How Quantum Computing Breaks Rsa Shors Algorithm Explained

Shors Algorithm Pdf Quantum Computing Quantum Mechanics In 1994, mathematician peter shor developed a quantum factoring algorithm that, when executed by a powerful enough quantum computer, could theoretically break rsa encryption. shor’s algorithm relies heavily on the quantum fourier transform (qft). In this deep technical dive, we’ll explore exactly how shor’s algorithm works, why it’s efficient on a quantum computer, and what makes this possible (yes, the quantum fourier.

Shor S Algorithm Explained How Quantum Computing Breaks Rsa By Shor’s algorithm uses quantum computing to factor large numbers efficiently, threatening rsa encryption. here’s how it works and why it matters for…. Discover how shor's algorithm can break rsa encryption using quantum computing. learn its principles, impact, and future implications. By using shor’s algorithm efficiently solve the period finding problem, we can reduce these “hard” problems to ones that quantum computers can solve in polynomial time. in this article, we’ll explore how shor’s algorithm can be applied to break rsa and ecc encryption schemes. Pbs infinite series created two videos explaining the math behind shor's algorithm, "how to break cryptography" and "hacking at quantum speed with shor's algorithm".
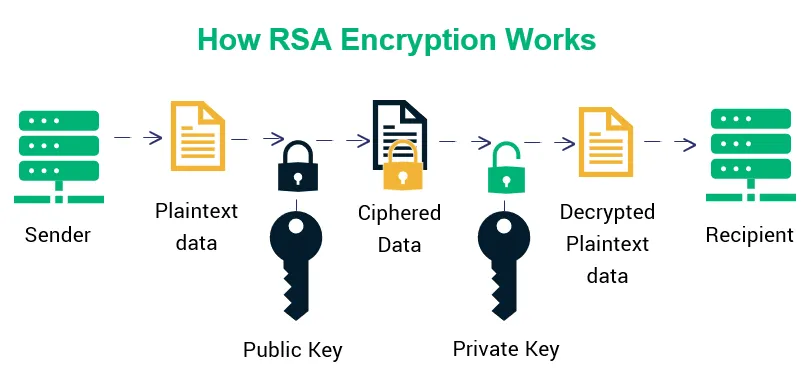
Shor S Algorithm Explained How Quantum Computing Breaks Rsa By By using shor’s algorithm efficiently solve the period finding problem, we can reduce these “hard” problems to ones that quantum computers can solve in polynomial time. in this article, we’ll explore how shor’s algorithm can be applied to break rsa and ecc encryption schemes. Pbs infinite series created two videos explaining the math behind shor's algorithm, "how to break cryptography" and "hacking at quantum speed with shor's algorithm". Clear explanation of shor’s algorithm: how quantum computers break rsa and ecc, qubit requirements, timeline estimates, and why pq migration is urgent now. Shor’s algorithm’s ability to factorize quickly on a quantum computer undermines rsa’s security assumptions, necessitating the exploration of post quantum cryptographic solutions to ensure secure communication in the quantum era. Shor’s algorithm remains one of the most significant theoretical threats to modern cryptography as it fundamentally breaches rsa’s security assumptions. while we are possibly a few years away from efficiently factoring 2048 bit keys, the urgency to transition to quantum safe encryption is real. Rsa is secure today because factoring large numbers is computationally infeasible for classical computers. but quantum computing introduces a fundamentally different computational model.

Shor S Algorithm Explained How Quantum Computing Breaks Rsa By Clear explanation of shor’s algorithm: how quantum computers break rsa and ecc, qubit requirements, timeline estimates, and why pq migration is urgent now. Shor’s algorithm’s ability to factorize quickly on a quantum computer undermines rsa’s security assumptions, necessitating the exploration of post quantum cryptographic solutions to ensure secure communication in the quantum era. Shor’s algorithm remains one of the most significant theoretical threats to modern cryptography as it fundamentally breaches rsa’s security assumptions. while we are possibly a few years away from efficiently factoring 2048 bit keys, the urgency to transition to quantum safe encryption is real. Rsa is secure today because factoring large numbers is computationally infeasible for classical computers. but quantum computing introduces a fundamentally different computational model.
Shor S Algorithm Explained How Quantum Computing Breaks Rsa By Shor’s algorithm remains one of the most significant theoretical threats to modern cryptography as it fundamentally breaches rsa’s security assumptions. while we are possibly a few years away from efficiently factoring 2048 bit keys, the urgency to transition to quantum safe encryption is real. Rsa is secure today because factoring large numbers is computationally infeasible for classical computers. but quantum computing introduces a fundamentally different computational model.
Shor S Algorithm Explained How Quantum Computing Breaks Rsa By
Comments are closed.