How Hacking Works Programmerhumor Io

How Hacking Works Programmerhumor Io Someone discovered the perfect way to summon the ghost from the ring using python. just create an infinite loop of a turtle drawing negative circles, and you've got yourself a cursed hallway experience. the perfect code for when you want your programming assignments to be literally haunted. 2.8k votes, 69 comments. 3.2m subscribers in the programmerhumor community. for anything funny related to programming and software development.

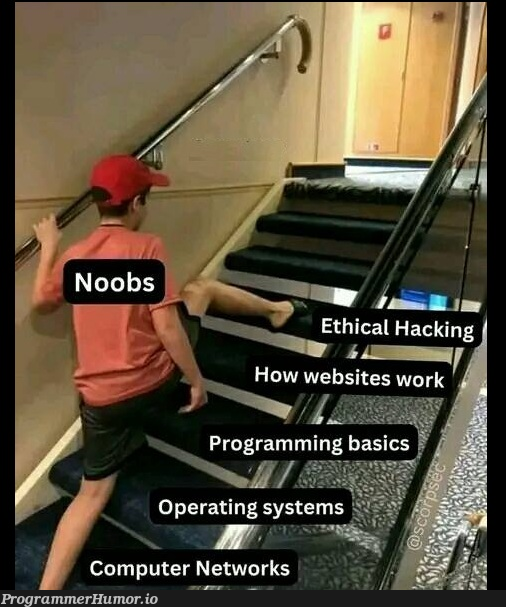
Coding Hacking Programmerhumor Io In this video, we break down how hacking really works—from recon to exploitation, tools used by real hackers, and how ethical hackers help secure our digital world. The focus is on understanding the basics of how computers and the internet work, introducing essential tools, and fostering a hacker's mindset. you'll learn to navigate the command line, explore simple network tools, and set up a safe practice environment to experiment without risks. The focus is on understanding the basics of how computers and the internet work, introducing essential tools, and fostering a hacker’s mindset. you’ll learn to navigate the command line, explore simple network tools, and set up a safe practice environment to experiment without risks. Learn how to hack. explore free ctfs, test your skills, watch video lessons, meet fellow hackers, and get experienced mentoring here.
Accidentalvisualhacking Programmerhumor Io The focus is on understanding the basics of how computers and the internet work, introducing essential tools, and fostering a hacker’s mindset. you’ll learn to navigate the command line, explore simple network tools, and set up a safe practice environment to experiment without risks. Learn how to hack. explore free ctfs, test your skills, watch video lessons, meet fellow hackers, and get experienced mentoring here. An still taken from indian series asur! the actors hack national database servers using this code xd. Linux runs everything from servers to smartphones to mars rovers and apparently the embedded systems in adult toys. the beauty here is that linux's success is so overwhelming that you can't escape it even in your most private moments. linus torvalds really did take over the world, one microcontroller at a time. That moment when your super strict firewall rules work perfectly – by blocking even your own ssh connection to the remote server. now some poor sysadmin has to make the digital walk of shame: a 500km road trip just to press a power button. In just 5 minutes, we'll break down the basics of hacking, demystifying the techniques and methods used by hackers. whether you're a beginner curious about cybersecurity or someone looking to.

Hacking Starter Pack Programmerhumor Io An still taken from indian series asur! the actors hack national database servers using this code xd. Linux runs everything from servers to smartphones to mars rovers and apparently the embedded systems in adult toys. the beauty here is that linux's success is so overwhelming that you can't escape it even in your most private moments. linus torvalds really did take over the world, one microcontroller at a time. That moment when your super strict firewall rules work perfectly – by blocking even your own ssh connection to the remote server. now some poor sysadmin has to make the digital walk of shame: a 500km road trip just to press a power button. In just 5 minutes, we'll break down the basics of hacking, demystifying the techniques and methods used by hackers. whether you're a beginner curious about cybersecurity or someone looking to.

Anti Hacking Software Programmerhumor Io That moment when your super strict firewall rules work perfectly – by blocking even your own ssh connection to the remote server. now some poor sysadmin has to make the digital walk of shame: a 500km road trip just to press a power button. In just 5 minutes, we'll break down the basics of hacking, demystifying the techniques and methods used by hackers. whether you're a beginner curious about cybersecurity or someone looking to.
How To Learn Hacking Programmerhumor Io
Comments are closed.