How Hackers Clone Sim Cards Easily
Video Tutorial How To Clone A Sim Card Step By Step Minitool This video breaks down how sim cards work, why they're crucial for mobile security, and how cybercriminals exploit vulnerabilities to steal your identity and access sensitive accounts. Learn how hackers use sim card attacks to steal pii and compromise accounts—and how to protect against these growing cyber threats.
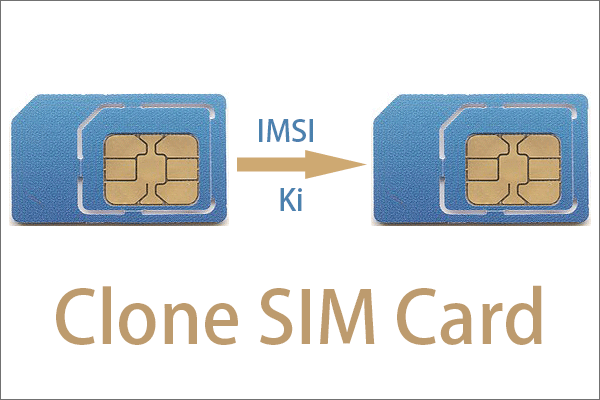
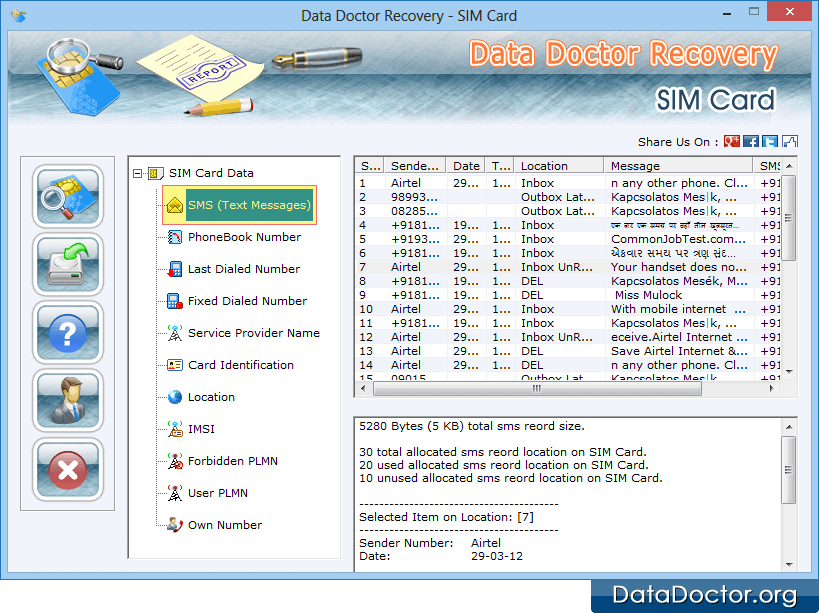
Video Tutorial How To Clone A Sim Card Step By Step Minitool Learn what sim cloning is and how it works. discover key risks associated with this fraud and explore effective ways to detect and prevent it. In this article, we’ll break down how hackers hack sim cards, what they can do once they’ve done it, and how you can protect yourself. we’ll cover the main techniques: sim swapping, sim cloning, and over the air (ota) attacks, plus some real world examples and tips to stay safe. At its core, sim cloning involves creating a duplicate copy of a subscriber identity module (sim) card, which is crucial for mobile communication. by doing this, a fraudster can impersonate the original sim card owner and gain access to their mobile services, calls, and texts. Sim cloning is one such technique where an attacker creates a duplicate sim card to gain unauthorized access to a victim’s mobile network, calls, messages, and even banking transactions. this leads to serious financial fraud, identity theft, and data breaches.
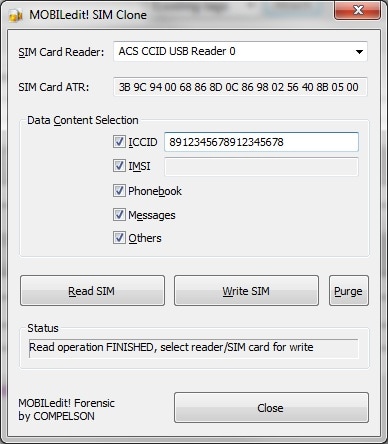
How To Clone Sim Card In Easy Steps Safe And Work Dr Fone At its core, sim cloning involves creating a duplicate copy of a subscriber identity module (sim) card, which is crucial for mobile communication. by doing this, a fraudster can impersonate the original sim card owner and gain access to their mobile services, calls, and texts. Sim cloning is one such technique where an attacker creates a duplicate sim card to gain unauthorized access to a victim’s mobile network, calls, messages, and even banking transactions. this leads to serious financial fraud, identity theft, and data breaches. In a sim clone attack, the hacker first gains physical access to your sim card and then creates a copy of the original. naturally, for copying your sim card, the hacker will first take out your sim from the smartphone, meaning this attack cannot be carried out entirely remotely. A cloned sim card seriously threatens your privacy because it allows bad actors to impersonate your mobile identity. by replicating sim credentials, someone else could make unauthorized calls, intercept sensitive messages, and receive two factor authentication codes for your accounts. Learn what sim cloning is, how attackers exploit it to intercept calls and sms, and why it remains a telecom security threat in 2025 despite stronger sim encryption. Attackers send fake banking alerts, otp requests, or package delivery texts. messages come from real local numbers, making them harder to block. why it’s possible: carriers often filter bulk sms from known gateways, but can’t easily block thousands of small sim cards each sending 50–100 texts.
Comments are closed.