How Phishing Attacks Work A Step By Step Guide Phishing Attack Phishingattacks Cybersecurity

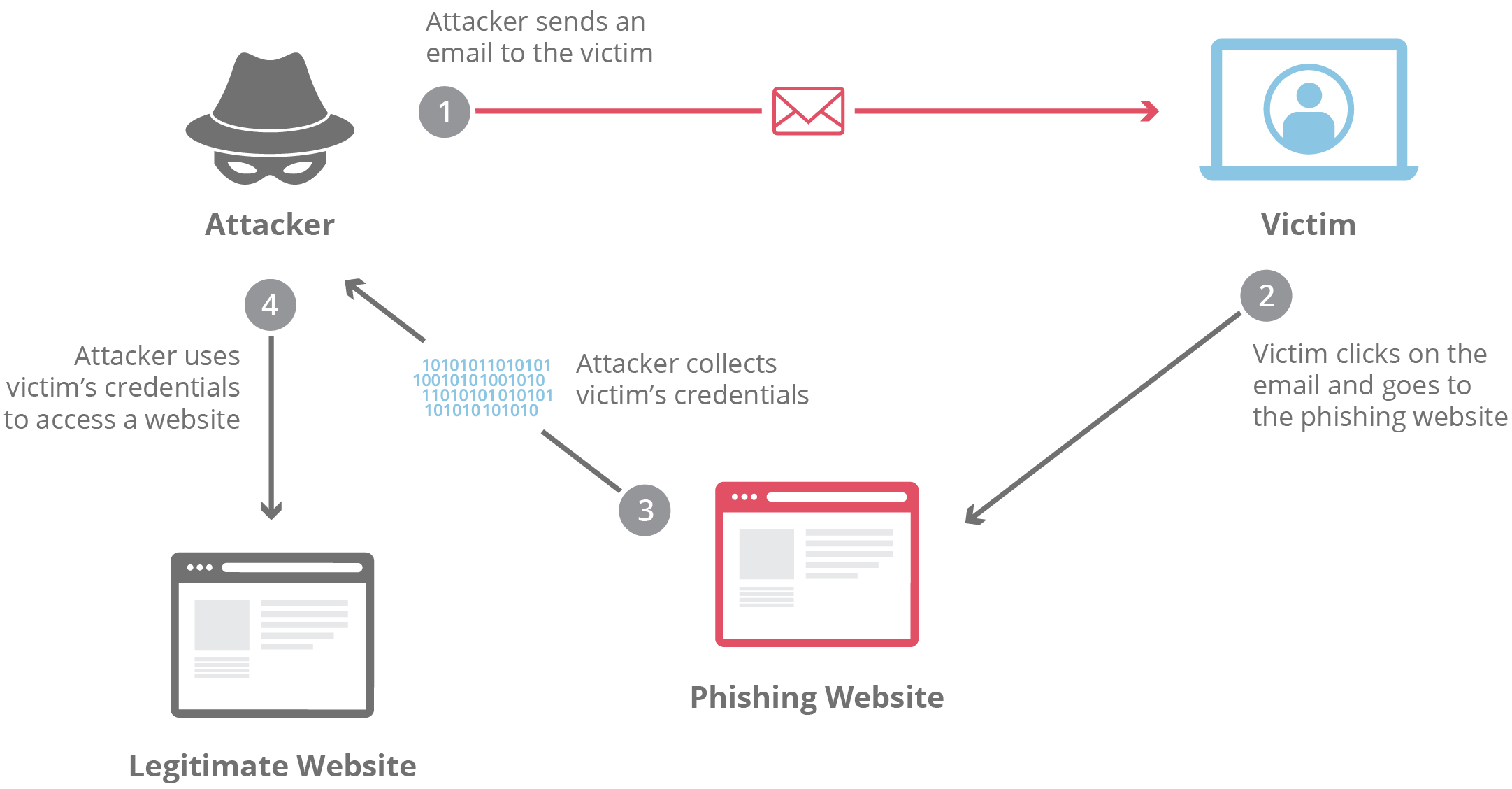
01 Phishing Attacks Guide Pdf What is a phishing attack? phishing is a type of cyberattack where threat actors masquerade as legitimate companies or individuals to steal sensitive information such as usernames, passwords, credit card numbers, and other personal details. It's not about complex code or breaking through firewalls; it's about playing on human emotions and trust. so, how do these sneaky attacks actually unfold? let's break it down, step by step.

