How To Automatically Run Detect Secrets With Git Pre Commit Hooks Secure Your Code With Pre Commit
Automating Code Checks With Git Pre Commit Hooks Pre commit hooks catch leaked api keys before they enter git history. step by step setup for gitleaks, detect secrets, and trufflehog with real config examples. This post explores how to integrate git secrets into your pre commit workflow using pre commit, a framework for managing and maintaining multi language pre commit hooks.
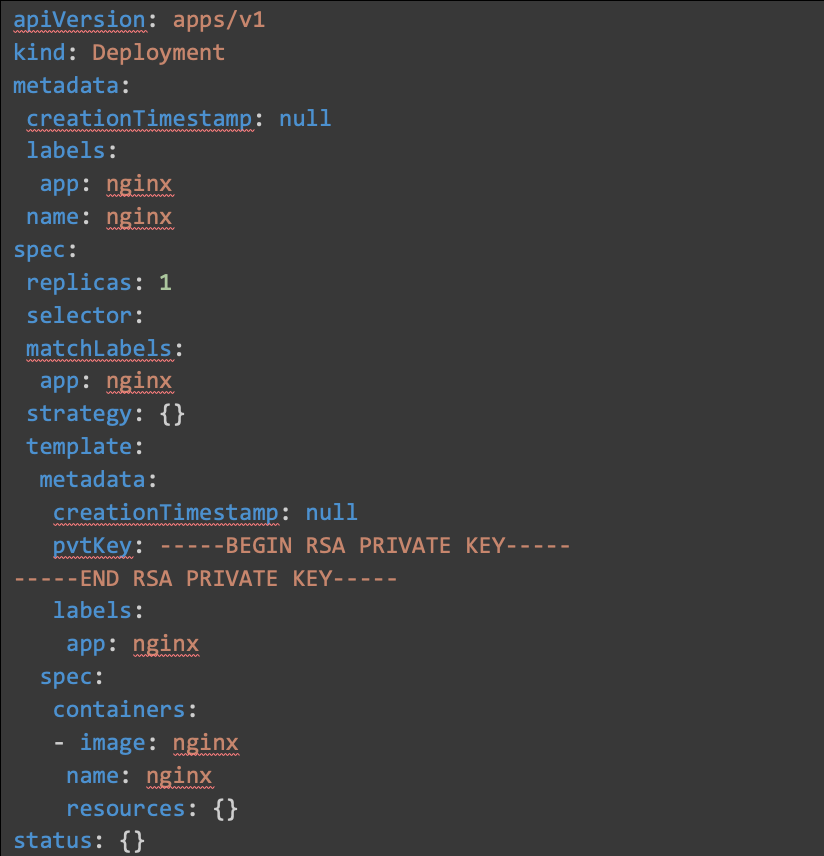
The Benefit Of Using Git Pre Commit Hooks Here's a quick example of how to ensure a git repository is scanned for secrets on each commit: add a configuration template if you want to add hooks to all repositories you initialize or clone in the future. add hooks to all your local repositories. add custom providers to scan for security credentials. Learn how to prevent secrets exposure in your code. orca’s pre commit and pre receive git hooks offer automated secret detection to secure your developer workflow. A practical example to use git hooks to automatically check for secrets before committing. Stop secrets from reaching your repository. set up pre commit hooks, secret detection with gitleaks, credential rotation, and a complete git security workflow.
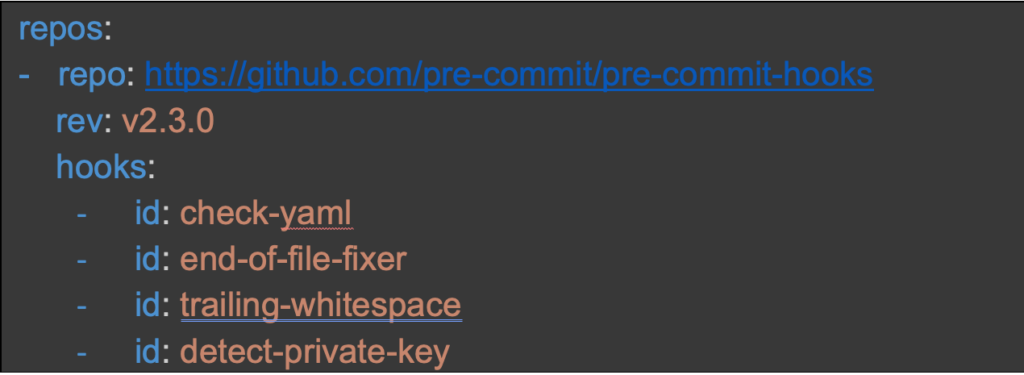
The Benefit Of Using Git Pre Commit Hooks A practical example to use git hooks to automatically check for secrets before committing. Stop secrets from reaching your repository. set up pre commit hooks, secret detection with gitleaks, credential rotation, and a complete git security workflow. Pre commit secret detection prevents credentials from entering your codebase, stopping breaches before they start. in devsecops, shifting security left means catching secrets at the developer's workstation—the earliest possible intervention point. How to design and deploy a central pre commit hook that blocks secrets from git history with low developer friction and few false positives. Now, your pre commit hook will run every time you attempt to commit changes, helping to enforce code quality and security checks before the commit is finalized. Implement security checks before code is committed using git hooks. learn gitleaks, detect secrets, and the pre commit framework to catch vulnerabilities early. pre commit hooks run automated checks on your code before it enters version control.
