How Hackers Bruteforce Login Pages Of Any Website

How To Hack Website Login Pages Brute Forcing With Hydra 18 21 Mp3 A brute force attack is a simple but effective technique where an attacker tries many username password combinations until one works. for website owners this often shows up as repeated failed login attempts, account lockouts, or unexplained spikes in server load. Brute force attacks work by calculating every possible combination that could make up a password and testing it to see if it is the correct password. as the password’s length increases, the amount of time, on average, to find the correct password increases exponentially.

How To Hack Website Login Pages Brute Forcing With Hydra 18 21 Mp3 Using tools like hydra, penetration testers can leverage brute force attacks to evaluate password strength. this comprehensive guide will cover cracking web logins with hydra‘s 30 protocol support on kali linux. In this article, we will explore two main types of attacks against login pages: brute force attacks and dictionary attacks. we will specifically focus on using hydra, a powerful tool for login hacking. In this ethical hacking tutorial, we’ll explore how hackers try to bypass login pages using brute force attacks and how you can defend your systems against them. Four beginner friendly website hacking techniques to try on your next pentest (with live “follow along” examples)!.
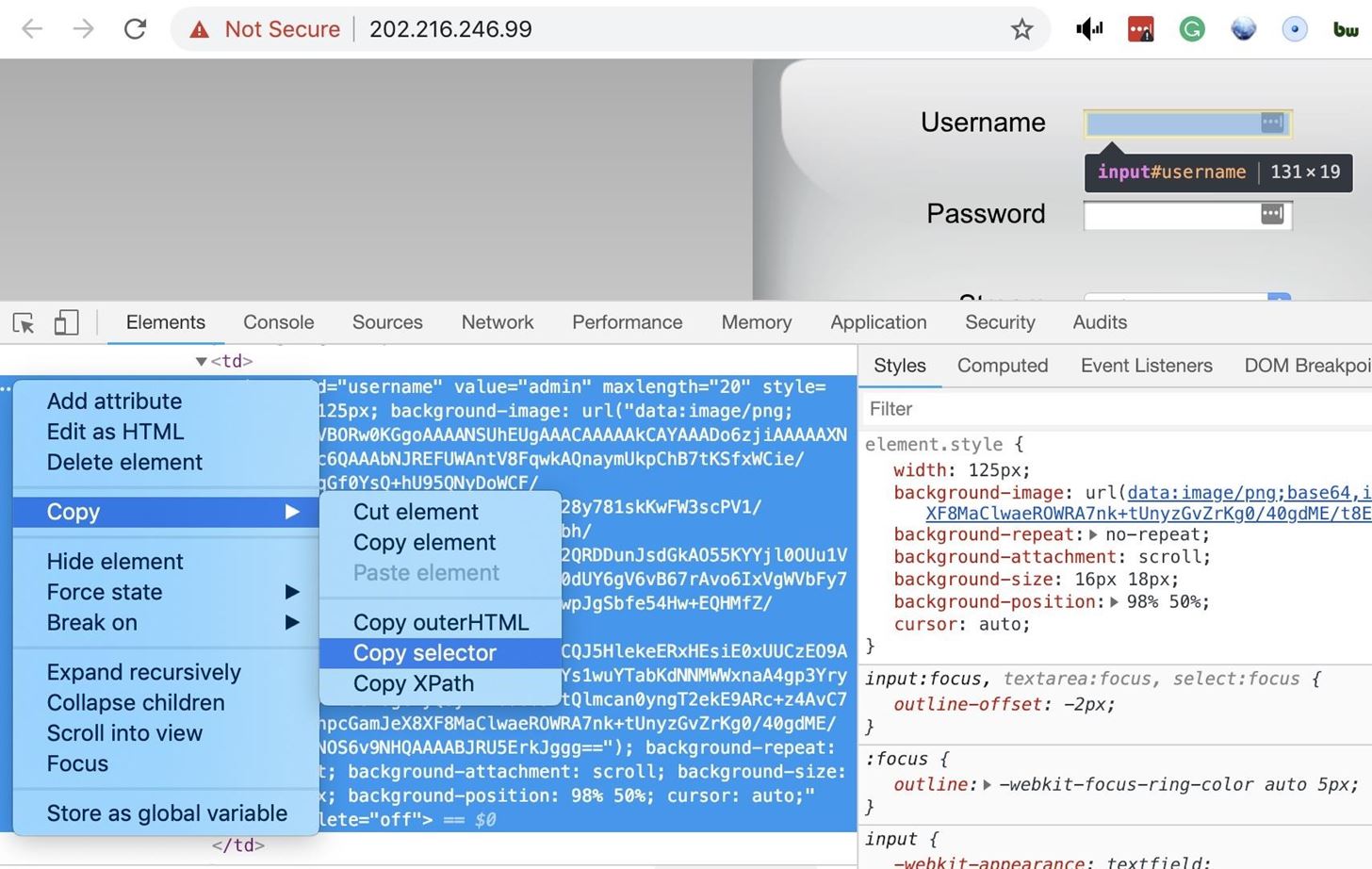
Brute Force Nearly Any Website Login With Hatch White Hats Hackings In this ethical hacking tutorial, we’ll explore how hackers try to bypass login pages using brute force attacks and how you can defend your systems against them. Four beginner friendly website hacking techniques to try on your next pentest (with live “follow along” examples)!. Brute force attacks are often used for attacking authentication and discovering hidden content pages within a web application. these attacks are usually sent via get and post requests to the server. In this video, i will be showing you how hackers use hydra to bruteforce a login page using php post method running on an http service. once again, the devices i used strictly belong to me and this video is for educational purposes only! and it doesn’t promote any unethical activity! enjoy!. Since we don't want to brute force all the usernames in combination with the passwords in the lists, we can tell hydra to stop after the first successful login by specifying the flag f. You can use brute force attack tools to penetrate any software, website or protocol that does not block requests after a few failed attempts. in the remainder of this post, we will examine some common brute force password cracking tools used for a range of different protocols.
