service providers can take to prevent falling victim to sim swap fraud. Sim swapping is rarely a 'phone problem' in isolation. treat it as a control plane compromise and rebuild trust from the accounts that can reset everything else.

Beware Of The Sim Swapping Fraud Enisa How to prevent sim swap fraud? fortunately, there exist effective measures that both you and your service providers can take to prevent falling victim to sim swap fraud. Sim swapping is rarely a 'phone problem' in isolation. treat it as a control plane compromise and rebuild trust from the accounts that can reset everything else. 𝗛𝗼𝘄 𝘁𝗼 𝗔𝘃𝗼𝗶𝗱 𝗦𝗜𝗠 𝗦𝘄𝗮𝗽𝗽𝗶𝗻𝗴 𝗟𝗲𝗮𝗳𝗹𝗲𝘁 this leaflet, addresses the sim swapping attacks, how to recognise them and. To avoid succumbing to a sim jacking, it is crucial that phone users take steps to protect their devices. from implementing security measures with their phone company and limiting how many personal accounts are associated with their number, each can prove useful to prevent a sim swapping attack. In this study, we give an overview of how sim swapping attacks work, list measures that providers can take to mitigate the attack and make recommendations for policy makers and authorities in the telecom sector and other sectors. In a sim swapping attack, an attacker takes over your mobile phone number by asking the mobile telecom provider to link your number to a sim card under the attacker’s control.

Sim Swapping What You Should Know Why You Should Care Packt Secpro 𝗛𝗼𝘄 𝘁𝗼 𝗔𝘃𝗼𝗶𝗱 𝗦𝗜𝗠 𝗦𝘄𝗮𝗽𝗽𝗶𝗻𝗴 𝗟𝗲𝗮𝗳𝗹𝗲𝘁 this leaflet, addresses the sim swapping attacks, how to recognise them and. To avoid succumbing to a sim jacking, it is crucial that phone users take steps to protect their devices. from implementing security measures with their phone company and limiting how many personal accounts are associated with their number, each can prove useful to prevent a sim swapping attack. In this study, we give an overview of how sim swapping attacks work, list measures that providers can take to mitigate the attack and make recommendations for policy makers and authorities in the telecom sector and other sectors. In a sim swapping attack, an attacker takes over your mobile phone number by asking the mobile telecom provider to link your number to a sim card under the attacker’s control.
Comments are closed.