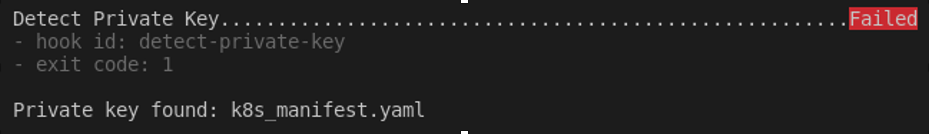
The Benefit Of Using Git Pre Commit Hooks Pre commit secret detection prevents credentials from entering your codebase, stopping breaches before they start. in devsecops, shifting security left means catching secrets at the developer's workstation—the earliest possible intervention point. How to design and deploy a central pre commit hook that blocks secrets from git history with low developer friction and few false positives. Now, your pre commit hook will run every time you attempt to commit changes, helping to enforce code quality and security checks before the commit is finalized. Implement security checks before code is committed using git hooks. learn gitleaks, detect secrets, and the pre commit framework to catch vulnerabilities early. pre commit hooks run automated checks on your code before it enters version control.
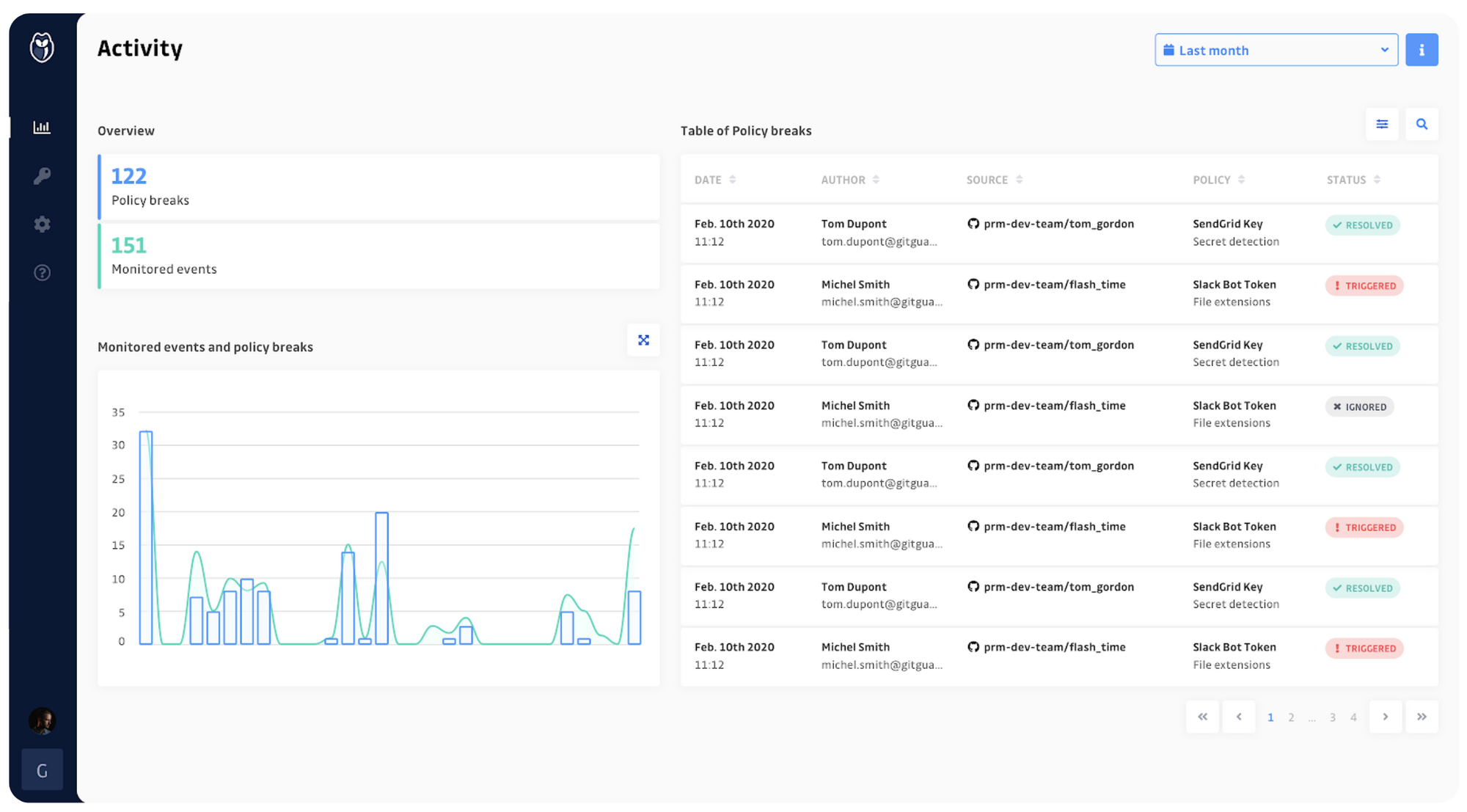
Git Hooks Security Post Commit Hook Gitguardian Blog Now, your pre commit hook will run every time you attempt to commit changes, helping to enforce code quality and security checks before the commit is finalized. Implement security checks before code is committed using git hooks. learn gitleaks, detect secrets, and the pre commit framework to catch vulnerabilities early. pre commit hooks run automated checks on your code before it enters version control.
Creating A Pre Commit Git Hook To Detect Secrets
Comments are closed.