How To Avoid Add Secrets On A Docker Dockerfile
Intro Guide To Dockerfile Best Practices Docker To consume a secret in a build and make it accessible to the run instruction, use the mount=type=secret flag in the dockerfile. Learn dockerfile secrets management: avoid env arg leaks, use buildkit secret, ssh mounts, multi stage builds, and runtime secrets in compose kubernetes. we’ve all done it.

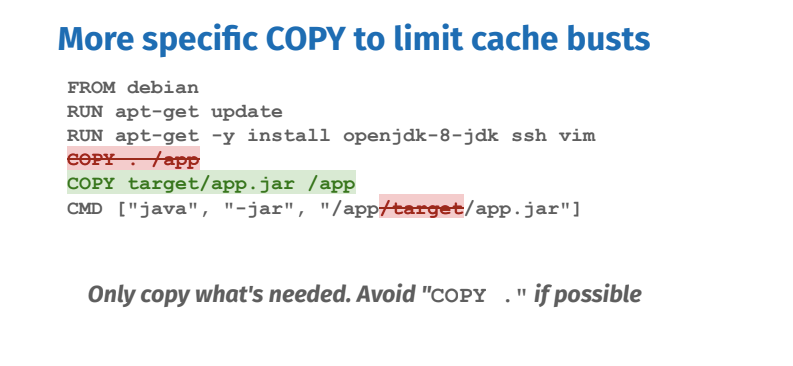
Secrets Docker Docs To reduce risks, avoid storing sensitive data directly in dockerfiles or using env to pass secrets. instead, inject them at runtime via a secure mechanism like docker compose or through orchestration systems. The secrets should be used during run time and provided by execution environment. also everything that is executing during a container build is written down as layers and available later to anyone who is able to get access to an image. That’s why dockerfile secrets, and especially dockerfile secrets environment variables, are dangerous: your credentials or private keys may remain embedded in old layers, fully recoverable through docker history or exported image tarballs. Over the years, i’ve seen multiple teams get caught out by their approach to using docker images. there are quite a few quirks to dockerfiles that don’t entirely make sense initially, especially around layers and how you can chain certain things together to build more efficient images.

Secrets Portainer Documentation That’s why dockerfile secrets, and especially dockerfile secrets environment variables, are dangerous: your credentials or private keys may remain embedded in old layers, fully recoverable through docker history or exported image tarballs. Over the years, i’ve seen multiple teams get caught out by their approach to using docker images. there are quite a few quirks to dockerfiles that don’t entirely make sense initially, especially around layers and how you can chain certain things together to build more efficient images. A safer approach starts with separating build time vs run time secrets, minimizing where secrets can be persisted (image layers, metadata, state), and using purpose built mechanisms that scope access to only the containers that need it. You may want to use this to avoid leaking secrets in your docker images such as using an api key or token to pull private packages. Here, we avoid hardcoding the secret directly into a dockerfile or a script. instead, we depend on an environment variable to store the secret, isolating it from the build configuration. Avoid plain environment variables; prefer file based secret mounts. always scan docker images for exposed secrets to mitigate supply chain risks. read on for actionable best practices and implementation examples. secrets management in docker is a critical security concern for any business.
Don T Leak Your Docker Image S Build Secrets A safer approach starts with separating build time vs run time secrets, minimizing where secrets can be persisted (image layers, metadata, state), and using purpose built mechanisms that scope access to only the containers that need it. You may want to use this to avoid leaking secrets in your docker images such as using an api key or token to pull private packages. Here, we avoid hardcoding the secret directly into a dockerfile or a script. instead, we depend on an environment variable to store the secret, isolating it from the build configuration. Avoid plain environment variables; prefer file based secret mounts. always scan docker images for exposed secrets to mitigate supply chain risks. read on for actionable best practices and implementation examples. secrets management in docker is a critical security concern for any business.

Dockerfile Secrets Here, we avoid hardcoding the secret directly into a dockerfile or a script. instead, we depend on an environment variable to store the secret, isolating it from the build configuration. Avoid plain environment variables; prefer file based secret mounts. always scan docker images for exposed secrets to mitigate supply chain risks. read on for actionable best practices and implementation examples. secrets management in docker is a critical security concern for any business.

How To Keep Docker Secrets Secure Complete Guide
Comments are closed.