How Hackers Used Stolen Github Tokens To Access Private Source Code

How Hackers Used Stolen Github Tokens To Access Private Source Code Attackers have used stolen oauth tokens issued to travis ci and heroku to gain access to private git repositories on github. here we take a look at exactly what happened, why it's significant, and how to mitigate the issue. Recently, a security researcher discovered an exposed pat in a public npm package, compromising one of malaysia’s largest point of sale providers. this incident highlights the growing risk of credential leaks in open source ecosystems. understand how github pats can be exploited if leaked.

How Hackers Used Stolen Github Tokens To Access Private Source Code One common observed attack pattern exploits situations where a user’s personal access token (pat) has not been properly and securely stored. if a threat actor is able to obtain a github user’s pat, they then may add a malicious actions workflow file to repositories accessible to the user. Hackers exploit github’s oauth2 device flow in new phishing campaign to steal tokens, bypass security, and access dev accounts and code. Gitguardian reported immediate exploitation: “initial discussions with affected developers confirmed that attackers were actively exploiting the stolen secrets, including aws access keys and database credentials.”. If a malicious actor discovers a github token, they may be able to access private repositories, steal private source code, or inject malicious code.
How Hackers Used Stolen Github Tokens To Access Private Source Code Gitguardian reported immediate exploitation: “initial discussions with affected developers confirmed that attackers were actively exploiting the stolen secrets, including aws access keys and database credentials.”. If a malicious actor discovers a github token, they may be able to access private repositories, steal private source code, or inject malicious code. Late last week, github disclosed that an unauthorized party breached its code repository. github itself wasn’t impacted, but the threat actor used compromised oauth tokens issued by two oauth integrators heroku and travic ci to download data of “dozens of organizations.”. A new supply chain attack on github, dubbed 'ghostaction,' has compromised 3,325 secrets, including pypi, npm, dockerhub, github tokens, cloudflare, and aws keys. “in most of the vulnerable projects we discovered during this research, the most common leakage is of github tokens, allowing an attacker to act against the triggering github repository. Below, we look at the risk profile of exposed credentials and secrets in public and private code repositories, how this attack vector has been used in the past, and what you can do to minimize your exposure.

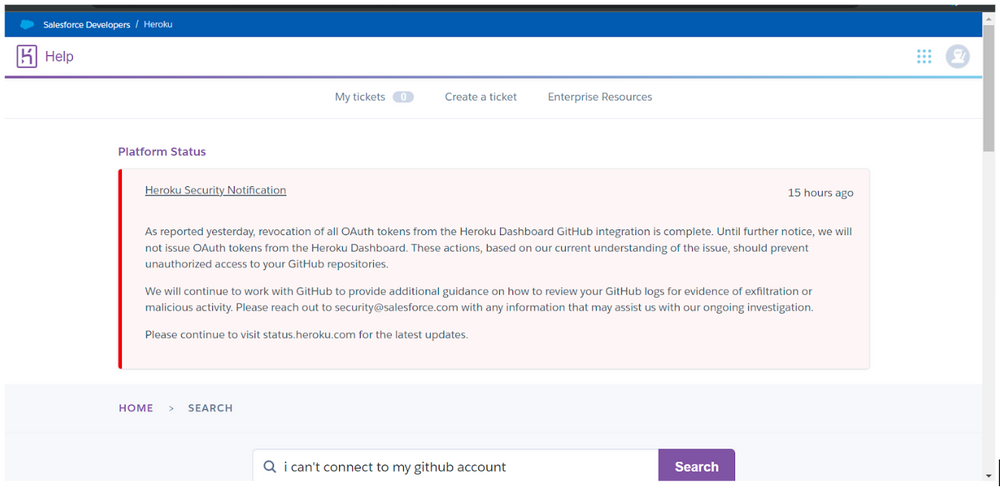
Malicious Actors Gain Access To Github Source Code Late last week, github disclosed that an unauthorized party breached its code repository. github itself wasn’t impacted, but the threat actor used compromised oauth tokens issued by two oauth integrators heroku and travic ci to download data of “dozens of organizations.”. A new supply chain attack on github, dubbed 'ghostaction,' has compromised 3,325 secrets, including pypi, npm, dockerhub, github tokens, cloudflare, and aws keys. “in most of the vulnerable projects we discovered during this research, the most common leakage is of github tokens, allowing an attacker to act against the triggering github repository. Below, we look at the risk profile of exposed credentials and secrets in public and private code repositories, how this attack vector has been used in the past, and what you can do to minimize your exposure.

Api Token Leaks On Github Kaspersky Official Blog “in most of the vulnerable projects we discovered during this research, the most common leakage is of github tokens, allowing an attacker to act against the triggering github repository. Below, we look at the risk profile of exposed credentials and secrets in public and private code repositories, how this attack vector has been used in the past, and what you can do to minimize your exposure.
Comments are closed.