How Does A Phishing Attack Work Phishing Attacks And Strategies Ppt Slide The guidance for software manufacturers focuses on secure by design and default tactics and techniques. manufacturers should develop and supply software that is secure against the most prevalent phishing threats, thereby increasing the cybersecurity posture of their customers. Explore our guide to understand phishing, a tactic employed by cybercriminals to manipulate individuals into taking actions unknowingly. This tutorial on what is phishing, helped you learn about the basics of a phishing attack, how it works, the various types of phishing attacks, and some preventive measures that can be taken to prevent such attacks. Phishing is a common method of online identity theft and virus spreading. find out how phishing scams work and learn ways to protect yourself from phishing.
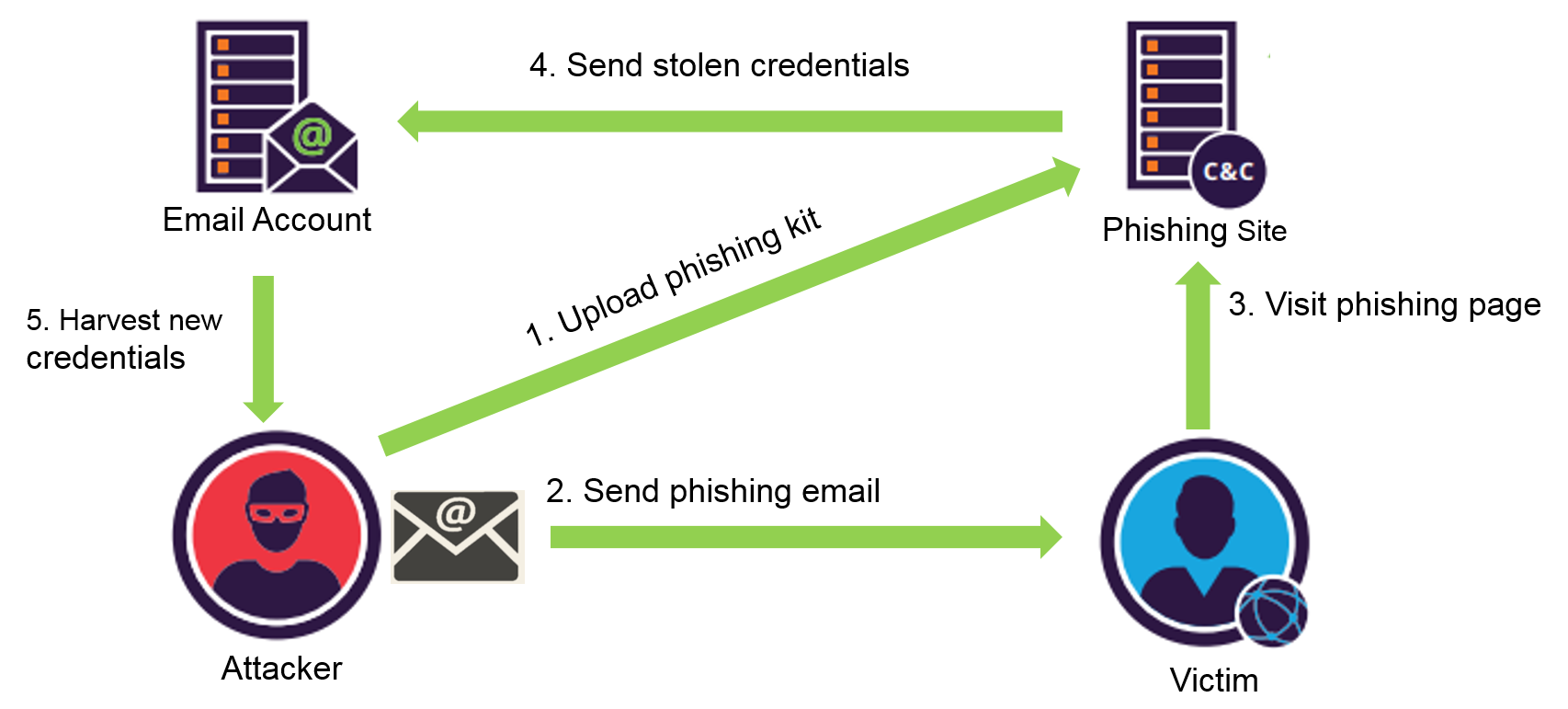
Phishing Attack Flow Figure 1 This tutorial on what is phishing, helped you learn about the basics of a phishing attack, how it works, the various types of phishing attacks, and some preventive measures that can be taken to prevent such attacks. Phishing is a common method of online identity theft and virus spreading. find out how phishing scams work and learn ways to protect yourself from phishing. Phishing is the biggest cause of hacking attacks. learn all about phishing: examples, prevention tips, how to phish your users, and more resources with knowbe4. Phishing attacks are designed to appear to come from legitimate companies and individuals. cybercriminals are continuously innovating and using increasingly sophisticated techniques, including spear phishing (an attack directed at a specific person or group) and other strategies, to trick users into clicking or tapping. Learn what phishing attacks are, how they impact organizations, and different ways to prevent these attacks from impacting your team. Stop phishing attacks before they start! learn the step by step anatomy of a phishing breach, from the deceptive email click to full scale data compromise. protect your business now.
