How Risk Based Authentication Works
Risk Based Authentication Improves Password Security Without Risk based authentication is a way to verify that users are behaving normally, and therefore less likely to be carrying out fraud, without disturbing the user. risk based authentication runs in the background and only prompts the user for additional authentication when necessary. Risk based authentication provides smarter protection by analyzing user behavior, device, location, and system sensitivity before allowing access. this method reduces unauthorized access, improves security, and helps organizations protect sensitive data without slowing down trusted users.
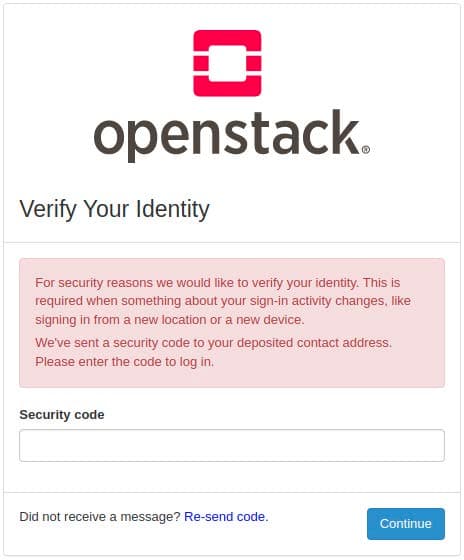
Open Source Risk Based Authentication On a low risk (e.g. same device as always), access to the website is granted. on a medium risk (e.g. unknown device), the website asks for additional information to confirm the claimed identity (e.g. confirmation of email address). on a high risk, access is denied. Risk based authentication (rba) is an authentication method in which varying levels of stringency are applied to a system's authentication process based on the likelihood that access to that system could result in its compromise. Learn what risk based authentication is, how it works, key benefits, and real world use cases to strengthen security without adding login friction. Learn how risk based authentication (rba) works, how to implement it with pam and psm, and why context aware login protection matters more than ever. learn how ai powered, real time session monitoring helps stop insider threats and privileged attacks before they escalate.
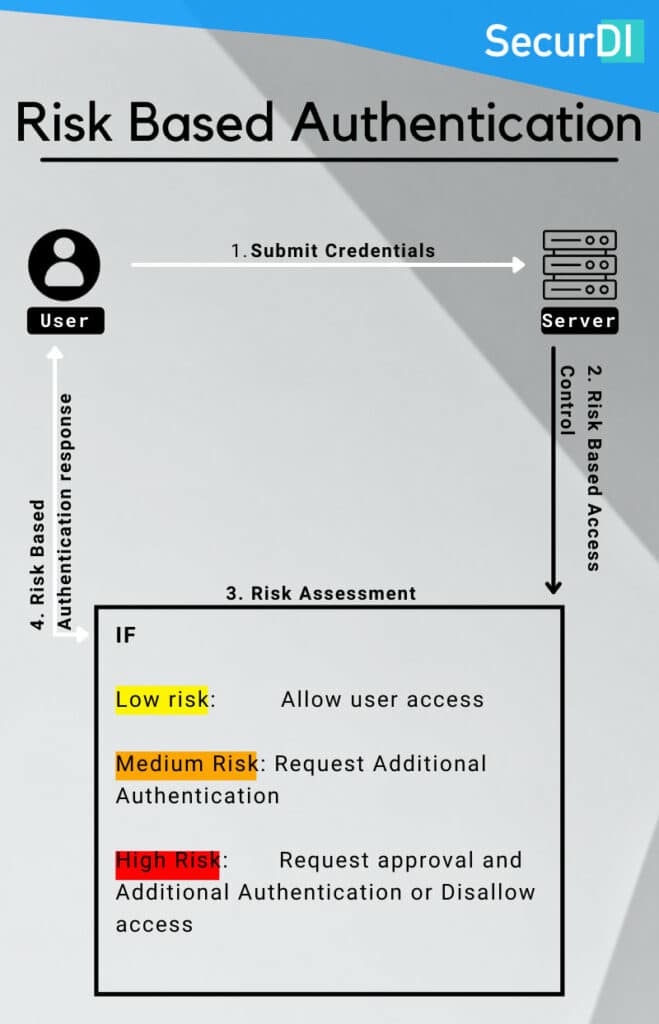
Risk Based Authentication Security And User Experience Learn what risk based authentication is, how it works, key benefits, and real world use cases to strengthen security without adding login friction. Learn how risk based authentication (rba) works, how to implement it with pam and psm, and why context aware login protection matters more than ever. learn how ai powered, real time session monitoring helps stop insider threats and privileged attacks before they escalate. Risk based authentication is a security method that evaluates login risk before granting access. learn its definition, how it works, benefits, and real world applications. Risk based authentication is a dynamic access control approach that adjusts authentication strength and steps according to assessed risk at the time of access. it is not a single authentication mechanism; rather it orchestrates multiple signals, policies, and controls to make per request decisions. Risk based authentication proves that a verified user is accessing an account, adapting how that proof is requested based on context. it analyzes factors like device, location, and network to determine if a login attempt looks typical or suspicious. This article discusses everything you need to know about risk based authentication. learn what rba is and how it works.
Cover Risk based authentication is a security method that evaluates login risk before granting access. learn its definition, how it works, benefits, and real world applications. Risk based authentication is a dynamic access control approach that adjusts authentication strength and steps according to assessed risk at the time of access. it is not a single authentication mechanism; rather it orchestrates multiple signals, policies, and controls to make per request decisions. Risk based authentication proves that a verified user is accessing an account, adapting how that proof is requested based on context. it analyzes factors like device, location, and network to determine if a login attempt looks typical or suspicious. This article discusses everything you need to know about risk based authentication. learn what rba is and how it works.
Comments are closed.