How Phishing Works Biondit

How Phishing Works Biondit You may not realise it, but you are a phishing target at work and at home. you're the most effective way to detect and stop phishing. it starts with being aware and understanding how phishing works. Phishing is a common method of online identity theft and virus spreading. find out how phishing scams work and learn ways to protect yourself from phishing.
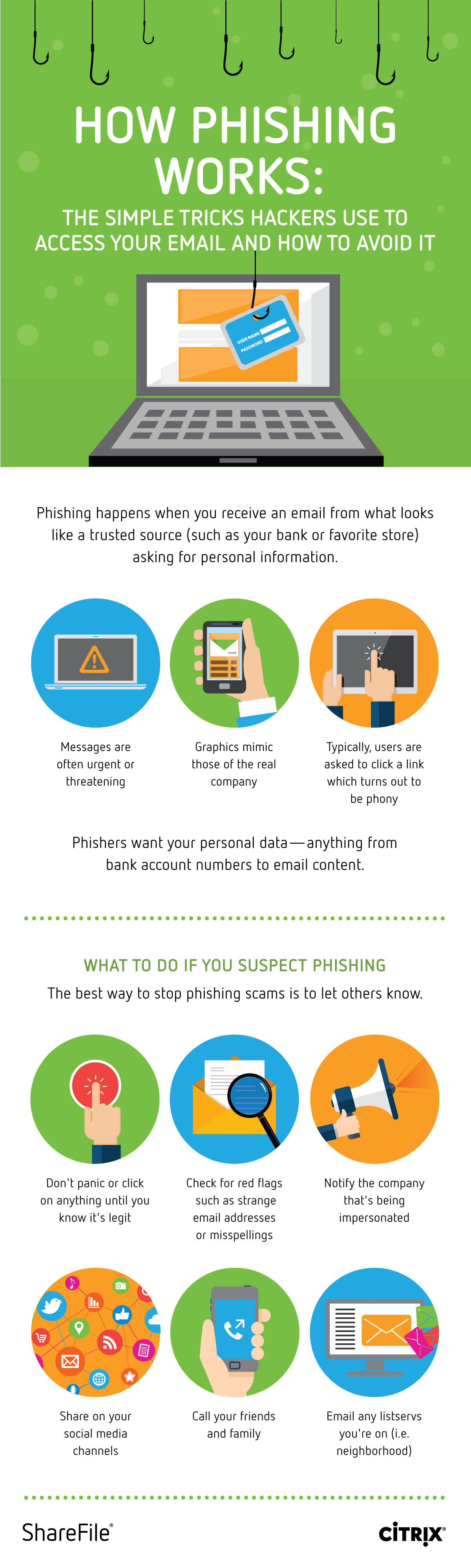
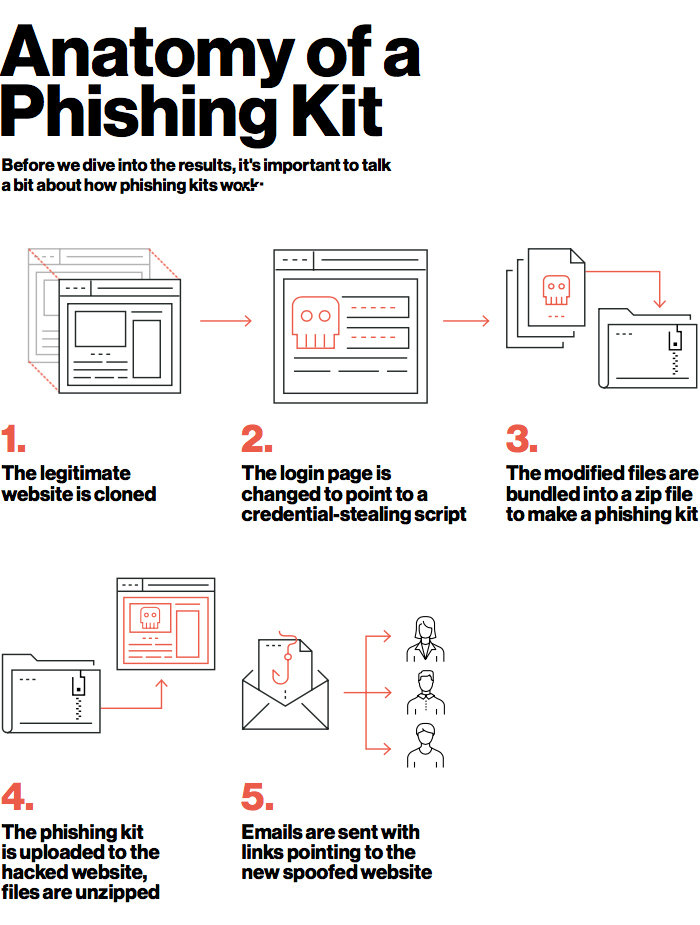
Stop Think Connect But how does a phishing attack work, and what steps can individuals and organisations take to protect themselves? this article will provide a detailed breakdown of how phishing attacks are executed and offer insights into recognising and defending against this growing threat. Phishing is a cyberattack where attackers use fake messages or websites to trick victims into giving away sensitive information. it works like “fishing,” using bait to lure targets into clicking harmful links or entering confidential data. Phishing is one of the most pervasive and damaging forms of cybercrime in the modern digital landscape. it operates through deception, exploiting human psychology rather than technological flaws. Find out what is a phishing attack, how it works and how can you protect your company against phishing. keep your digital assets safe.

How Phishing Works Axon It Phishing is one of the most pervasive and damaging forms of cybercrime in the modern digital landscape. it operates through deception, exploiting human psychology rather than technological flaws. Find out what is a phishing attack, how it works and how can you protect your company against phishing. keep your digital assets safe. This article covers everything you need to know about phishing. read to learn what it is, how it works, its features, and how to prevent phishing attacks. Learn how phishing works, the types of phishing attacks, and ways to recognize fake emails to protect yourself and your information from cyber threats. John podesta, hillary clinton’s campaign chair, offered his gmail password during the 2016 presidential election, and employees at the university of kansas responded to a phishing email that handed their paycheck deposit information, resulting in them losing pay. Cyberattacks called phishing use deceptive "social engineering" techniques to trick people into divulging sensitive data, transferring money, and more.
How Phishing Works And How To Prevent It Techcentral Ie This article covers everything you need to know about phishing. read to learn what it is, how it works, its features, and how to prevent phishing attacks. Learn how phishing works, the types of phishing attacks, and ways to recognize fake emails to protect yourself and your information from cyber threats. John podesta, hillary clinton’s campaign chair, offered his gmail password during the 2016 presidential election, and employees at the university of kansas responded to a phishing email that handed their paycheck deposit information, resulting in them losing pay. Cyberattacks called phishing use deceptive "social engineering" techniques to trick people into divulging sensitive data, transferring money, and more.
How Phishing Works Howstuffworks John podesta, hillary clinton’s campaign chair, offered his gmail password during the 2016 presidential election, and employees at the university of kansas responded to a phishing email that handed their paycheck deposit information, resulting in them losing pay. Cyberattacks called phishing use deceptive "social engineering" techniques to trick people into divulging sensitive data, transferring money, and more.
Comments are closed.