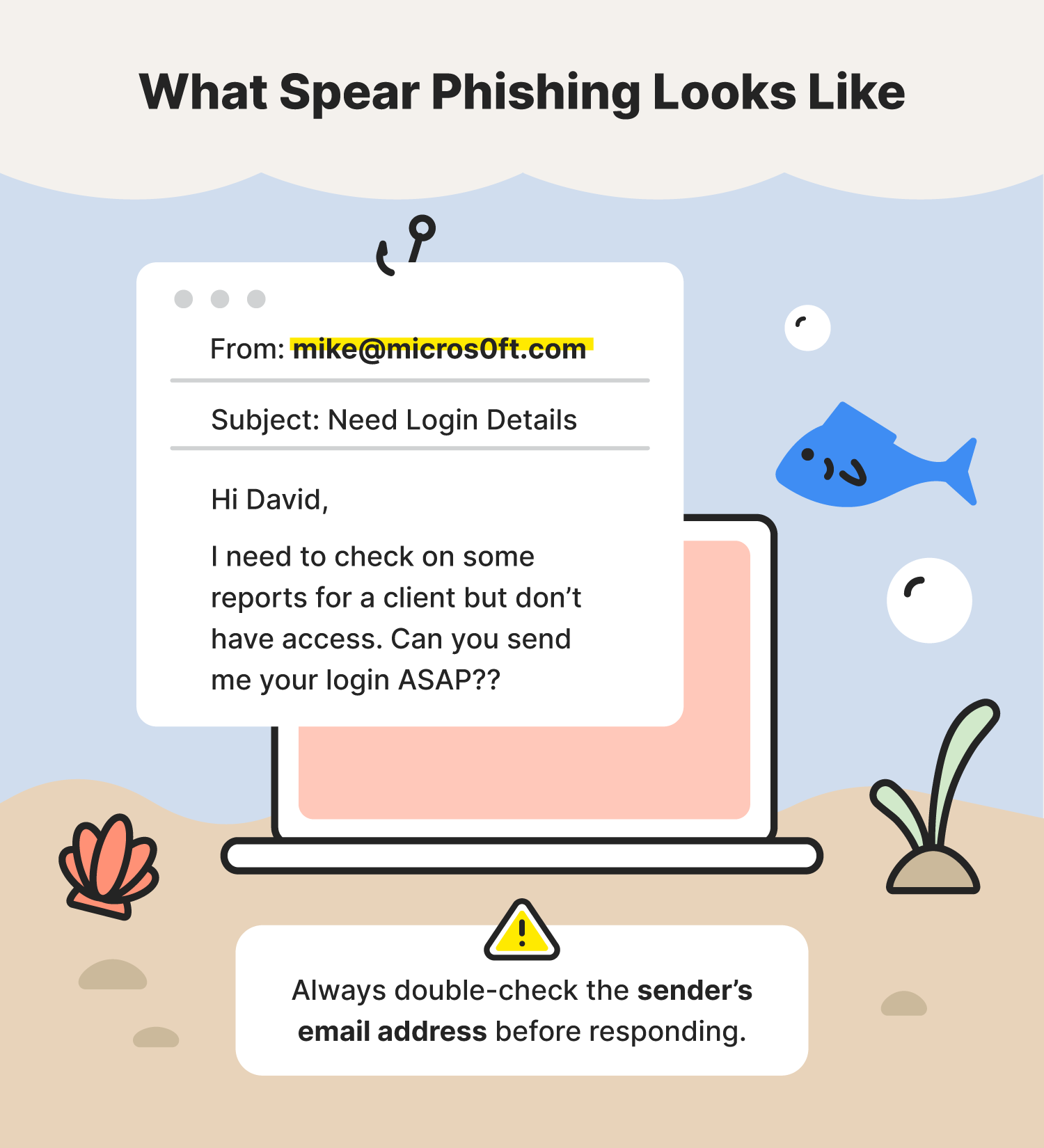
Phishing Attack Phishing is the biggest cause of hacking attacks. learn all about phishing: examples, prevention tips, how to phish your users, and more resources with knowbe4. Phishing attacks are designed to appear to come from legitimate companies and individuals. cybercriminals are continuously innovating and using increasingly sophisticated techniques, including spear phishing (an attack directed at a specific person or group) and other strategies, to trick users into clicking or tapping. Learn what phishing attacks are, how they impact organizations, and different ways to prevent these attacks from impacting your team. Stop phishing attacks before they start! learn the step by step anatomy of a phishing breach, from the deceptive email click to full scale data compromise. protect your business now.