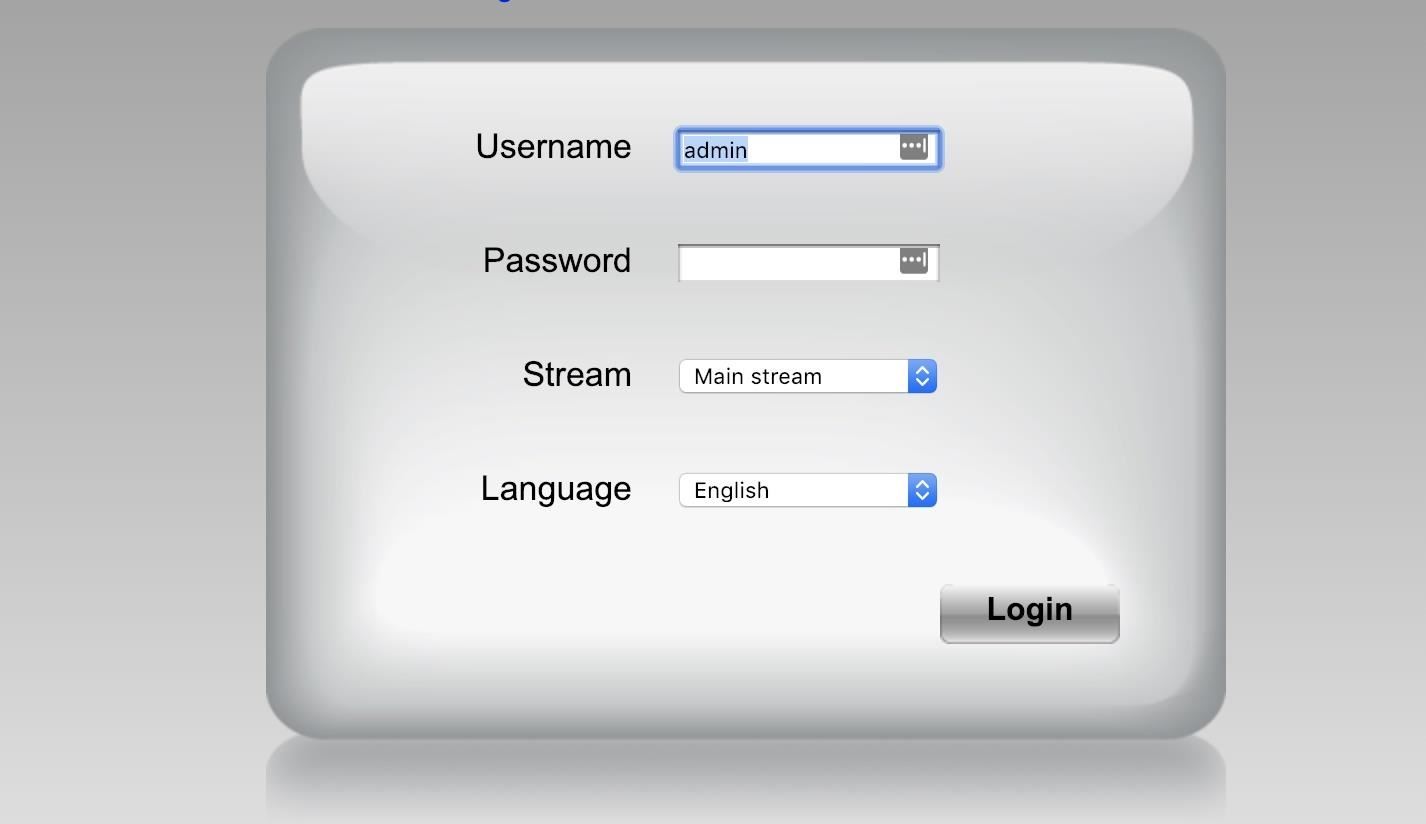
Brute Force Nearly Any Website Login With Hatch White Hats Hackings Brute force attacks are often used for attacking authentication and discovering hidden content pages within a web application. these attacks are usually sent via get and post requests to the server. In this video, i will be showing you how hackers use hydra to bruteforce a login page using php post method running on an http service. once again, the devices i used strictly belong to me and this video is for educational purposes only! and it doesn’t promote any unethical activity! enjoy!. Since we don't want to brute force all the usernames in combination with the passwords in the lists, we can tell hydra to stop after the first successful login by specifying the flag f. You can use brute force attack tools to penetrate any software, website or protocol that does not block requests after a few failed attempts. in the remainder of this post, we will examine some common brute force password cracking tools used for a range of different protocols.
Comments are closed.