How To Achieve Role Based Access Control Using Network Configuration Manager

Manageengine Network Configuration Manager Automated Nccm Get to know how you can limit user access and permissions with the role based access control (rbac) in network configuration manager v12. If you're not yet familiar with these concepts, see fundamentals of role based administration. use the information in this article to create and configure role based administration and related security settings.
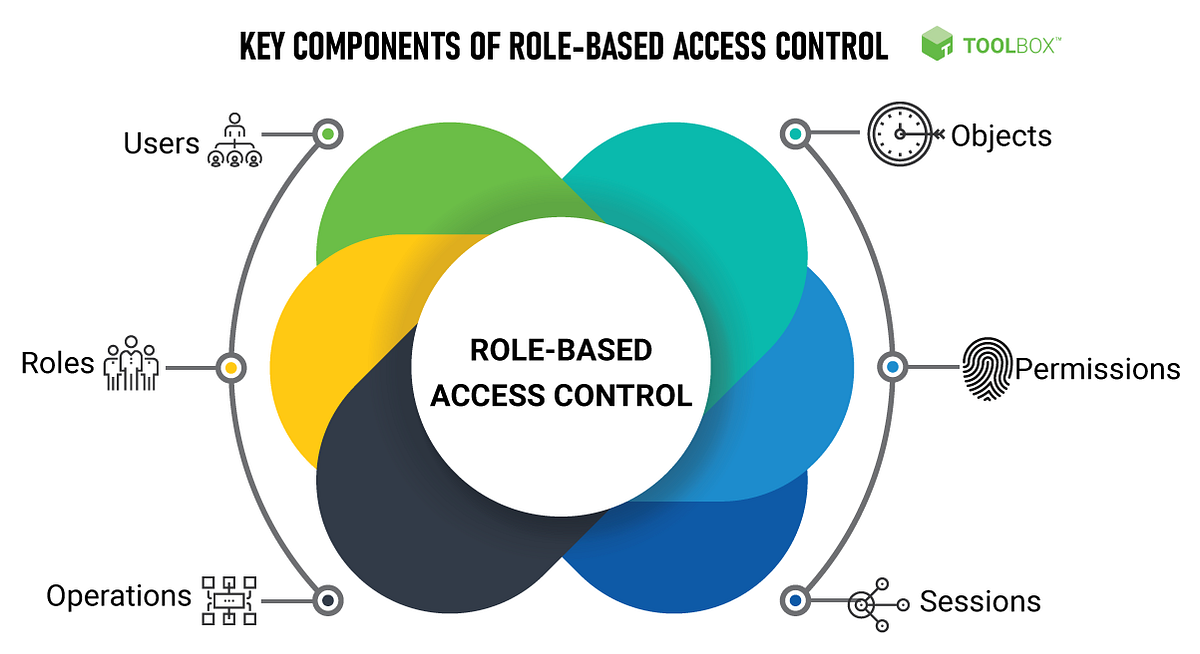
Role Based Access Control Rbac Made Easy How To Implement It In Your In this video, we shall see how to define access levels and a scope of access that restricts users from accessing certain devices or device groups more. Introduction the role based access control (rbac) support has been added to the network configuration management (ncm) that permits you to restrict a user according to the user roles and permissions. using rbac, you can control which actions an authenticated user is permitted. With configuration manager, you use role based administration to secure the access that administrative users need to use configuration manager. you also secure access to the objects that you manage, like collections, deployments, and sites. In role based access control, rbac solutions are provided to users who are assigned roles depending on the resources they need access to. all other parts of the network are rendered inaccessible to them, ensuring no unauthorized accesses or changes are made to network resources.

Role Based Access Control Implementation And Management Guide With configuration manager, you use role based administration to secure the access that administrative users need to use configuration manager. you also secure access to the objects that you manage, like collections, deployments, and sites. In role based access control, rbac solutions are provided to users who are assigned roles depending on the resources they need access to. all other parts of the network are rendered inaccessible to them, ensuring no unauthorized accesses or changes are made to network resources. Master role based access control (rbac) in microsoft configuration manager (sccm) in this detailed tutorial, learn how to implement and manage rbac (role based access control). Role based access control (rbac) is a method of granting permissions to users based on their roles in an organization. this article provides a step by step guide on how to set up rbac. Learn how to implement role based access control (rbac) with step by step best practices and real world examples to enhance your access security. Discover a comprehensive guide to implementing role based access control (rbac), including best practices, common challenges, and how mst’s solutions can enhance the process.
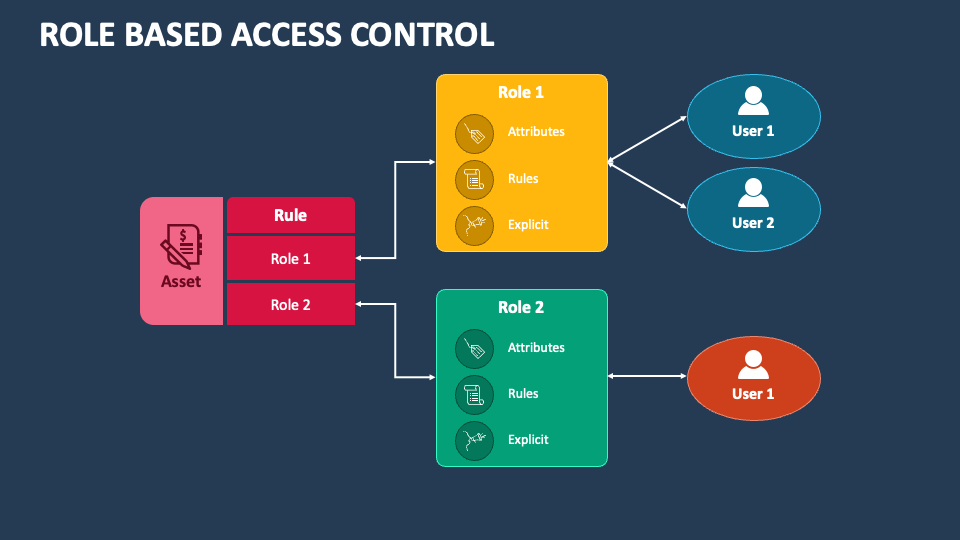
Role Based Access Control Powerpoint And Google Slides Template Ppt Master role based access control (rbac) in microsoft configuration manager (sccm) in this detailed tutorial, learn how to implement and manage rbac (role based access control). Role based access control (rbac) is a method of granting permissions to users based on their roles in an organization. this article provides a step by step guide on how to set up rbac. Learn how to implement role based access control (rbac) with step by step best practices and real world examples to enhance your access security. Discover a comprehensive guide to implementing role based access control (rbac), including best practices, common challenges, and how mst’s solutions can enhance the process.

Role Based Access Control Secure Access Management Learn how to implement role based access control (rbac) with step by step best practices and real world examples to enhance your access security. Discover a comprehensive guide to implementing role based access control (rbac), including best practices, common challenges, and how mst’s solutions can enhance the process.
Comments are closed.