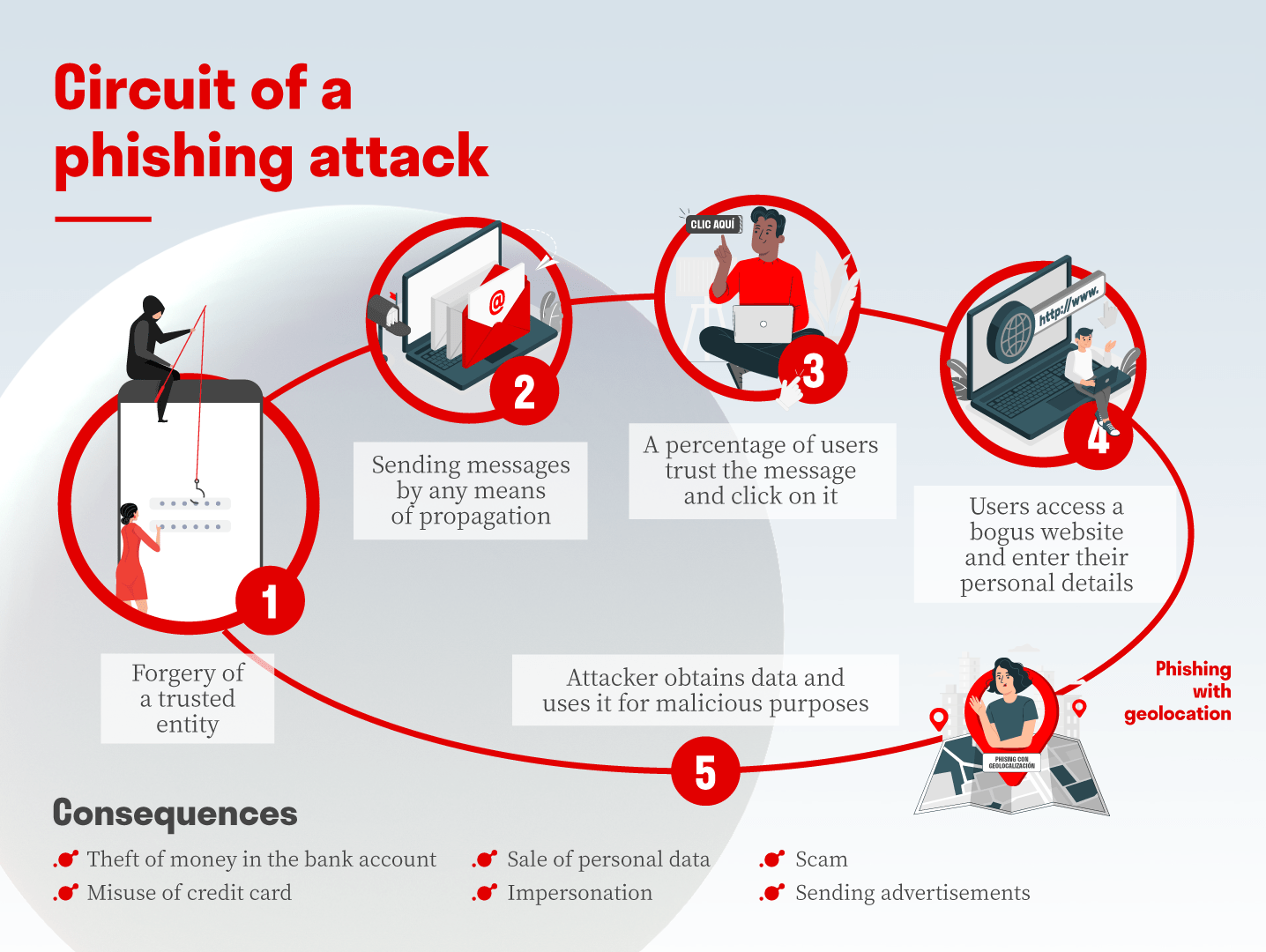
Phishing Attacks Hanley S Consulting Services Learn what phishing attacks are, how they impact organizations, and different ways to prevent these attacks from impacting your team. Stop phishing attacks before they start! learn the step by step anatomy of a phishing breach, from the deceptive email click to full scale data compromise. protect your business now.
Phishing Attack Phishing Wikipedia
Comments are closed.